The financially motivated Stormous Ransomware group allegedly launched a ransomware cyberattack on Fichtner Water & Transportation, a Stuttgart, Baden-Württemberg based engineering firm. Following the alleged Fichtner Ransomware Attack, the Ransomware Gang has threatened to leak financial information, plans, drawings, project details, etc.
The Fichtner ransomware attack
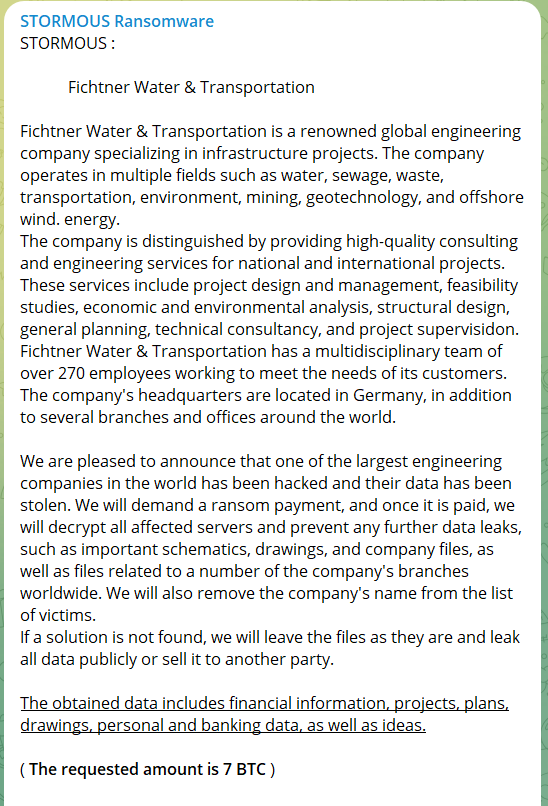
With a small description of the Fichtner water and transportation company, the ransomware group wrote that it would demand a ransom. And if the company fails to comply, will leak important schematics, drawings, and files from its worldwide branches.
The Stormous ransomware group telegram post about the Fichtner data breach read that the gang will decrypt the affected servers once the ransom of 7 BTC was paid. They also wrote that further leaks will be prevented after the ransom demands are met.
“If a solution is not found, we will leave the files as they are and leak all data publicly or sell it to another party,” the Telegram post about the Fichtner ransomware attack concluded.
After the alleged Fichtner ransomware attack, the website is accessible. The Cyber Express reached out to Fichtner water and transportation, however, we haven’t received a response yet.
About Fichtner water and transportation
Fichtner water and transportation has several branches globally including in Peru, Turkey, Afghanistan, Vietnam, etc. The company provides engineering and consulting services in the areas of energy management, and process engineering, globally.
The Fichtner group has over 1,800 staff forming a transdisciplinary team that works in geotechnics, offshore wind power, traffic, transport, etc. It has nearly 270 experts at nine locations throughout Germany.
Stormous ransomware group
The Stormous ransomware group has pledged allegiance to Russia in the past. The group also created a poll asking participants to vote for which company it should target next. The polling results pointed towards Coca-Cola which received 72% of the votes.
Coca-Cola suffered a security breach while the Stormous ransomware group claimed to have stolen 161 GB of data from the former.
According to a press release by the beverage giant dated March 8, 2022, it suspended its business in Russia. “Our hearts are with the people who are enduring unconscionable effects from, these tragic events in Ukraine,” the press release said.
The Stormous ransomware group has also been known to target several Indian entities including Delhi Heights School Success Neeti, and Fycis Software for Nidhi Banking among others.