After Onyx and Yashma ransomware variants, BlackSnake has become the latest offshoot of the Chaos ransomware strain, reported cybersecurity firm Cyble.
Extremely sophisticated and advanced, Blacksnake ransomware has already been used in several attacks, targeting a variety of organizations, including healthcare, finance, and government entities, according to Cyble.
The ransomware is reportedly being distributed through phishing emails and social engineering tactics.
Moreover, the peddlers of this malware were spotted selling it on data breach marketplaces too.
BlackSnake ransomware doesn’t bite Turkey, Azerbaijan
“The BlackSnake ransomware encryption process consists of several stages. In the first step, the malware employs a string_Builder() function to generate a 40-byte random string,” said the Cyble report.
“Next, it retrieves a pre-defined RSA public key that is hard-coded within the malware file. This key encrypts the previously generated random string, producing a key suitable for AES encryption.”
After obtaining the key, the malware utilizes the AES algorithm to encrypt all the files found in the directory, and then adds the generated key (encoded in base64) to the end of each encrypted file.
The sample with the hash e4c2e0af462ebf12b716b52c681648d465f6245ec0ac12d92d909ca59662477b has been subjected to static analysis, revealing that it is a 32-bit PE binary compiled using .NET. This information is presented in a figure.
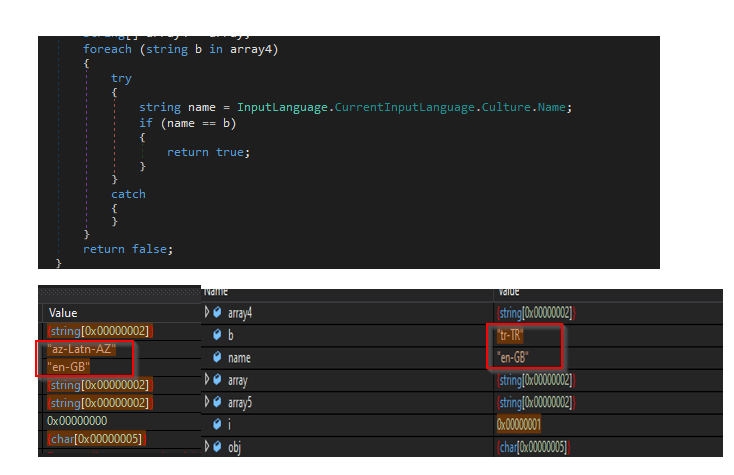
Once executed, the BlackSnake Ransomware carries out an initial check to determine if the system’s current input language matches the language codes “az-Latn-AZ” or “tr-TR.
If there is a match, the ransomware ends its operation, suggesting that the creators of BlackSnake ransomware have no intention of targeting systems located in Turkey or Azerbaijan, found Cyble researchers.
BlackSnake ransomware and choosy encryption
BlackSnake is said to have a unique encryption mechanism, making it difficult to detect and decrypt files. The ransomware also has the capability to evade security measures and disable antivirus software on infected systems.
Once a system is infected, the ransomware encrypts all files and demands a ransom in exchange for the decryption key.
The ransom note left behind by Blacksnake warns victims not to attempt to recover their files without paying the ransom, as doing so could result in the permanent loss of their data.
Interestingly, it avoids infecting devices that it has already bitten. According to Cyble, it may be an attempt to limit the impact of the ransomware.
“The BlackSnake ransomware has a method of detecting whether it has already infected a system. It does this by checking the location of the executing assembly with the path “C:\Users[user-name]\AppData\Roaming\svchost.exe”,” said the Cyble report.
“If this path matches, the ransomware continues to search for the file named “UNLOCK_MY_FILES.txt” in the %appdata% directory. Once the file is found, the ransomware will terminate itself.”
BlackSnake and Chaos: The origin story
Threat actors find it convenient to build on pre-existing ransomware codes for developing new ransomware families, noted Cyble.
“Onyx and Yashma ransomware families were already linked to the Chaos ransomware family, and the BlackSnake ransomware is another family now associated with the strain,” said the Cyble report.
“The Threat Actor has tweaked the Chaos ransomware source code and added a clipper module directly into the file, which is different from the usual approach of having a separate file for the clipper.”
A Breach Forum user with the alias “BlackSnakeTeam”, which joined the data breach forum in August 2022, has been found offering the ransomware strain, with a demand of only “15% of your profits”.
This is the only post the user has made on the forum, as on 10 March, 2023. Interestingly, a thread on Chaos ransomware builder was listed as a possibly related thread to the post.
Chaos was in the cybersecurity news recently, when a new, Go-based, multiplatform strain that bears no resemblance to its previous version came to light in September 2022.
“While analyzing the IP address of a staging server hosting additional modules, we noted it had an abnormal self-signed certificate that displayed the organization name of “Chaos”,” said a threat assessment report by Black Lotus Labs, the threat intelligence division of Lumen Technologies.
“We then searched for IP addresses with similar self-signed certificates that contained the word “Chaos” in the organization name and discovered 15 active nodes at the time.
The earliest certificate was generated on April 16, 2022; we assess this was when the Chaos activity cluster was first launched in the wild,” the report added.