Have you ever woken up to a message demanding money in exchange for access to your computer? This isn’t a scene from a dystopian movie; it’s the chilling reality of ransomware, a form of cyber extortion that has become a major threat in today’s digital world.
Ransomware has become a pervasive cyber threat, wreaking havoc on individuals and businesses alike. According to a 2023 report by Cybersecurity Ventures, global ransomware damages are projected to reach a staggering $265 billion by 2031!
These attacks not only cause financial losses but can also disrupt critical operations, damage reputations, and even pose legal and regulatory challenges. But what is ransomware? How exactly does it work? Who are its common targets? And most importantly, how can you defend yourself from becoming the next victim? In this article, we’ll discuss these things in detail.
What is Ransomware?
Ransomware is a malicious software program, or malware, specifically designed to hold a victim’s data or device hostage. Imagine a digital kidnapper – ransomware encrypts your crucial files, databases, or even locks you out of your entire system. The attacker then demands a ransom payment, typically in cryptocurrency, in exchange for the decryption key or regaining access.
Ransomware has become a significant threat in the digital age, causing billions of dollars in damages and disrupting businesses and individuals alike.
Types of Ransomware
There are two main types of ransomware, each employing a different tactic to extort victims:
- Crypto-Ransomware (Encryptors): This is the most prevalent and well-known strain. Crypto-ransomware encrypts a victim’s valuable data, rendering it inaccessible. This could include essential documents, photos, financial records, or entire databases. The attacker then demands a ransom payment, typically in cryptocurrency, for the decryption key – the only way to unlock the files and regain access.
- Locker Ransomware: This variant doesn’t encrypt files but rather locks the user out of their entire device or system. Imagine being blocked from your desktop screen, with a ransom note prominently displayed, demanding payment to regain control. While less sophisticated than crypto-ransomware, it can still be disruptive, especially for businesses relying on constant system access.
In recent years, cybercriminals have upped their game, developing more intricate strains that combine techniques:
- Data Stealing Ransomware: This advanced variant goes beyond encryption. It not only encrypts your files but also steals sensitive data before locking the system. This adds another layer of pressure, as the threat of leaked information can be even more damaging than data inaccessibility. Imagine the potential consequences of stolen customer records, financial data, or internal communications being exposed.
- Triple Extortion Ransomware: This is the most ruthless form of ransomware, taking the attack a step further. In addition to encryption and data theft, attackers may threaten to leak the stolen data or launch denial-of-service (DoS) attacks against the victim’s network. A DoS attack overwhelms a network with traffic, making it inaccessible to legitimate users. This multi-pronged approach aims to cripple the victim’s operations completely, forcing them to pay the ransom to recover.
How Does Ransomware Work?
The inner workings of ransomware can be broken down into distinct stages, outlining the attacker’s strategy from initial infection to extorting the victim. Here’s a closer look at the ransomware attack lifecycle:
1. Infection
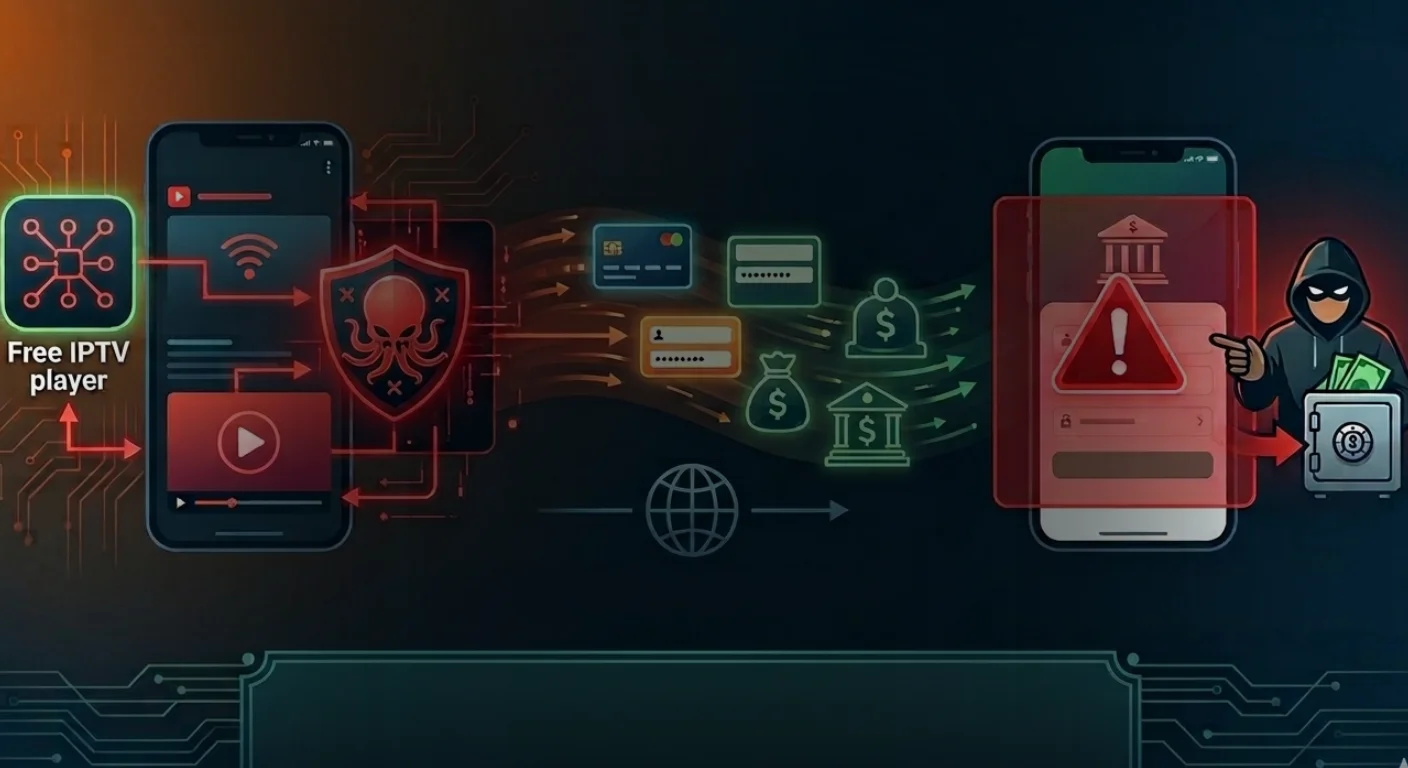
The initial infection can occur through various methods, with phishing emails being a prevalent tactic. These emails often contain malicious attachments disguised as legitimate documents or links that, when clicked, unknowingly download the ransomware onto the victim’s device.
Unintentional visits to compromised websites can also trigger drive-by downloads, where the ransomware infects the system without any user interaction. Additionally, ransomware can spread through vulnerabilities in outdated software or operating systems. Attackers constantly scan networks for weaknesses they can exploit to gain access and deploy the ransomware.
2. Delivery and Reconnaissance
Once downloaded, the ransomware program establishes itself on the victim’s device. It then begins scanning the system for valuable targets. This might include documents, databases, financial records, photos, or any other data deemed crucial for the victim’s operations.
3. Encryption
The ransomware employs a complex encryption algorithm to scramble the targeted files. This process essentially renders the files unreadable and inaccessible, effectively locking the victim out of their own data. The encryption strength varies depending on the specific ransomware strain.
4. Ransom Note
After encrypting the data, the ransomware delivers its message. A ransom note typically pops up on the screen, informing the victim about the attack and outlining the attacker’s demands. This message usually includes:
- The extent of the attack: It explains which files have been encrypted and the consequences of not complying.
- The ransom amount: The attacker specifies the ransom amount they demand in exchange for the decryption key.
- Payment method: Cryptocurrency like Bitcoin is often the preferred payment method due to its anonymity.
- Deadline: The attacker might set a deadline for payment, pressuring the victim into a hasty decision.
5. Communication (Optional)
Some ransomware strains may incorporate a communication channel, allowing the victim to contact the attacker to negotiate the ransom or ask questions. However, it’s important to remember that you’re communicating with a cybercriminal. There’s no guarantee of a successful resolution, and engaging with them might even encourage further attacks.
What Are the Effects of Ransomware on Businesses?
A ransomware attack on a business can be a crippling blow, causing a domino effect of disruptions and financial losses. Here’s a closer look at the potential consequences businesses face when hit by ransomware:
- Data Loss or Inaccessibility: The core function of ransomware is to encrypt or lock down critical data. This can render essential documents, financial records, customer information, intellectual property, and operational databases unusable. Depending on the severity of the attack and the availability of backups, the loss of data can significantly hinder day-to-day operations and potentially lead to permanent data loss.
- Financial Loss: The financial ramifications of a ransomware attack can be substantial. Businesses may be forced to pay hefty ransom demands to regain access to their data. This financial burden can be compounded by the costs associated with:
- Incident Response: Engaging cybersecurity professionals to investigate the attack, eradicate the malware, and restore systems.
- Downtime: Ransomware attacks can cripple business operations for extended periods, leading to lost productivity, revenue opportunities, and potential customer churn.
- Reputational Damage: A successful ransomware attack can severely damage a company’s reputation, especially if sensitive data gets leaked. Customers and partners might lose trust in the organization’s ability to safeguard their information.
- Legal and Regulatory Issues: Businesses operating in certain industries or handling sensitive data might face legal and regulatory repercussions depending on the nature of the data compromised in the attack. Failure to comply with data protection regulations can result in hefty fines and penalties.
- Operational Disruption: Beyond data inaccessibility, ransomware attacks can disrupt crucial business processes. Production lines might grind to a halt, communication channels could be severed, and access to essential applications could be blocked. This widespread disruption can have severe consequences for a company’s ability to function effectively.
- Erosion of Employee Trust: A ransomware attack can create a sense of unease and distrust among employees. They might be concerned about the security of their own personal data or feel frustrated by the disruption to their work. Effective communication and post-attack recovery efforts are crucial to rebuild employee trust and confidence.
Common Ransomware Targets
While no one is immune to a ransomware attack, cybercriminals often target specific entities with the potential for greater disruption and the possibility of extracting a higher ransom payout. Here’s a closer look at some of the most frequent targets:
- Businesses: Organizations of all sizes, from small startups to large corporations, are attractive targets due to their reliance on critical data for daily operations. This data could include financial records, customer information, intellectual property, or internal communications. Disrupting access to this data can significantly hinder business continuity and cause significant financial losses.
- Healthcare Organizations: Hospitals, clinics, and other healthcare providers are prime targets for ransomware attacks due to the sensitive nature of the data they handle. Patient medical records, financial information, and research data are all valuable assets that attackers can exploit. A successful ransomware attack on a healthcare organization can not only disrupt critical medical services but also put patients’ health at risk by delaying diagnoses or treatments.
- Government Agencies: Government agencies at all levels, from local municipalities to national institutions, are vulnerable to ransomware attacks. These attacks can disrupt essential public services, such as tax collection, social security programs, or emergency response systems. Additionally, ransomware attackers might target government agencies to steal sensitive data related to national security or classified information.
- Educational Institutions: Schools and universities are increasingly becoming targets for ransomware attacks. Attackers may be lured by the vast amount of data stored on university servers, including student records, faculty research, or administrative data. Disrupting access to these systems can cause significant delays in academic schedules, research projects, and administrative processes.
- Critical Infrastructure Providers: Organizations responsible for critical infrastructure, such as power grids, water treatment plants, or transportation systems, are also at high risk. A successful ransomware attack on such an entity could have catastrophic consequences, disrupting essential services and potentially causing widespread damage.
Why Is Ransomware Spreading?
The alarming rise of ransomware attacks can be attributed to a confluence of factors that create a lucrative environment for cybercriminals and make organizations and individuals more susceptible:
- Increased Reliance on Digital Data: Our dependence on digital data for business operations, personal information, and communication has created a vast pool of valuable targets for attackers. Businesses of all sizes store sensitive information electronically, making them prime targets for attacks that exploit data accessibility.
- Rise of Cryptocurrency: The emergence of cryptocurrency like Bitcoin has provided a perfect payment method for ransomware attackers. Cryptocurrency transactions are anonymous and relatively untraceable, allowing attackers to operate with a degree of impunity. The ease and speed of transferring cryptocurrency further incentivize this criminal activity.
- Profitability: Ransomware has become a highly profitable business for cybercriminals. The potential for large ransom payouts, coupled with the relatively low risk of getting caught, makes ransomware a lucrative venture. Ransomware attacks can be automated and launched at scale, further increasing the potential returns for attackers.
- Evolving Tactics: Ransomware attackers are constantly innovating their tactics. They exploit new vulnerabilities in software and operating systems, develop more sophisticated encryption methods, and even employ psychological manipulation in their ransom notes to pressure victims into paying.
- Lack of Cybersecurity Awareness: Many individuals and organizations still lack adequate cybersecurity awareness. This includes falling for phishing scams, failing to update software regularly, and neglecting basic security measures like strong passwords and multi-factor authentication. This creates exploitable weaknesses that attackers can leverage to gain access to systems and deploy ransomware.
- Globalized Threat Landscape: The rise of cybercrime as a global industry means ransomware attacks can be launched from anywhere in the world. This makes it difficult for law enforcement agencies to track down and prosecute attackers, further emboldening them.
Why You Shouldn’t Pay Ransomware
While the urge to pay a ransom to regain access to your data might be strong, here are some reasons why it’s generally not recommended:
- No Guarantee of Decryption: There’s no guarantee that paying the ransom will result in receiving the decryption key. You’re essentially trusting a cybercriminal to keep their word, which is a risky proposition.
- Encourages Further Attacks: Paying a ransom incentivizes attackers and fuels the development of more sophisticated ransomware strains. It signals that the tactic is profitable, making you and others more likely to be targeted again.
- Security Risks: Ransomware payments are often made in cryptocurrency, which can be traced back to the victim’s wallet. This could expose them to further attacks or identity theft.
- Legal and Regulatory Issues: Depending on the type of data encrypted, there might be legal or regulatory consequences associated with paying a ransom.
How to Protect Yourself From Ransomware?
Here are some crucial steps to safeguard yourself and your organization from ransomware attacks:
- Implement Strong Backups: Regularly back up your critical data on a separate, secure system, preferably offline. This ensures you have a clean copy to restore in case of an attack.
- Update Software and Systems: Regularly update your operating system, software applications, and firmware to patch security vulnerabilities that attackers might exploit.
- Educate Employees: Train employees on cybersecurity best practices, including identifying phishing emails, avoiding suspicious websites, and the importance of strong passwords.
- Phishing Email Awareness: Implement email filtering solutions and educate employees to recognize phishing attempts. Employees should be cautious of unsolicited emails, especially those with attachments or suspicious links.
- Network Segmentation: Segment your network to minimize the potential damage if a device gets infected. This can prevent ransomware from spreading laterally across your entire network.
- Strong Passwords and Access Control: Enforce strong password policies and implement multi-factor authentication (MFA) to add an extra layer of security to user accounts.
- Security Software: Utilize reputable antivirus and anti-malware software to detect and prevent ransomware infections.
- Incident Response Plan: Develop a comprehensive incident response plan outlining the steps to take in case of a ransomware attack. The plan should include data recovery procedures, communication protocols, and reporting guidelines.
By following these defensive measures, you can significantly reduce the risk of falling victim to a ransomware attack. Remember, prevention is always better than cure.
How to Detect Ransomware?
Early detection of a ransomware attack is crucial for minimizing damage and facilitating a faster recovery. Here are some signs that might indicate a ransomware infection:
- Unusual File Activity: Notice a sudden increase in disk activity, especially file encryption processes.
- Inaccessible Files: Important files become inaccessible or unusable.
- Suspicious Pop-Up Messages: Ransom notes demanding payment typically appear on the screen.
- System Slowdown: The overall performance of your device or network might slow down significantly.
- Unknown Applications: Unfamiliar applications running in the background could be signs of malware infection.
Key Takeaways
- Ransomware encrypts or locks your data, demanding a ransom payment for access.
- Businesses are prime targets due to their critical data and potential disruption caused by an attack.
- Paying the ransom is discouraged. There’s no guarantee of decryption, and it fuels further attacks.
- Back up your data regularly, keep software updated, and train employees on cybersecurity best practices to defend against ransomware.
- Early detection is crucial. Watch for unusual file activity, inaccessible files, ransom messages, and system slowdowns. Isolate the infected device, disconnect it from the network, and seek professional help if you suspect a ransomware attack.
FAQs
What is ransomware in simple words?
Ransomware is a type of malicious software that encrypts files or locks a user out of their device, demanding a ransom for access restoration.
Is ransomware A virus?
No, ransomware is not a virus but a specific type of malware designed to extort money from victims.
What is an example of a ransomware attack?
An example of a ransomware attack is the WannaCry attack in 2017, which affected hundreds of thousands of computers worldwide.
What are the two main types of ransomware?
The two main types of ransomware are encrypting ransomware, which encrypts files, and locker ransomware, which locks users out of their devices.
Can you remove ransomware?
It is possible to remove ransomware, but it can be challenging, and prevention is often the best defense.