While India’s Punjab police is preoccupied with the ongoing search operation for Khalistani separatist Amritpal Singh and his aide Papalpreet Singh, it may have to divert their attention to a cyber attack on the police department by hacker collective Eagle Cyber Crew.
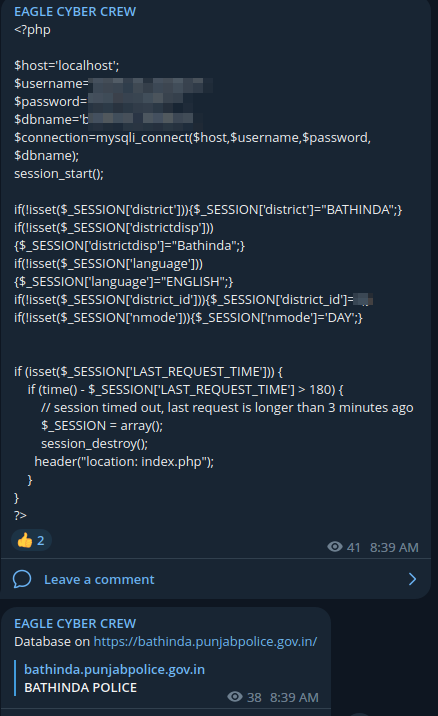
During routine threat monitoring, security researchers at Cyble Research and Intelligence Labs (CRIL) identified a Telegram post discussing the security breach of the Punjab police website. Cybercriminal group Eagle Cyber Crew claimed the attack stating that they had gained access by exploiting a Local File Inclusion (LFI) vulnerability.
Following the attack on the police department, the group defaced a few of the official websites. The websites were accessible post the Punjab Police security breach. The attack could not have come at a worse time as the department is busy dealing with the ongoing unrest in the Indian state.
The Cyber Express has reached out to the Punjab police to confirm the security incident but is yet to receive a response from them.
Punjab police attacked

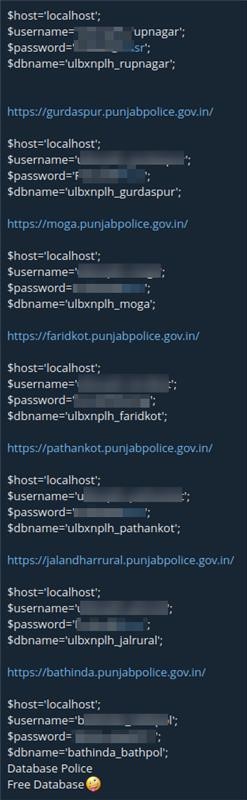
Researchers from CRIL confirmed that the hacktivist group managed to access MySQL configuration files from the subdomain of ‘punjabpolice.gov.in.’ They leaked internal configuration files from various subdomains after the Punjab Police website was hacked.
This security breach of the Punjab Police website exposed login credentials, including the usernames and passwords of database users.
Cybercriminals can use stolen login credentials to log in to websites and steal more personal data, which can be further misused. It poses a risk to full names, emails, and contact details, including addresses and numbers specified by users.
Speaking about the Punjab Police data leak, CRIL researchers told The Cyber Express, “Threat actor group Eagle Cyber Crew claimed on their Telegram channel to have compromised public-facing web infrastructure of the Punjab Police, India.” Eagle Cyber Crew exploited the Local File Inclusion (LFI) vulnerability.
After the Punjab Police was attacked, access to backend files from other digitally connected provincial websites of Punjab was compromised.
Eagle Cyber Crew leaked internal configuration files from its sub-domains after the Punjab Police was attacked:
- Amritsar Police
- Bhatinda Police
- Faridkot Police
- Gurdaspur Police
- Jalandhar Rural Police
- Mansa Police
- Moga Police
- Pathankot Police
- Sangrur Police
- Sri Muktsar Sahib Police
- Rupnagar Police
Punjab Police attacked by Eagle Cyber Crew
The Telegram channel associated with the Eagle Cyber Crew was created on December 2, 2022. “The self-proclaimed hacktivist group claimed to be based in Malaysia,” CRIL researchers added.
Eagle Cyber Crew works with other hacktivist groups from Bangladesh, Indonesia, Pakistan, Palestine, Sudan, Vietnam, and Yemen. They are on a campaign against India and Israel called ‘#opsjentikramadhan.’
Mitigation of the Local File Inclusion vulnerability
It is essential to maintain the security of the websites so hackers cannot take advantage of the Local File Inclusion vulnerability. Exploitation in Local File Inclusion is done by injecting an infected code into the targeted server page.
The following best practices are recommended to prevent exploitation:
- Securing file paths by keeping them hard-coded so they cannot be appended directly.
- Limiting acceptable characters if an administrator needs dynamic path concatenation.
- Setting a limit on the API to admit only from a directory to prevent directory traversal attacks.