A previously patched vulnerability is still being exploited on the Redis servers. According to research by Aqua Nautilus, the deliberately vulnerable CVE-2022-0543 Redis honeypots were found, which were exploited using malware written in Golang or go programming language.
The Go-based malware Redigo impacts remote dictionary servers or Redis servers using the critical vulnerability CVE-2022-0543 that has a severity base score of 10.0, according to a report by the National Vulnerability Database. This vulnerability can allow Redigo to launch several attacks using commands such as:
- INFO – This command collects information about the Redis server, whether it is vulnerable to CVE-2022-0543- or not.
- SLAVEOF – This command helps adversaries to create a replica of the attacking server to help them download the shared object and exploiting CVE-2022-0543.
- REPLCONF – This command helps establish a connection between the attacking server and the created replica of the server.
- PSYNC – This command helps run the stream of commands coming from the attacking server. The replicated server runs it. By running this command, the replica also gets updated and gets the shared library exp_lin.so downloaded to itself.
- MODULE LOAD – A module from the dynamic library is loaded which was downloaded in stage 4 at runtime. Arbitrary codes are run in this stage using the downloaded library.
- SLAVEOF NO ONE – In this attack, the replication stops and changes the Redis server to a master server.

Redis impacts Debian and Debian-derived Linux distributions using the CVE-2022-0543 flaw. This flaw was patched in February 2022 however, it is still exploited in the wild using the publicly available proof-of-concept exploit code. It attacks initiates after finding the Redis server exposing port 6379. It becomes easier for cybercriminals to evade detection by simulating Redis communications on this port. Its indicators of compromise details are as follows:
- a755eeede56cbce460138464bf79cacd
- c3b9216936e2ed95dcf7bb7976455859
Researchers are speculating about the launch of a denial-of-service (DDoS) attack using botnets and running cryptocurrency miners in this campaign besides stealing server data. Redigo malware went undetected in Virus Total by all vendors.
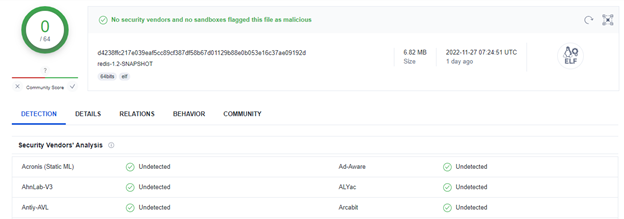
Virus Total did not show Redigo as malicious or suspicious. It makes the command-and-control server messages appear like legitimate Redis communication. It was named Redigo because researchers found the use of this malware written in the Go language was targeting Redis servers.
Redis is an open-source in-memory database that was released to offer help with real-time applications to send files sooner. It uses a cache to store data in its memory and caters to millions of requests in a short time.





















































