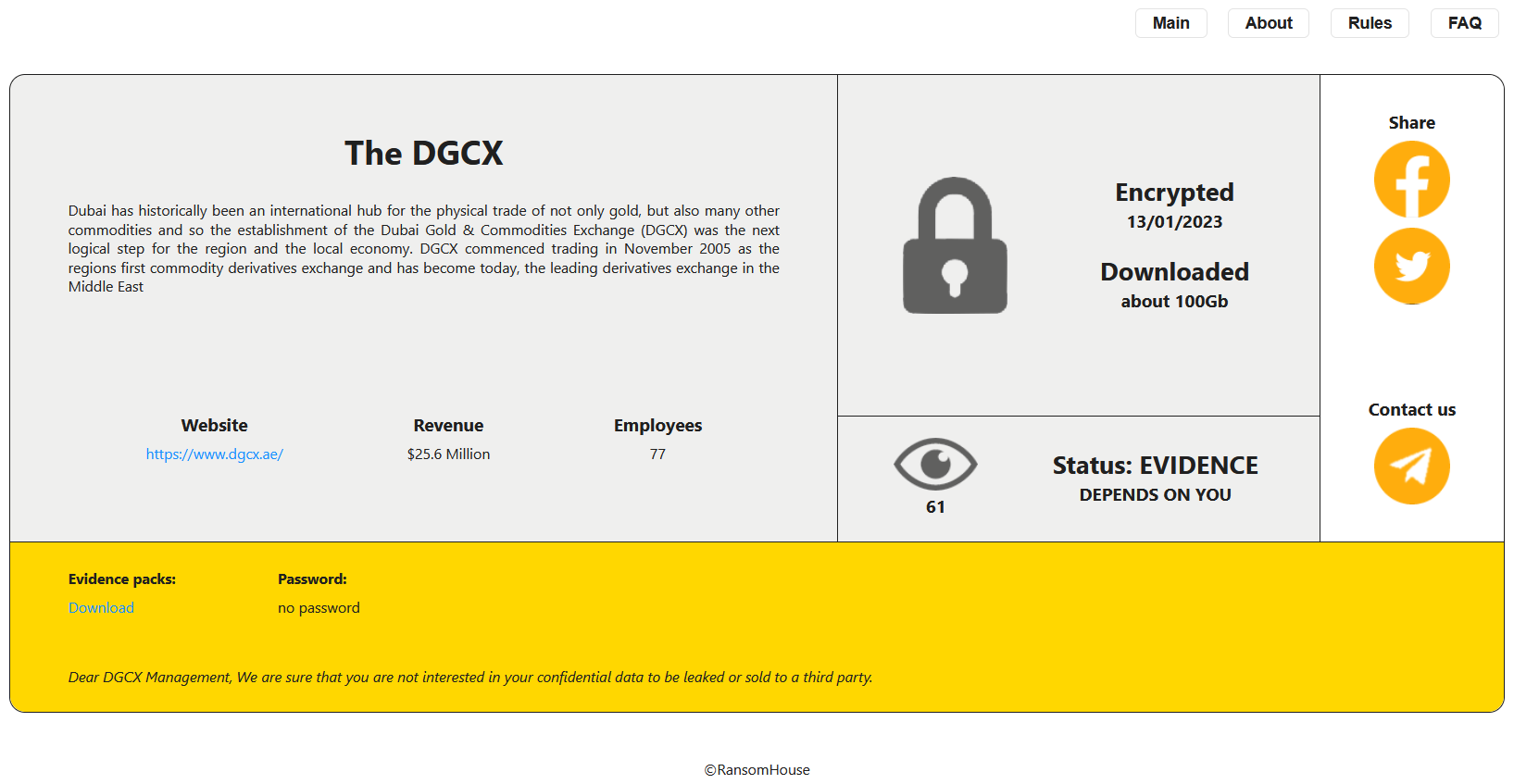
Threat actor RansomHouse has claimed to have accessed the data of Dubai Gold & Commodities Exchange (DGCX), a financial and commodity derivatives exchange located in Dubai, UAE. The gang has posted a leak notice, stating that they have downloaded 100GB of data.
According to the leak notice, the data was encrypted on January 13. Unlike a regular ransom notice, it does not threaten to leak data or have a ransom payment deadline.
The Dubai Gold and Commodities Exchange (DGCX) began operations in November 2005 and was the first derivatives exchange in the Middle East and North Africa region. It is owned by the Dubai Multi Commodities Centre.
Unlike other ransomware gangs, RansomHouse is a relatively new group made up of white hat hackers who have grown frustrated with organizations that have weak security measures, threat intel researchers speculate.
DGCX data breach and RansomHouse
The screenshot from the leak site noted some details about the leading Middle Eastern exchange including its $25.6 million revenue and a link to the official website. The post on the leak site ended with the line, “Dear DGCX Management, We are sure that you are not interested in your confidential data to be leaked or sold to a third party.”
Along with copied details from the About section of the DGCX website, the RansomHouse post stated the encryption date to be 13 January 2023. Moreover, it had links to prominent social media platforms including Facebook, and Twitter. The post had received 61 views at the screenshot was taken.
The claimed encryption happened days before DGCX reported a 8.24% rise in the value of contracts for 2022, reaching $162.01 billion. Additionally, the total number of contracts increased by 16% to a total of 8.239 million for the year.
DGCX has 267 members, with over 80% coming from the Middle East and the Indian subcontinent. The remaining members are from the US and Europe, and are based in financial hubs including London and Chicago.
RansomHouse ransomware group
RansomHouseis accesses victims’ networks by tapping into their vulnerabilities, steals data, and forces victims to pay up, lest their data is sold to the highest bidder, noted Malwarebytes Labs. And if no criminal is interested in buying the data, the group leaks it on their leak site.
“We believe that the culprits are the ones who found the vulnerability or carried out the hack, but those who did not take proper care of security,” reads the About Us page of the RansomHouse group.
Researchers list the group as a bunch of ‘disgruntled red-team pen-testers’ because of their polite speech on the forums. Cyberint posted that the RansomHouse group does not develop ransomware and focuses on exfiltrating data. The group has three channels on Telegram for talking about ransomware news and interacting with other members.
This group is also unique in the way it extorts money from victims. They appear to market themselves as penetration testers and bug bounty hunters more than your average online extortionist. After stealing data from targets, they offer to delete it and then provide a full report on what vulnerabilities they exploited and how,” said the Malwarebyte Labs report.
Like ransomware groups, they also have channels in place—a Telegram account and a leak site—to communicate with victims, journalists, and those who want to track their activities.
Besides these, the group claims to invite journalists to report data breaches from their pages after conducting a Know Your Customer (KYC) procedure with them. Their ‘Post-transaction guarantees’ includes the deletions of the following data:
- Uploaded information from the team’s servers
- Posts, websites, and pages related to the data leak
- Backdoors
The RansomHouse group defends bug bounty hunters who are underpaid. Since they used the Telegram channel of the Lapsu$ gang initially, it is connected to the gang.