Experts at Cyble Research and Intelligence Labs (CRIL) found a new Android banking trojan ‘Zanubis’. The cybersecurity company shared its report after analyzing several malware strains like Hydra, Ermac, Amextroll, and others. However, the new trojan appeared to be in a different league than others, as it targeted over 40 applications from Peru, all while hiding and using “Zanubis” as a key to decrypt responses received from the Command and Control (C&C) servers.
Cyble’s report on Zanubis
Credit: Cyble Research and Intelligence Labs (CRIL)
According to the report, the malware appeared to be a standard PDF document used regularly in offices, banks, government organizations, and educational institutions. At the time the report was published, the malware-injected files had targeted banks in Peru and two social media apps WhatsApp and Gmail. The cybersecurity company did an in-depth analysis of Zanubis, and here is a quick look at the lucid version of the report.
Technical analysis of Zanubis
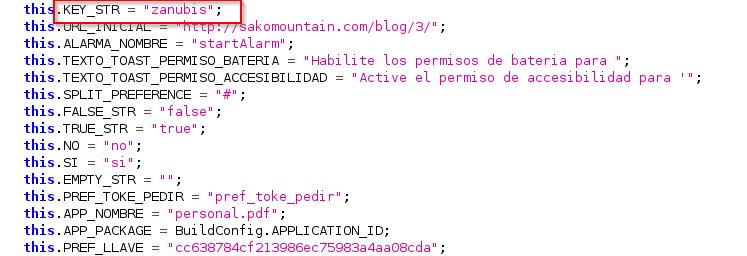
While analyzing the malware, the research team decoded some of the samples from the TA, including a file named “Personal.pdf,” which had a package name “com.personal.pdf” and a 64-digit alphanumeric SHA256 Hash code.
Credit: Cyble Research and Intelligence Labs (CRIL)
The application had 30 permissions in the manifest file (a file/document containing metadata for a group of accompanying files that are a part of a coherent uni). Out of these permissions, Zanubis was able to exploit 10 of them.
Here are the ten permissions that the TA exploited:
- READ_CONTACTS
- RECEIVE_SMS
- READ_SMS
- CAMERA
- READ_EXTERNAL_STORAGE
- RECORD_AUDIO
- WRITE_EXTERNAL_STORAGE
- CALL_PHONE
- SEND_SMS
- SYSTEM_ALERT_WINDOW
These permissions included some of the basic functionality of the devices — something that should not be compromised as it allows the TA to access internal files, manipulate them, delete them, and even snoop sensitive information from the target devices.
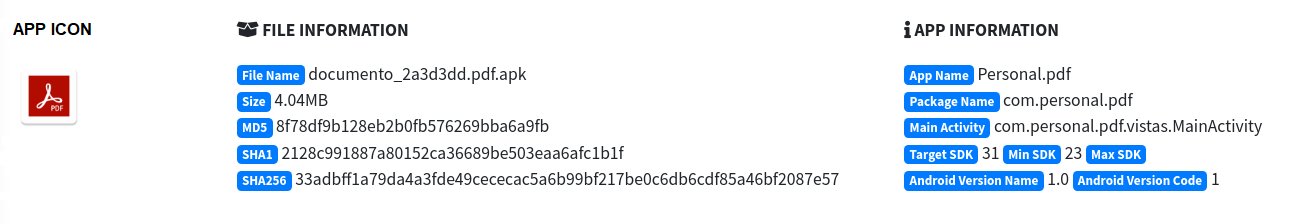
Analysis of Zanubis source code
Credit: Cyble Research and Intelligence Labs (CRIL)
For the uninitiated, a source code is a collection of strings of words, numbers, letters, and symbols that a computer programmer uses to create executable applications. Malware, trojans, Android applications, and even the operating systems they are built on, uses a source code to produce a result using logic embedded in the code.
Zanubis, as a trojan, also had a source code, which was reviewed to see how it operated and what algorithms it used in its operations. Cyble did a test run of the malicious program and found out that the malware first prompts the users to grant Battery Optimization access, followed by the use of a11y (accessibility or practice of making web applications more usable for people with limited physical and mental abilities).
The report mentioned that the malware connects to a Command and Control server ‘hxxp://92.38.132[.]217:8000’ and receives the list of applications and its overlay URL. It then uses all the permission on the target device. Once the user turns on the ‘Accessibility Service’, the malware prevents the system from deactivating and turns on all the permissions on the target device.
After receiving all the required details, the malware begins decrypting the response and saves the files with a .xml extension named “cc638784cf213986ec75983a4aa08cda.xml. After that, it scans through the information on the target device and sends the list of installation applications, contacts, SMS permission status, and other information to the original perpetrator via the C&C server.