Cyble Research & Intelligence Labs (CRIL) has recently uncovered a concerning cybersecurity development: a threat actor has harnessed the Amadey bot to propagate SectopRAT, marking the emergence of a new wave of cyber attacks.
This operation centers around the LummaC information stealer, which has now joined forces with the Amadey bot malware and SectopRAT, creating a malicious alliance.
CRIL’s investigation has shed light on the intricate details of this campaign, highlighting how the Amadey bot malware is employed to distribute the SectopRAT payload sourced from the LummaC stealer.

The LummaC information stealer, found within Russian-speaking forums, operates under a Malware-as-a-Service (MaaS) model, enabling it to harvest sensitive data from compromised devices illicitly.
Its targets include cryptocurrency wallets, two-factor authentication codes, browser extensions, and other critical files and documents.
LummaC information stealer, Amadey bot, and SectopRAT: Understanding the attack chain
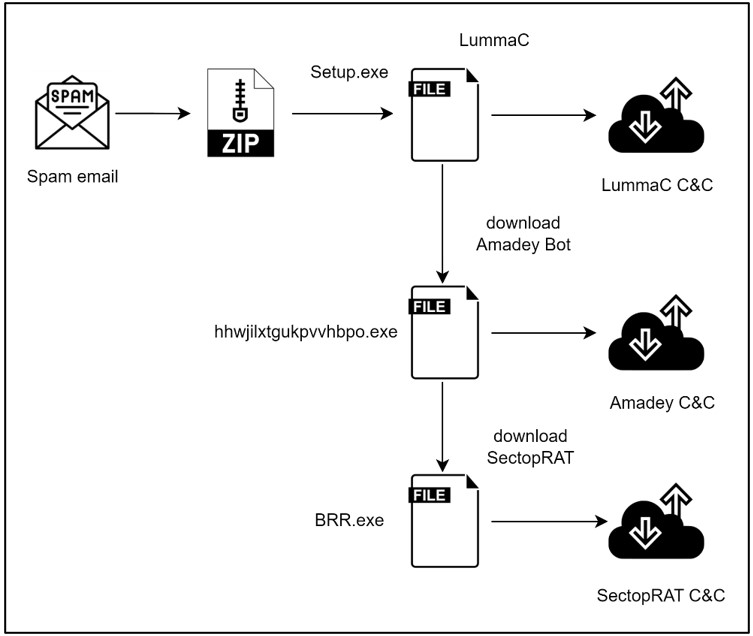
This collaboration between LummaC, Amadey, and SectopRAT operates in a series of events and completes their cycle after stealing information from their victim.
LummaC strategically facilitates loading the Amadey bot, fetching SectopRAT to target victims from all the corners.
As this collective effort penetrates systems, it leaves behind a trail of chaos: data theft, payload deployment, and stealing cryptocurrency information.
To understand how this attack campaign works, we must first get familiar with events associated with each threat.
For starters, the LummaC information stealer adds a unique twist to its campaign by introducing a secondary malware payload known as the Amadey bot.
This bot exhibits precision in replication and gains access through a concealed LNK file within the startup folder. Once activated, the LNK file initiates a series of events, setting off an infection chain on the victim’s device.
The LummaC Stealer, in turn, retrieves the Amadey bot malware, which reciprocates by fetching the SectopRAT payload.
This intricate web of interactions often begins with the LummaC’s information stealer exploiting via phishing websites masquerading as legitimate software sources. The stealer infiltrates victim systems through this disguise, making its way into unsuspecting computers.
Technical analysis of the LummaC information stealer campaign
Upon delving into the technical analysis of the LummaC information stealer, CRIL found that the hacker group uses ZIP files as carriers for its malicious payload. Concealed under names like “Newest_Setup_123_UseAs_PassKey.zip” and “Passw0rdz_113355_Open_Setup_App.zip,” these files trap victims, drawing them into an endless abyss.

At the core of this attack strategy lie two executable files, “Setup.exe” and a 32-bit GUI-based .NET Reactor executable.
Once initiated, these files extract sensitive data from the victim’s device. As the LummaC information stealer infiltrates victims, it meticulously gathers system details such as operating system information, hardware configuration, and screen resolutions.
Additionally, it homes in on the victim’s web browser, with a specific focus to extract information about the cryptocurrency wallets and two-factor authentication extensions.

Subsequently, the pilfered information is relayed to a command-and-control server, thereby completing the attack chain.
The Amadey Bot, a versatile malware discovered in 2018, has become a favored tool for hackers seeking to introduce supplementary malware payloads to their attacks.
Notably, the Lockbit ransomware group has been observed leveraging the Amadey bot to target victims.

“In 2022, associates linked to the LOCKBIT group employed the Amadey bot to distribute ransomware to their targets”, reads the report by Cyble. Lastly, the SectopRAT, a popular Remote Access Trojan (RAT) developed using a .NET compiler, represents the final payload of this campaign.
With diverse capabilities, SectopRAT can extract browser data, infiltrate cryptocurrency wallets, and even manipulate browser sessions by creating a concealed secondary desktop. Employing Anti-VM and Anti-Emulator mechanisms, SectopRAT operates stealthily in the background, siphoning information from unsuspecting victims.

The discovery of the LummaC-Amadey-SectopRAT alliance reveals a new level of cyber threat sophistication. This orchestrated attack chain explains the evolving tactics of cybercriminals, from data gathering to payload distribution.