Passwords are a way to secure online accounts against hacking and prevent unwanted access to malicious actors. A strong password can avert or completely stop cyberattacks. Maintaining password hygiene and creating strong passwords are essential to keep accounts safe.
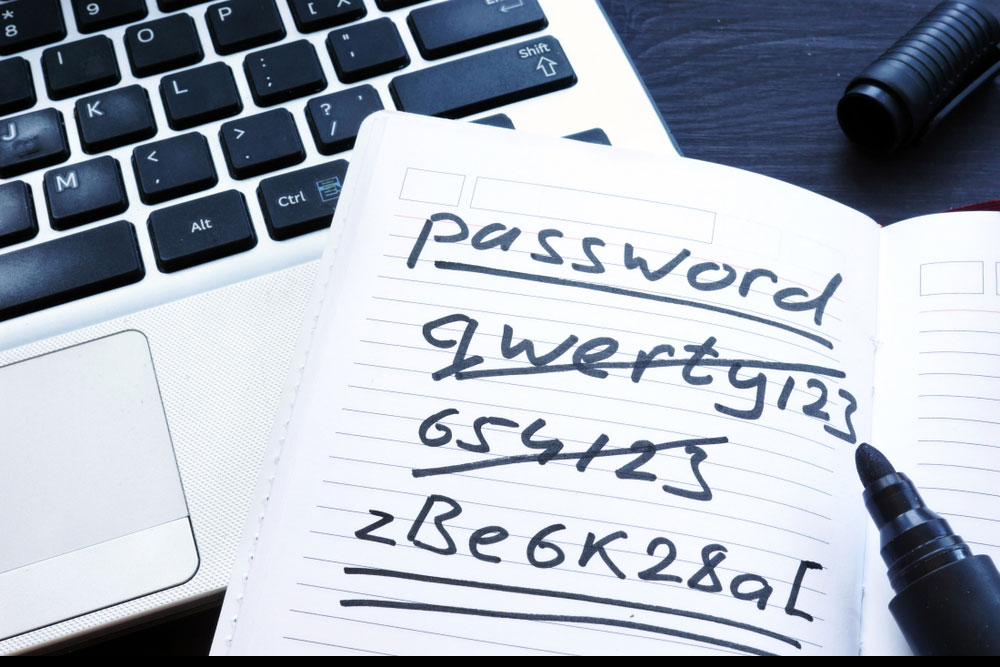
However, creating a strong password can be tricky. People tend to keep simple passwords so they can easily remember them. Welcome, abc123, password, 12345, iloveyou, tomcat, 111111, Qwerty, admin, and princess are among the easiest passwords kept by people, and hackers are aware of this. Most websites ask users to create a strong password that combines uppercase and lowercase letters, numbers, and alphanumeric characters. Still, many accounts get easily hacked.
What is password hygiene?
Cyber hygiene practices include keeping passwords safe to protect online data from being stolen or misused. It is a part of maintaining and safeguarding passwords to avoid misuse of user data. A hacker can access a user’s online data through stolen credentials or hacking using the weakest passwords. Basic password hygiene principles help avoid cybercrime and compromise of one’s online information.
Practices like creating strong passwords by following standard password-making protocol and regularly changing passwords can help maintain password hygiene. Not punching one’s password openly so it is not visible to others and not noting down one’s password on sticky notes and placing them near the device are among best practices in maintaining password hygiene.
Data theft techniques
Hackers use various tools to hack accounts like a keylogger that logs keystrokes and trojan horses that offer the desired file type for free while employing the malware to steal system data. Hacking and remote administration tools connect to the victim’s system and capture what is on their screen. Statistics state that about 81% of company data breaches occur due to poor passwords, 80% of hacking was done using stolen and reused login credentials, and about 555 million stolen passwords have been posted on the dark web since 2017. Another research states that 59% of users reuse their passwords in all their personal and professional accounts. Offices can use advanced technology to secure their passwords, like Enterprise Password Manager (EPM).
Creating strong password
Whether passwords are for personal accounts or professional accounts, it is advised to use strong passwords that have a minimum of 12 characters; a 14-character password is considered vital, passwords that are not repeated on other accounts, a combination of letters that do not form actual words, has a variety, characters and numbers and one that does not include the account holder’s first, middle or last name.
The National Cyber Security Center (NCSC) suggest that users must create a password that has three random words. This would make the account less vulnerable. Using password generators is found difficult to be reproduced by hackers.
Passphrases in place of passwords
A passphrase is known to be more challenging to crack than cracking a password. Passphrases are longer than regular passwords, with a minimum of 15 characters. They usually have 22 characters and contain upper-case and lower-case letters, numbers and at least one punctuation character. A passphrase never includes words relating to the user’s personal information. Passphrases have better chances of not getting hacked. Users can use passphrase generators, too, as their apps generate complex passphrases.
Staying secure with one-time passwords
One-time passwords (OTP) are a great way to avoid having a single password or passphrase that could be hacked. One-time passwords expire within a few seconds or minutes and thus cannot be used by another person to hack into accounts. Moreover, OTPs are sent on a device like a phone or via emails, limiting the account’s audience. The benefit of relying on OTPs is not having to remember a long password. A time-bound password sent to an account or device adds another protection layer.
Changing passwords
Regularly changing passwords is a good habit to secure one’s accounts from hacking attempts and those who keep a tab on someone’s online history. Cybersecurity experts argue that changing the password every 2-3 months is safe. It is upon the user’s discretion to change their passwords if they notice any suspicious activity online. Not sharing password details with anyone is a must, or it can reach unwanted hands even through trusted contacts. If one must share their password during an emergency, changing the password again soon after the work is done is advised.
Jotting down passwords
Remembering passwords can be a task, especially when one has more than one account. Not making a note of the password on the same device or account is advised as it leaves room for easy access to confidential credentials. Making sticky notes of passwords makes the user vulnerable to hacking that may or may not be done with malicious intent. Being lazy in creating and remembering a strong password is among the reasons for data theft.
Additional security features
Using a security question if this option is available can increase online protection. However, it is essential not to use a question-and-answer sequence that the user’s contacts can predict. Random answers to questions can distract hackers and leave them astray. Changing the security question over a few months is also a smart practice, especially if one sees unread emails showing as ‘read’ in the account. Multi-factor authentication is also a secure way to create a password that qualifies as a strong password by following the three criteria. The criteria include using biometrics like fingerprint, iris or facial recognition, an email address to log in, a username and password combination, or a pin.
Two-step verification
Some other measures to secure online accounts are using the two-step verification option. Also called two-factor authentication, this method requires authenticating login attempts using a connected device. It can be activated on select websites and devices using the “Security” option in the account. Users are sent prompts whenever someone tries to log in to their device. Upon receiving the prompt, the user can allow or deny login. Opting for receiving login notifications on another device is a great way to keep a tab on login attempts. Moreover, some accounts also have the feature of showing how many devices that account logged into. Users can log out if they see a device they don’t recognize. Showing login time is also a feature some websites offer. It is worth the while of a user to investigate specific features and options websites provide to secure their accounts. Most websites are directed by authorities and cybersecurity regulations to update their security protocol. An alert user must look for all these options to secure their online accounts and data.
Using password generator
Using applications to generate passwords is an excellent way to avoid using common words that come naturally to the user. Password generators can create complex passwords that users can use. It shows password strength to help users decide if they want a stronger password from what was generated. Since password generators use a pseudo-random algorithm that uses a sequence called ‘seed’ to create random and unrelatable passwords, users are offered passwords that they have rarely used.
There are several ways a user can do to prevent hacking and data theft. Creating a strong password for every account and changing them when something seems amiss is judicious. Creating a strong password is not just required to protect login credentials and user information but also to safeguard savings in the bank and investments.