Apart from the unpredictability of occurrences and the certainty of existence, what’s the connection between cyberattacks and weather conditions? That’s the theme Microsoft has adapted for the naming system for cybercriminals!
The new naming convention will assign unique names to different threat actors, consisting of two parts: a category of their activities and a randomly assigned animal or weather name.
But why the change from the existing naming system for cybercriminals?
Microsoft believes that the new naming system will make it easier for security professionals to understand and prioritize threats.
Because let’s face it, when you’re dealing with a million different cybercriminal groups, any naming system for cybercriminals can get complicated quickly. But with names like “Thunderstorm Threat” or “Cyber Cyclone,” you’ll never forget which group is responsible for which attack.
Naming system for cybercriminals: New season for Microsoft
“The complexity, scale, and volume of threats is increasing, driving the need to reimagine not only how Microsoft talks about threats but also how we enable customers to understand those threats quickly and with clarity,” wrote Microsoft Threat Intelligence Corporate Vice President John Lambert.
“With the new taxonomy, we intend to bring better context to customers and security researchers that are already confronted with an overwhelming amount of threat intelligence data.”
“With the new naming system for cybercriminals groups Microsoft identified as part of its ongoing efforts to combat cyber threats, the company hopes that this new system will make it easier for security professionals to identify and track threat actors, as well as to share information about them,” said an explainer.
The new naming taxonomy is part of Microsoft’s broader effort to improve cybersecurity measures and provide customers with effective and reliable tools to protect themselves against cyber threats, the explainer added.
“We realize that other vendors in the industry also have unique naming taxonomies representing their distinct view of threats based on their intelligence,” wrote Lambert.
“However, there are often overlaps or close alignments with tracked actors, and keeping track of these names can be challenging for defenders.”
New naming system for cybercriminals explained
Under the new system, cybercriminal groups will be assigned a unique name consisting of two parts: a descriptor of the group’s activities and a random animal name.
“In our new taxonomy, threat actor groups will be named after weather events. A weather event or “family name” represents either a nation-state actor attribution (e.g., Typhoon indicates origin or attribution to China) or a motivation (e.g., Tempest indicates financially motivated actors),” Lambert explained.
“Threat actors within the same weather family are given an adjective to distinguish actor groups that have distinct TTPs, infrastructure, objectives, or other identified patterns.”
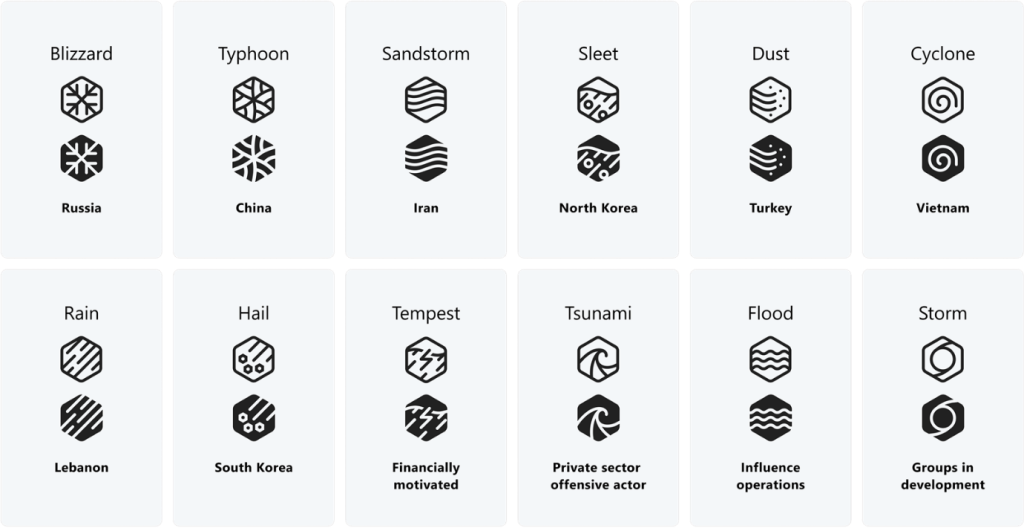
Microsoft categorizes cybercriminal groups into five groups: Nation-state actors, financially motivated actors, private sector offensive actors, influence operations, and groups in development.
“Threat actors within the same weather family are given an adjective to distinguish actor groups with distinct tactics, techniques, and procedures (TTPs), infrastructure, objectives, or other identified patterns,” said the Microsoft explainer
“For groups in development, where there is a newly discovered, unknown, emerging, or developing cluster of threat activity, we use a temporary designation of Storm and a four-digit number, allowing us to track it as a unique set of information until we can reach high confidence about the origin or identity of the actor behind the operation.”
The naming approach used previously (Elements, Trees, Volcanoes, and DEVs) has been retired and all existing threat actors have been reassigned to the new taxonomy.
According to Lambert, the new naming convention aims to help organizations more effectively identify and prioritize threats, facilitating better communication and cooperation between different organizations working to combat cyber threats.