In 1982, Elk Cloner, the first malware, was detected in a Mac device. From then on, malware attacks have continued to increase and become more sophisticated. With over 10 million malware attacks witnessed within a year, it is imperative to have a robust team of experts working on malware analysis and detection.
Malware analysis and detection techniques include employing a malware honeypot, machine learning behavioral analysis, or using Nmap to help detect and mitigate it.
The first stealth virus, ‘Brain’ capable of hiding itself, was found in the 1990s, followed by others with increased capabilities. Now, nearly 560,000 new malware is detected every day, which makes analysis of the same a tedious task for the forensic department.
Evolution of malware and its detection techniques
Traditionally, malware analysis is done mostly manually however, new tools and techniques come in handy in faster research of the software. Efficient malware analysis helps in creating malware detection and prevention software.
Static analysis, dynamic analysis, and reverse engineering are some of the methods or stages of malware analysis and detection techniques. It unfolds the type, functionality, and impact of malicious software that may be a virus, worm, ransomware, or Trojan.
The time taken for malware analysis is increasing with features added to newly found samples on a regular basis. However, apt malware analysis and detection techniques are essential to curb its spread and threat.
Here are the most commonly used malware analysis and detection techniques
Static Malware Analysis
Static malware analysis is the study of malicious software without having to execute it (in a safe environment.) This is a fairly manually performed task that involves understanding the source code of the malware to find the data structure and used functions.
Otherwise, the found data gets lost when the source code gets compiled into a binary executable. Some types of static malware analysis are –
- File fingerprinting – It involves testing it and conducting operations on the file including the computation of a cryptographic hash. This malware analysis technique helps find whether it was modified and if it has any similarities with its counterparts.
- Disassembly – Here, the machine code is reversed using tools to assembly language like IDA Pro. The reconstructed assembly code is then used to find the program logic and intended malicious function as programmed by its developer.
- AV scanning – AV scanners help detect if the malware binary belongs to the more commonly used ones.
- File format – To find the magic number of the UNIX systems to determine the file type and find the file type, the metadata of the malware is examined.
- Packer detection – Static analysis is hindered by the loss of metadata of malware which is often obfuscated using a packer. To prevent this loss during the packing process, unpackers such as PEiD2 can help to some extent in examining the malware.
Dynamic Malware Analysis
Dynamic analysis is the study of a file in its execution process. The malware is run in a safe environment to understand its malicious capabilities. A benefit of dynamic analysis against static analysis is that it offers the observation of the actual behavior of the software during runtime and when it unpacks itself.
Moreover, extra detailing is offered in terms of its analysis as this process is largely automated. However, the ‘dormant code’ allows monitoring only one execution path offering incomplete code coverage.
Following are the two main types of dynamic malware analysis –
- Analyzing the malware between defined points – Upon executing the malware for a specific time frame, the changes to the system are monitored from start to end.
- Monitoring runtime behavior – It is simply the monitoring of the malware during runtime using specialized tools. Some of the malware analysis tools are Anubis, CWSandbox, and Norman Sandbox.
Machine learning and deep learning techniques for malware analysis
Malware evolved from ‘ILOVEYOU’ in 2000, which attacked millions of Windows-based devices to ‘Anna Kournikova’ which infected with emails. Malware detection also went through an overhaul.
A malware analysis and detection technique using Machine Learning Algorithms soon came to the fore. To thoroughly gauge the workings of a Polymorphic malware that can change its signature to evade detection, machine learning techniques were created. These techniques offer a high detection ratio with clear results measuring false positives and false negatives.
It also uses models to detect malware behavior including Bagging, Gradient Boost and AdaBoost, MLP classifier, Hybrid Model, and Restricted Boltzmann Machine model. It offers different levels of accuracy in understanding malware features along with losing valuable data in runtime.
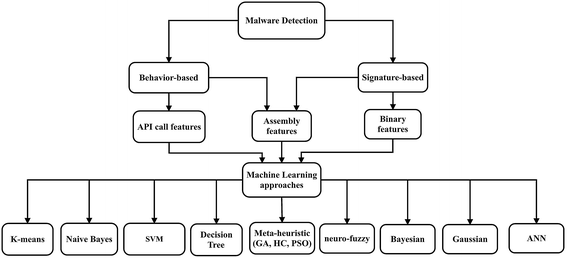
Data mining techniques using machine learning approaches for malware analysis and detection
Data mining involves two broad approaches namely the signature-based detection and behavior-based detection of malware. It is a machine-learning method for detecting malware. It works on malware and benign examples.
-
Signature-based malware detection technique
The signature-based detection method focuses on conducting static investigations for learning the code-structure of the infection chain. For this the method looks for interruptions against a predefined set of known assault capabilities.
Although this method follows a thorough execution pattern it is not considered the best detection method as it misses important functions of the malware while working on standard marks covered by portable malware.
-
Behavior-based malware detection technique
Behavior-based malware detection technique requires running it in a sandboxed environment to check it during runtime. It offers better results of how the malware was created and developed to run on a machine. Following the dynamic analysis method, malware is monitored for its malicious features by its code and structure.




















































