Ashutosh Yadav, 20, had the fright of his life when he realized that he had lost ₹152,000 ($1,840) to scamsters – the money he thought was safely deposited in a bank under the Indian government’s grand banking inclusion plan CSC Bank Mitra. Scamsters siphoned off the money with the spoof website of an Indian government project.
The youth from rural central India, who runs a computer training center in his hometown, saw nothing suspicious when he logged in to the official portal of the Common Service Centers (CSC). The fake CSC Bank Mitra website appeared legit enough to fool even a computer literate like Yadav.
The amount, minuscule compared to the scams that hog cybersecurity news, is a year’s savings for a family that earns hardly $500 a month. “I took the money from my father’s savings and lost it,” Yadav told The Cyber Express.
Police records in the business-rich Indian state of Maharashtra alone show that Yadav is one among the thousands duped by scamsters who tapped the opportunity
Financial Scams in the Guise of CSC Bank Mitra
CSC Bank Mitra, the ambitious banking inclusion plan floated by the Indian government under the Common Service Centers (CSC) Scheme, has established over 8,500 customer service points or kiosks to facilitate rural Indian entrepreneurs in extending basic banking services to unbanked consumers across semi-urban and rural India.
Village Level Entrepreneurs (VLEs) are registered under the CSC scheme to deliver various government and non-government schemes from the CSC outlets. To be part of the scheme, a VLE must undergo a registration process on the portal register.csc.gov.in and submit documents to ascertain their eligibility.
Yadav described that he got tricked into sending money because he saw a completely identical website to the original one. He sent the money to fraudsters this year between June and July.
In August 2022, open-source researchers at cybersecurity company Cyble were informed by an outreach contact about this ongoing financial fraud operation.
“In this particular scam, the entrepreneurs intending to acquire a Customer Service Point (CSP) were directed by the fraudsters to visit and register on a fake website “ecscgov.co.in”, posing as an official portal for the Common Service Centers (CSC) Scheme by MEITY, India,” read the Cyble Research Intelligence Labs (CRIL) blog post on their enquiry of the situation.
According to the researchers, unsuspecting consumers have no way of identifying genuine CSP business correspondents, and this ambiguity is exploited by several unverified VLEs operating their websites and portals that pretend to offer CSP Kiosk setup services. They have been duping consumers since the inception of the government-backed Digital India scheme to benefit rural parts of India, found the researchers
“The Common Service Centers (CSC) might be aware of ongoing fraud operations. It is concurrent with the fact that there were several consumer complaints against similar fraud schemes followed by a ticker notification published on the official website csc.gov.in addressing Village Level Entrepreneurs (VLEs) to verify their credentials,” read the blog post
CSC Bank Mitra, a low-hanging fruit
CSC Bank Mitra is one of classic examples of public-facing schemes that aimed for popularity at the cost of scrutiny and security, making it a low-hanging fruit for scamsters in all garbs, from data brokers to money swindlers.
The Cyber Express in October found that archived customer data of Indian private and public sector banks, from SBI to HDFC and ICICI, have been made available on the dark web, suspected to be leaked from one of the Bank Mitra scheme websites.
In August 2022, researchers uncovered a scheme has been apparently duping and scamming rural consumers in India in the name of CSC Bank Mitra. Similar to the present case, trusting customers were at the risk of being duped by fraud CSP business correspondents.
Tip of the iceberg
Nivrrutti Bavaskar, a Police Sub-inspector at the North Cyber Police Station in Mumbai, told The Cyber Express that he has become adept at spotting the mode of operation of such scamsters because of the number of such cases that he sees frequently. The loose chink, in most of the cases, is the spoofed website itself, he pointed out.
“Scammers often create a duplicate page and not an entire website. A legit website will have multiple pages linked to it that will have related content. However, a spoofed page or website may have a single-page, with a form-like structure that is shown to victims in order to fill in their credentials.”
Anyone facing such a site must scroll through the page or website to its social media pages, he recommended. More often, scammers may not have their official social media handles linked. Also, it can help to check if the website starts with the URL – https. The ‘s’, which stands for secured, will be missing in most of the fraudulent websites, he added.
Details related to the fraudulent transactions
- Spoofed website address: http://www.ecscgov.co.in/
- Mobile numbers of the imposters: +91-7699197820, +919163270984, +918292684046, +918902247758
- The scammers’ mobile numbers had their number registered as a WhatsApp Business.
- Email addresses: [email protected] and [email protected].
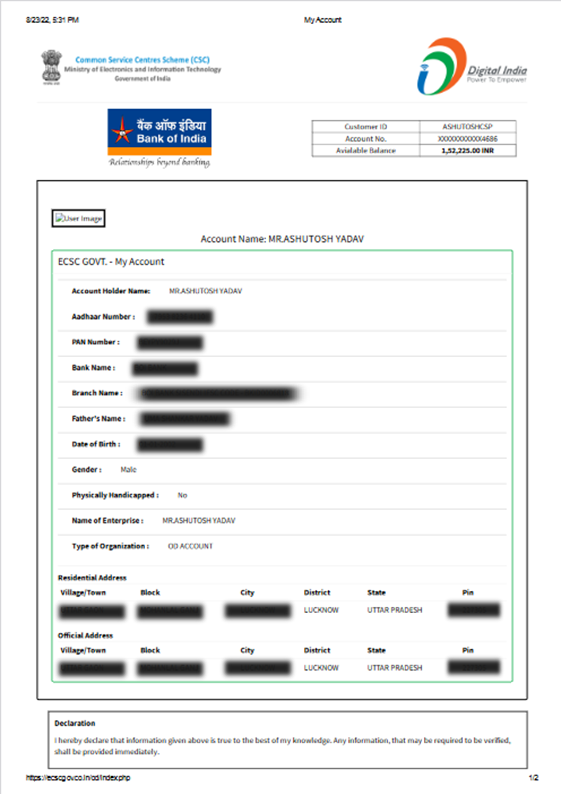
- Bank payment document:
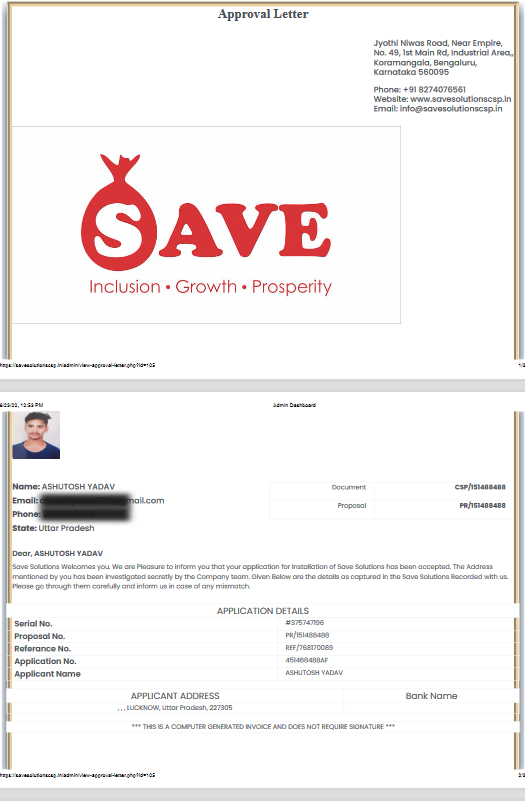
6. Forged documents:


Transactions with the imposters’ name:

Forged document with victim’s details:
Details of the imposters

Researchers found details of the alleged scammers that were found to be associated with the spoofed website. The information could not be validated. The name of the person found was Sudhir Verma with the email address [email protected]. His address mentioned was 56, Nehru Nagar, Delhi – 110006, India.
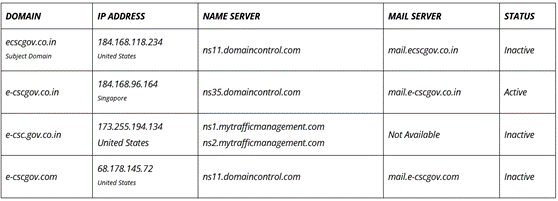
Details of the DNS search done by CRIL is shown below:
Conclusion
Though the internet has managed to reach almost every corner in India, the cybersecurity status of the country, especially in the rural areas, remains unclear. As our investigation proved, even the educated are often vulnerable and easy targets for scammers, putting utmost importance on raising cybersecurity awareness and highlighting the need to be digitally secure. Inclusion at the cost of security is a vulnerability that urgently needs to be patched.