From stealing personal information to blackmailing individuals, threat actors have often found ways to profit from malicious products.
Yet again, hacker forum users were found using the platform to sell malware. While one user was selling Android Stealer, the other was attempting to sell source code.
Android Stealer on sale
According to the post, the user has been promoting the sale of an Android stealer that can compress images from a victim’s phone and send them to the user through a Telegram bot.
The app is easy to use and does not require any hosting or domain, making it an attractive tool for anyone looking to steal photos from Android devices.

The app’s creator has also promised to customize its name and icon to meet the buyer’s needs, making it even more appealing.
However, the app does require storage permission to work, meaning the victim must grant permission for the app to access their phone’s storage.
This is a crucial detail that potential buyers must keep in mind. If the app does not receive the necessary permissions, it cannot steal the images.
Source code for sale
Another user of the forum user is selling the source code to a stealer that can collect sensitive data like passwords and cookies, take screenshots, and gather information about the victim’s computer.
The post on the forum states that the stealer has been completely rewritten from scratch and is written in C++ over .NET, with no dependency on the .NET version.
The stealer is also designed to run on Windows 7 to Windows 11 and works with a server on sockets through its protocol over TCP.
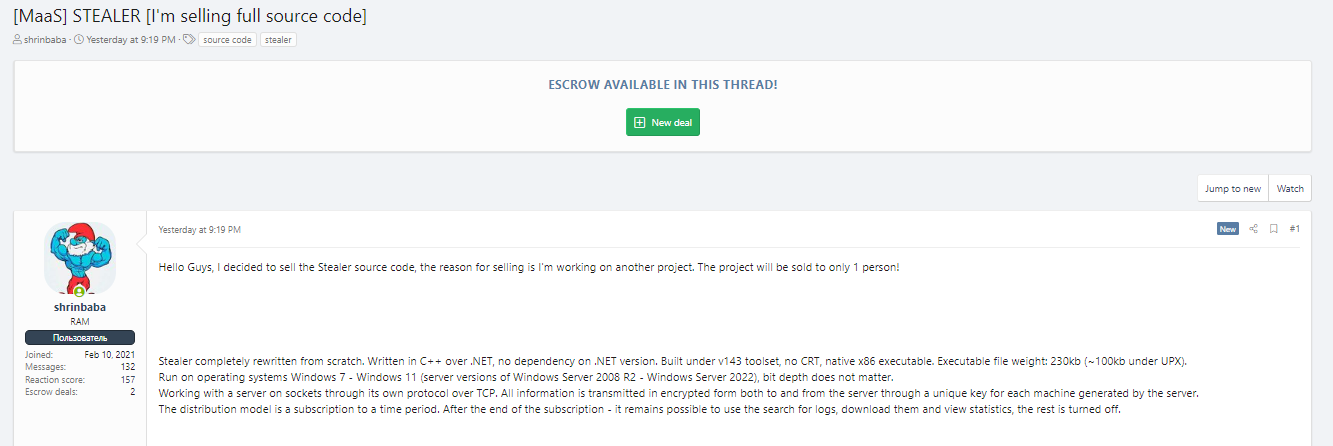
All information is transmitted in encrypted form to and from the server through a unique key generated by the server for each machine. The distribution model for this stealer is a subscription to a period.
While these hackers offer their tools for a low price, their actions can cause significant harm to their victims.
The Android photo stealer, for instance, can be used to blackmail individuals, steal personal information, or damage someone’s reputation.
The source code stealer, on the other hand, can collect sensitive data that can be used to gain access to bank accounts or other online accounts.
In conclusion, selling these tools on the hacker forum is just another reminder of the constant threat cyber criminals pose.
It’s essential to stay vigilant and take proactive steps to protect yourself from these attacks. By staying informed and taking the necessary precautions, you can keep your personal information and devices safe from harm.




















































