Multi-extortion has been increasing, and companies are harassed in many ways to extract a ransom payment in return.
Ransomware attacks typically involve making system data inaccessible by encryption and extorting money to decrypt the data. However, as ransom demands are getting denied by victims, hacker groups are finding new ways.
Cybercriminals are misusing stolen data in several ways to pressure targets into succumbing to their threats. Multi-extortion is one such technique that has increased in the past few months.
Some of the newfound tactics used by cybercriminals for multi-extortion are as follows:
- Encrypting data – Asking targets to pay for making the data accessible.
- Data theft – Ransomware groups exfiltrate the data threatening to release it if payment is not made.
- DDoS attack – Hackers go on with their data exfiltration and launch DDoS attacks to stop the services. It can be even critical if suffered by healthcare providers that need to refer patient data.
- Harassment – Besides the above, cyber criminals use the stolen user data to directly call, SMS, and email, and impersonate them among other online crimes.
The above actions lead to creating more pressure and threat on organizations as it affects their reputation and credibility and creates fear after losing control of system data.
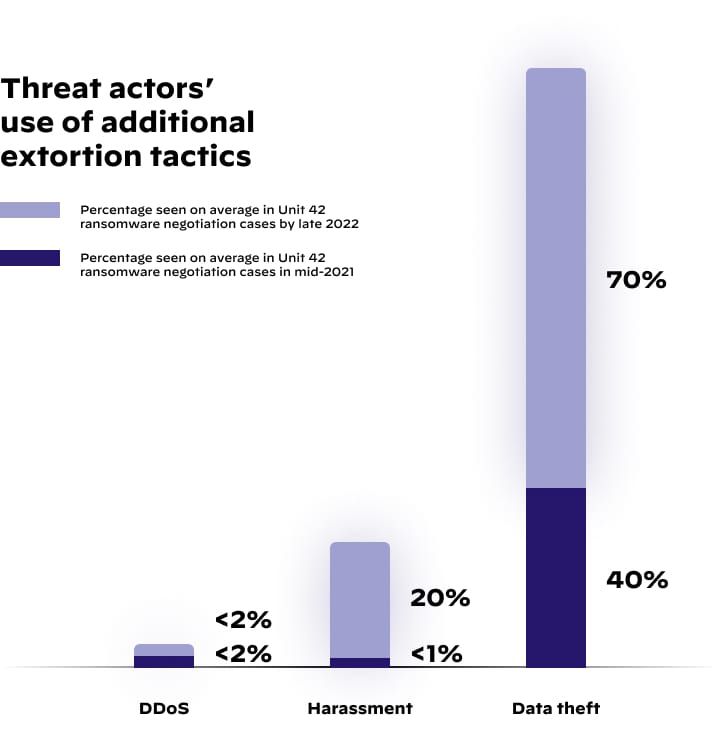
The Unit 42 multi-extortion research report
The Unit 42 threat intelligence and response teams conducted extensive research, the report highlighted the increase in the average percentage of ransomware negotiations cases.
(Photo: Palo Alto Network)
- The data theft percentage rose to 70% by late 2022 in comparison with 40% in mid-2021.
- Harassment was 1% in mid-2021 which increased to 20% in late 2022.
- DDoS attacks steadily increased by over 2% in both mid-2021 and late 2022.
Effectively reducing multi-extortion by creating a threat landscape
The incidence response plan suggested by Palo Alto Networks in its research report urged organizations to create a playbook to tackle the increased multi-extortion techniques.
Creating an incident response team and seeking help from legal authorities is paramount to mitigate cyberattack and their risks.
There must be a plan to work on the reduction of direct client harassment in the hands of hackers. Besides this, the incidence response effort needs to focus on a crisis communication protocol to help reduce uncertainty and make better decisions to tackle similar threats in the future.
Moreover, it is necessary to adapt to Endpoint Detection and Response to protect against incoming cyberattacks and enable Extended Detection and Response to proactively detect and mitigate threats.
Also, a study into the tactics, techniques, and procedures is recommended as it can help prevent threats by creating necessary tools and adapting to the current trends of threat actors.