A previously patched Cisco router vulnerability has been exploited by APT28 to conduct reconnaissance and deploy malware, a CISA advisory read.
The Cybersecurity and Infrastructure Security Agency published a joint advisory in collaboration with the UK National Cyber Security Center, the US National Security Agency, and the FBI.
The Cisco router vulnerability may still be exploited by threat actors, the joint advisory stated.
The first advisory for the Cisco router vulnerability
The advisory for the Cisco router vulnerability CVE-2017-6742 was first published in June 2017 with workarounds and information on limiting access to Simple Network Management Protocol (SNMP) from trusted sources.
Disabling SNMP was also suggested if needed. Threat actors called APT28 gained access to Cisco routers globally including Europe, the US government, and over 250 Ukrainian targets.
SNMP typically lets administrators remotely monitor network devices. This allowed hackers to gain access to sensitive network information. Using poor configurations like default or easy community strings can further help hackers gain access to networks.
Previous exploitation of the patched Cisco router vulnerability
APT28, also known as Strontium, Pawn Storm, Fancy Bear, the Sednit Gang, and Sofacy exploited the high severity CVE-2017-6742 with a base score of 8.8.
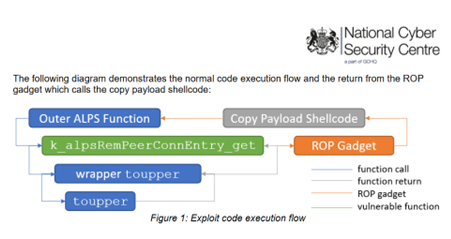
The exploitation of the vulnerability was found in 2021 by the same threat actor group. It caused a buffer overflow letting hackers control the instruction pointer and remote code execution.
The UK and US legal authorities wrote in the CISA advisory that they were nearly certain that APT28 is the Russian General Staff Main Intelligence Directorate 85th special service Center (GTsSS) military intelligence unit 26165.
APT28 has previously launched cyberattacks against the German parliament in 2015 leading to data theft and impacting the email accounts of German members of the parliament and the vice-chancellor.
The threat actors also attempted an attack on the Organization for the Prohibition of Chemical Weapons (OPCW) in April 2018.
Malware used in the previous exploitations of the Cisco router vulnerability
SNMP exploit was used to deploy Jaguar Tooth malware by writing shellcode to memory and then to write arbitrary 4-byte values to targeted addresses.
Jaguar Tooth is considered a low to medium sophistication malware that is non-persistent. It has the capability to automatically steal device information, and having a backdoor access.
Mitigation techniques
Steps to take to prevent cyberattacks from misusing the patched Cisco router vulnerability include patching all the systems with the latest updates.
Changing default credentials is of utmost importance as hackers do not take time in finding or guessing easy credentials.
CISA also asked users to secure their remote desktop protocol for unauthorized access. Training end-users is also imperative, especially in the wake of cyberattacks that are done owing to human errors or errors that can be avoided by staff with regular cyber hygiene.