Four vulnerabilities in Wago Web-Based Management (WBM) Systems were found to allow cross-site scripting attacks, set device parameters, remote code execution, etc.
CVE-2022-45140, CVE-2022-45139, CVE-2022-45138, and CVE-2022-45137, were the WBM vulnerabilities reported to Wago by Ryan Pickren from Georgia Institute of Technology’s Cyber-Physical Security Labs.
The WBM vulnerabilities can be exploited to harm critical infrastructure, control Wago Programmable Logic Controllers (PLCs), disrupt heavy machinery, and also pose a danger to the life of the engineers.

Researchers at Cyble Research and Intelligence Labs (CRIL) noted that globally, over 10,000 Wago WBM systems were exposed over the internet which posed a potential risk to systems that were not patched.
CRIL researchers found that maximum exposure to the internet which was not a reflection of vulnerable products was found in Italy, Turkey, and Germany. Some systems might have been patched among the exposed systems.
Details about the Wago Web-Based Management System (WBM) vulnerabilities
CVE-2022-45138 and CVE-2022-45140 were critical vulnerabilities in Wago. The former could be misused to skip authentication protocol for critical functions that can allow unauthenticated remote code execution. Moreover, this WBM vulnerability could offer full access, compromising the entire device’s security.
The exploitation of CVE-2022-45140 can also lead to full system compromise as there was no mechanism to stop unauthenticated access. It could be used to write arbitrary code to the storage with root privileges.
The medium vulnerabilities CVE-2022-45137 and CVE-2022-45139 although had limited impact on confidentiality and a small subset of confidential data, could be used with other flaws to increase the damage caused.
CVE-2022-45137 can allow XSS cross-site scripting attacks via the browser. CVE-2022-45139 would cause an origin validation error which was a CORS misconfiguration in the web-based management. It could allow a third-party webserver to exploit pages on the web server of the target.
If a threat actor combines this vulnerability in WBM with CVE-2022-45138, it could be used to gain information about the device including the CPU diagnostics.
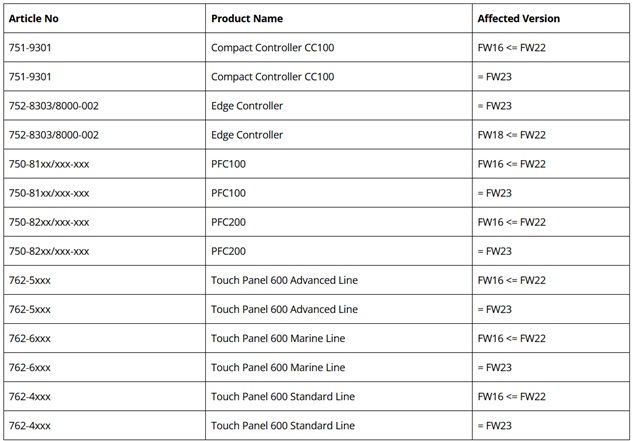
A list of the affected devices by the unpatched vulnerabilities in WBM are:
The latest firmware (FW22 Patch 1 or FW 24 or higher) was released by the official vendor which should be applied by users to guard against any possible exploitation in the future.
Further exploitation of the WBM vulnerabilities
As a finding, it was revealed that several asset owners have not changed the default factory login credentials. The default credentials can be found easily by threat actors either on device manuscripts or online which makes easy victims of threat actors.
The image below shows the staggering number of WBM instances that were working on default factory credentials:

CRIL also found that all information about the system including web server, number of tasks, project information, state, etc., can be stolen leading to misuses of specific project information. Moreover, the hostname, domain names, DNS server details, TCP configuration, etc., can also be read by cybercriminals.
They can make changes that can reflect immediately on the network. Cybercriminals can also edit the firewall settings posing a security risk to the ICS environment.
Heavy machinery can be caused to malfunction with also physical damage caused to them including the engineers around by altering the ICS environment.
To add to the damage, security tools can be manipulated by changing the settings of the firmware updates, passwords, service interface, and backup files.

Hacktivist groups have launched malicious campaigns exploiting exposed ICS including Wago, in the past. In operation Khanjar, a cybercriminal Thraxman targeted Russian factories in Crimea.




















































