A nefarious threat actor who identifies themselves as LeakBase, Chucky, Sqlrip, and Chuckies, on various underground forums, released a massive trove of databases containing the PII information of 16 million Indians who use the Indian government’s Swachh City platform, an initiative of the government’s Ministry of Housing and Urban Affairs.
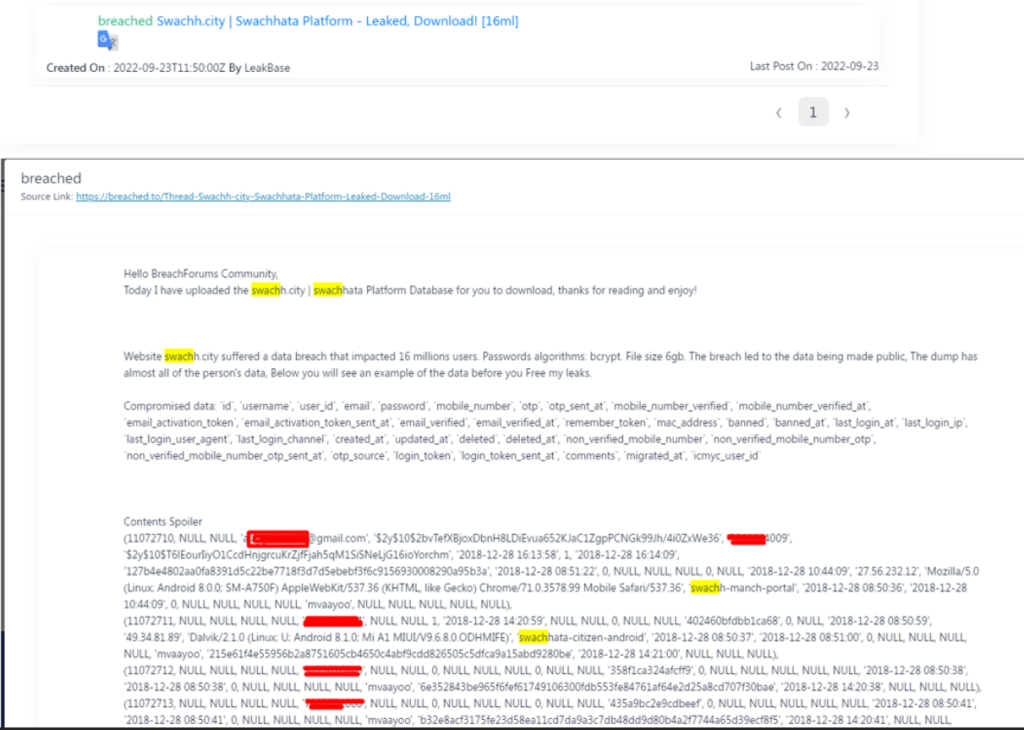
Researchers at Cyble Research and Intelligence Labs analysed the data collected from the Swachh City platform after the malicious actor posted a detailed report on the Dark Web. They were able to extract various details about the users.
According to Cyble, the compromised data includes:
`id`, `username`, `user_id`, `email`, `password`, `mobile_number`,
`otp`, `otp_sent_at`, `mobile_number_verified`,
`mobile_number_verified_at`, `email_activation_token`,
`email_activation_token_sent_at`, `email_verified`, `email_verified_at`,
`remember_token`, `mac_address`, `banned`, `banned_at`,
`last_login_at`, `last_login_ip`, `last_login_user_agent`,
`last_login_channel`, `created_at`, `updated_at`, `deleted`,
`deleted_at`, `non_verified_mobile_number`,
`non_verified_mobile_number_otp`,
`non_verified_mobile_number_otp_sent_at`, `otp_source`, `login_token`,
`login_token_sent_at`, `comments`, `migrated_at`, `icmyc_user_id`
The researchers discovered the leaked database through Cyble’s Threat Intelligence platform on September 23, 2022. It was posted on a public forum BreachForums, which has recently taken over from Raidforums after the FBI seized it. “We were validating this information. It was an alleged leak of the Swachh City platform that we found earlier this week and have completed our validations,” Cyble Researchers told The Cyber Express.
Not only the details of the web users of Swachh City were compromised, but even the database of the users who downloaded the Indian government’s Swachhata-MoHUA app on iOS and Android were victims of the data breach,” the researchers noted.
Often for financial gain, LeakBase operates as an online retailer on the Dark Web. It also conducts sales on its forum, and researchers warned that the leaked information could be used by criminals to carry out advanced attacks. In addition, close to 1.25 GB of the leaked database was reportedly hosted on a popular file-sharing platform.
The attacker’s origin is relatively unknown, but researchers believe it is a Russian language operator from the analysis of the codes. They also noted that the threat actor had been targeting the Indian government lately.
How did the actor carry out the attack on Swachh City?
It is led to believe that the TA may have had access to PHPMyAdmin, “Our Cyber Threat Intelligence Platform captured a compromised administrator account of their phpAdmin account on April 11, 2022,” noted Cyble Threat Researcher. This is supported by the TA’s recent initiative of selling accesses for various panels, including cPanel, Joomla, phpMyAdmin, and others.

The Cyber Express team observed the screenshot of the alleged access to the ‘PHPMyAdmin’ page, which suggests that the threat actor most likely compromised an employee’s machine and used their stolen credentials to breach their systems.
Cyble researchers further shared compromised ‘admin’ and ‘root’ level accounts that have likely led to the breach of their system.
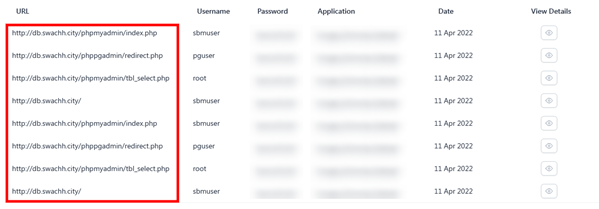
The Cyber Express team hasn’t validated the credentials themselves. However, the alleged access screenshot shared by the TA with Cyble researchers points towards the likely case of an internal machine and account compromise. Meanwhile, users can find out if their data has been compromised by checking their credentials and data on amibreached.com.