The University of Oklahoma published a notice informing staff and students that it has suffered a security breach.
This breach was also due to the ongoing exploitation of organizations using the MOVEit file transfer services. The University of Oklahoma cyber attack was through the third-party vendors of the institution who used MOVEit services.
The University of Oklahoma cyber attack and MOVEit
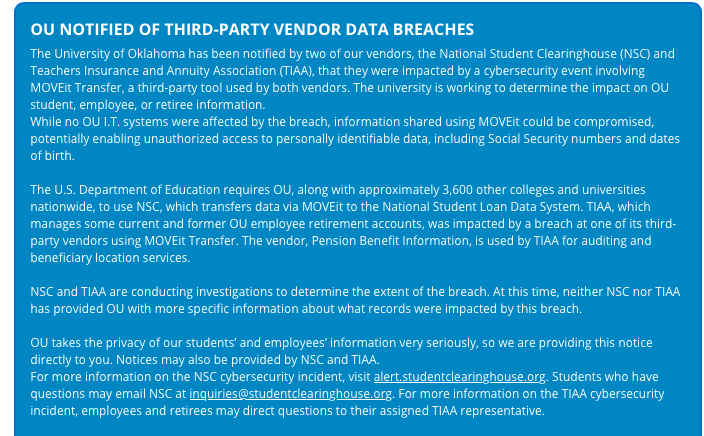
Threat Analyst, Brett Callow tweeted about the University of Oklahoma cyber attack with the above screenshot which said that the university was indirectly impacted by the MOVEit cyber attack.
The two vendors of the university that led to its breach were the National Student Clearinghouse (NSC) and Teachers Insurance and Annuity Association (TIAA).
The MOVEit cyber attack together with the two third-party vendors used by schools has impacted 17 schools so far, according to Brett’s investigation. 299 organizations have been found to be impacted by MOVEIt besides 41 US schools.
Overall, an estimated 18,154,787 individuals’ data has been compromised in the MOVEit cyber attack in the hands of the Cl0p ransomware group. The group has gotten its hands on hundreds of clients of file transfer providing services nearly since 2020.
Cl0p ransomware group with FIN11 group launched a cyber attack on Accellion’s legacy file transfer appliance in 2020. This gave them access to data related to hundreds of its clients. In 2023 it was reported that Cl0p breached GoAnywhere MFT to have similar benefits.
Impact of the University of Oklahoma cyber attack
All the data shared using MOVEit is expected to be likely exposed to Cl0p hackers, the notice by the University of Oklahoma read. This could include personally identifiable information of students including their Social Security Numbers, and date of birth.
It was assured that none of the IT systems of the university were breached. The University of Oklahoma with nearly 3,600 colleges and universities is required to use NSC to transfer data through MOVEit.
This information then goes to the National Student Loan Data System. “TIAA, which manages some current and former OU employee retirement accounts, was impacted by a breach at one of its third-party vendors using MOVEit Transfer,” the notice said.
Ransom payments have been increasing this year with reports naming cybercriminal groups extorting money for data exfiltrated from them. BlackBasta, Cl0p, ALPHV, and LockBit were among the highest-paid cybercriminal groups with Cl0p making $1.7 million on average.
In the year 2021, a figure of nearly $940 million was reached in ransom payments with the toll having reached over $449 million until June this year. In the first half of 2023, the revenue from ransom payments for hackers increased by 90% as compared to 2022.
Organizations are urged to avoid making ransom payments however, with their systems held inactive victims feel helpless and give in.
As a Cyble blog noted, organizations must prepare against similar cyber attacks in the future proactively. They must have tool ad teams to monitor third-party security requirements. The need for an incident response team was recommended.
Universities and other organizations can conduct cybersecurity awareness training so they can take necessary actions at first sight of any suspicious activity. Basic cyber hygiene of not opening suspicious or unexpected emails from unknown and spammy contacts must be avoided.
A limit of data access through the Identity and Access Management policy and Data Loss Prevention is necessary to prevent threats and unauthorized access.





















































