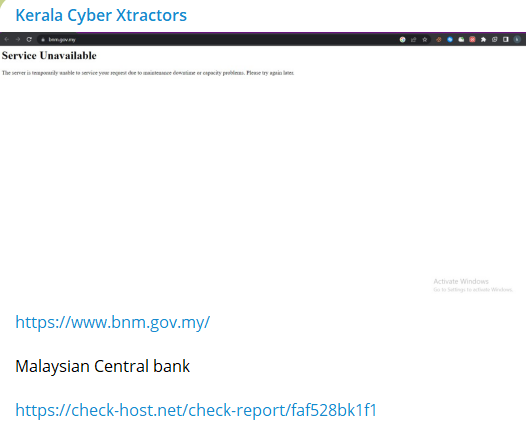
The Kerala Cyber Xtractors hacker group allegedly attacked the Malaysian Central Bank. According to reports, the group announced its plans to target Indonesian organizations almost a week back. The website is inaccessible post the announcement of the Malaysia Central Bank cyberattack by the group.
A group of Malaysian hacktivists last year targeted Indian websites. The group, reportedly called the “Malaysian Cyber Army”, claimed responsibility for the attacks carried out against Indian government and commercial websites.
The report states that the hacktivists used Distributed Denial-of-Service (DDoS) attacks to take down the targeted websites, rendering them inaccessible to users. The websites that were targeted included those belonging to the Indian government, educational institutions, and commercial entities.
Malaysia Central Bank cyberattack
The hacker group pinned the message about the Malaysia Central bank cyberattack and wrote that the website was down for two hours straight.
A message along with a screenshot of the hacked bank website was posted on Facebook. The post received about 60 views at the time of publishing this report.

The Central Bank of Malaysia controls the currency issue in the country. It is the banker and adviser to the government of Malaysia. It regulate the country’s financial institutions, credit system and monetary policy.
Under the Money Services Business Act 2011, the bank holds the power to regulate money services business industry and operations, including remittance, wholesale currency, and currency exchange businesses
Kerala Cyber Xtractors
The group runs Twitter, Instagram, and Facebook accounts besides using Telegram to post about their misadventures.
The Kerala Cyber Extractors group has a following of 961 individuals on Facebook. A post on Facebook claiming the Malaysia Central Bank cyberattack read, “Bank Negara Malaysia MALAYSIA CENTRAL BANK IS DOWN FOR 2 HOURS. THIS IS A PAYBACK FOR ATTACKING INDIAN GOVERNMENT WEBSITES AND OTHERS.”
The group was found celebrating their achievements on social media with claims of cyberattacks on entities belonging to other countries attacking Indian organizations.
Kerala Cyber Xtractors, allegedly from the Thiruvananthapuram city of Kerala, India, also breached the education and healthcare sector of Indonesia, a post read. They leaked COVID certificates, and other sensitive data from their database.
Scrolling through the previous claims, the group also launched attacks on Pakistani organizations. They posted screenshots of web pages showing an error message as shown below:
Other alleged victims of the Kerala Cyber Xtractors noted were the Sindh police. Their listed website was not functional at the time of writing. The group attacked nearly 80 major government servers belonging to Pakistan.
Some of the targeted websites form Pakistan were as follows:
wwf.gov.pk
Several groups from Asia are coming up with their groups and fighting each other aggressively lately. These group call themselves defenders of their focus, may it be humanity, peoples’s rights, the right to speech, freedom etc.
Websites get taken down for a few hours and a retaliatory attack is made by another group from the victimized country leading to a chain of cyberattacks launched on unsuspecting organizations. Some operations run by this group are OpIndia, OpSweden, and OpIran all discussing fighting societal oppression by hacking their websites.





















































