Researchers have found a new strain of ransomware, dubbed “Underground Team”. The Underground Team ransomware strain not only encrypts files but also lists victims’ host information in the ransom note.
Unlike the regular extortion demands, the Underground Team ransomware note offers help in spotting network vulnerabilities and recommendations for information security.
The specific victims targeted by the Underground Team ransomware strain remain unknown, said researchers at Cyble Research and Intelligence Labs (CRIL).
According to the researchers, there have been no reported instances of data leaks associated with this ransomware.
Underground Team ransomware: Deep dive
The Underground Team ransomware is made with Microsoft Visual C/C++ and runs on 64-bit systems.
When it infects a computer, it carries out various actions such as deleting backup copies of your files, changing settings in the computer’s registry, and stopping a specific database service called MSSQLSERVER.
To achieve these actions, the ransomware uses specific commands. For example, it uses a command to delete the backup copies of your files stored on your computer. By doing this, it makes it harder for the user to recover files.
It also uses a command to adjust the settings related to remote desktop sessions, which can impact how the computer is accessed remotely.
Additionally, it forcefully stops the MSSQLSERVER service, which can disrupt the functioning of a particular type of database.
After that, the ransomware looks for the drives and file systems on your computer. It does this by using certain functions provided by your operating system. Once it identifies the drives, it drops a ransom note called “!!readme!!!.txt” in various folders on the computer.
Next, the ransomware starts searching for files and directories to encrypt. It does this by scanning through them one by one. However, it excludes certain filenames, file extensions, and specific folders from the encryption process.
Once the files are identified, the ransomware encrypts them, making them unreadable. However, it doesn’t change the names of the encrypted files or add any new extensions.
Underground Team ransomware: Encryption and negotiation style
After the encryption is complete, the Underground Team ransomware creates a file called “temp.cmd” and runs it. This file is designed to delete specific files, clear event logs, and remove itself from your computer. It does this to hide its presence and cover its tracks.
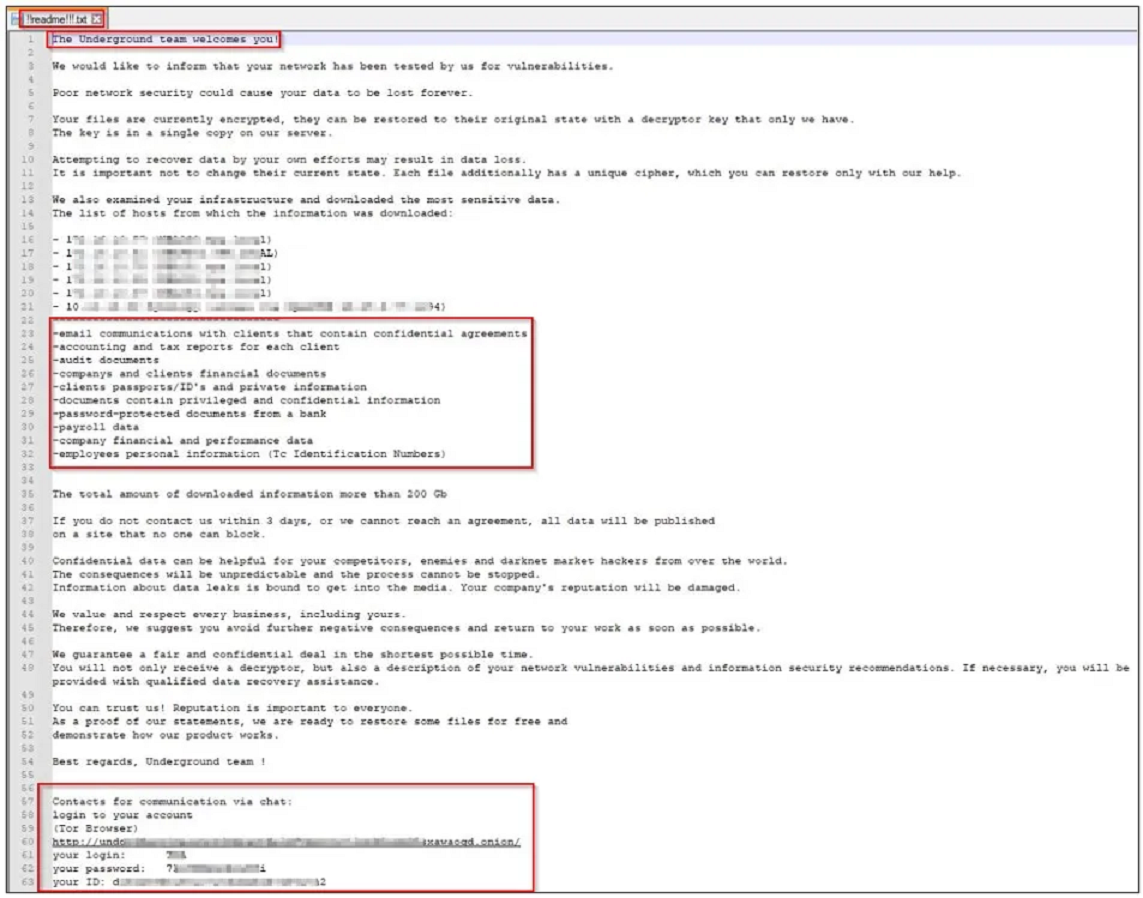
The ransom note left by the ransomware instructs the user to contact the attackers for help in recovering your encrypted files or to pay the ransom.
“The ransom note of the Underground Team ransomware introduces novel elements that distinguish it from typical ransom notes. In addition to guaranteeing a fair and confidential deal within a short timeframe, the group offers more than just a decryptor,” said the CRIL report.
The note provides an Onion URL, which is a way to access a chat platform to communicate with the attackers. This platform looks like a ticketing system, allowing you to negotiate with the attackers about the ransomware incident.

“It promises to provide insights into network vulnerabilities and recommendations for information security. Furthermore, qualified data recovery assistance will be extended to the victims if required,” the report said.
“While these novel additions showcase a broader approach by the ransomware group, it is imperative to continue exercising caution and skepticism when evaluating such claims.”
Ransomware mitigation: Begin with the basics
Although the operating style is different, attacks by the Underground Team ransomware strain can be averted to a great extent with some general security practices, CRIL researchers told The Cyber Express.
These include conducting regular backups and keeping them offline or in a separate network, enabling automatic software updates on all devices, using reputable anti-virus and internet security software, and exercising caution when opening untrusted links and email attachments.
“Over time, malicious actors have adjusted their ransomware tactics to be more destructive and impactful and have also exfiltrated victim data and pressured victims to pay by threatening to release the stolen data,” said a CISA advisory on ransomware protection.
“These ransomware and associated data breach incidents can severely impact business processes by leaving organizations unable to access necessary data to operate and deliver mission-critical services,” it said.
“The economic and reputational impacts of ransomware and data extortion have proven challenging and costly for organizations of all sizes throughout the initial disruption and, at times, extended recovery.”
In the event of a ransomware attack, users must disconnect infected devices from the network, detach external storage devices if connected, and inspect system logs for any suspicious events, advised CRIL researchers.






















































