In a world where digital threats are becoming more confusing, Cyble Research and Intelligence Labs (CRIL) has uncovered one of the most extensive deceptive domain spoofing campaigns to date.
Dubbed Operation TrustTrap, this large-scale operation has leveraged over 16,800 malicious domains to exploit cognitive trust mechanisms and harvest sensitive user data from unsuspecting victims.
The scope and scale of this operation reveal a shift in how cybercriminals are evolving their tactics to bypass traditional technical security measures.
What is Operation TrustTrap
Since early 2026, CRIL has been tracking a well-coordinated infrastructure involving a massive network of spoofed domains. These domains were designed to mimic legitimate government portals, particularly those related to transportation services like Department of Motor Vehicles (DMV) portals, toll payment systems, and vehicle registration services in the United States. The aim of this campaign is clear: credential and payment card harvesting through the exploitation of trusted government-facing services.
However, the technical complexity of the attack isn’t based on advanced hacking techniques. Instead, Operation TrustTrap exploits how humans visually interpret URLs. By embedding government-like subdomains, attackers have created fraudulent domains that resemble legitimate government addresses, deceiving individuals into visiting these sites and providing sensitive information.
Tencent Cloud and Alibaba Cloud APAC
The spoofed domains were predominantly hosted on Tencent Cloud and Alibaba Cloud APAC, both of which have significant data centers in the Asia-Pacific region. These platforms have been linked to the infrastructure of the campaign, and their concentrated use adds another layer of complexity to the attribution process.
Furthermore, CRIL found that the domains were primarily registered through Gname.com Pte. Ltd., a registrar known for its significant Chinese customer base. Other registrars, such as Dominet (HK) Limited and NameSilo LLC, were also identified in the campaign.
These domain names were often associated with .bond, .cc, and .cfd top-level domains (TLDs), which were frequently used to evade detection and blacklisting.
The Key Technique: Subdomain Trust Injection
The most common method used in Operation TrustTrap is subdomain trust injection. This technique involves embedding trusted government tokens, such as mass.gov or wa.gov, in subdomains rather than the root domain. In legitimate URLs, the .gov component typically appears at the end of the domain string, but in these malicious domains, .gov is cleverly placed as part of a subdomain.
For instance, a URL such as mass.gov-bzyc[.]cc will lead a user to believe they are accessing an official Massachusetts government page, but in reality, they are on a fraudulent site designed to capture personal and financial data.
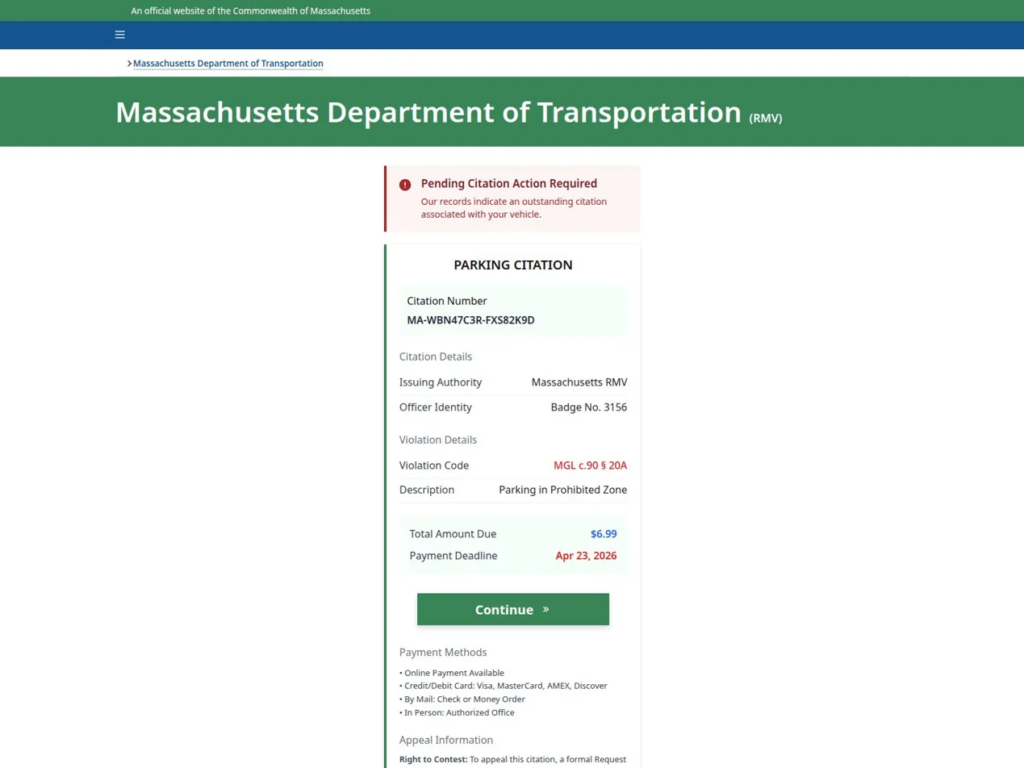
This manipulation of the domain’s structure is visually convincing, but it bypasses traditional security filters that only check the root domain for trusted indicators like .gov.
Another obfuscation technique used is hyphen-based semantic manipulation, where hyphens are inserted into familiar government identifiers to create visually similar URLs. This tactic further complicates the detection of malicious domains.
Global Targeting and Regional Focus
While Operation TrustTrap is heavily focused on the United States, targeting state portals such as those in California, Washington, and Florida, the operation is not confined to one region. CRIL identified similar spoofing efforts targeting government portals in India, Vietnam, and the United Kingdom.
In India, attackers have specifically targeted portals that follow the .gov.in domain structure. By injecting subdomains like www.in.gov-bond, the attackers were able to replicate the appearance of legitimate government websites, particularly those related to the Indian Department of National Investigation (NIA) and other defense-adjacent sites.
![Operation TrustTrap Reveals 16,800 Fake Domains Exploiting User Trust 41 APT36 impersonating NIA, India operating at nia[.]gov[.]in[.]in3ymonaq[.]casa](https://cyble.com/wp-content/uploads/2026/04/figure7.png)
This specific targeting suggests that the threat actor has knowledge of government infrastructure and how it operates.
APT36 and the Connection to Operation TrustTrap
In addition to the use of Tencent Cloud and Alibaba Cloud, the tactics, techniques, and procedures (TTPs) observed in the campaign bear a striking resemblance to those used by APT36 (also known as Transparent Tribe). This Pakistan-based Advanced Persistent Threat (APT) group has a long history of targeting Indian government entities, defense personnel, and diplomatic infrastructure.
The infrastructure used in Operation TrustTrap shows similarities to APT36’s previous campaigns, particularly in terms of the domain registration patterns and use of Tencent Cloud and Alibaba Cloud APAC infrastructure. Furthermore, the behavior observed, including domain rotation and the use of disposable domains, matches previous APT36 activities.
Registrar and Hosting Analysis
The dominance of Gname.com as the registrar of choice for over 70% of the spoofed domains points to a specific trend in the campaign’s operational setup. This Singapore-based registrar, which serves a large number of Chinese entities, is part of the broader infrastructure strategy that focuses on low-cost hosting in the Asia-Pacific region.
Notably, Tencent Cloud and Alibaba Cloud APAC offer cloud services with global reach, providing the necessary infrastructure to scale this type of malicious operation. These services have been instrumental in supporting the rapid deployment of phishing sites across a variety of government services, especially those involving time-sensitive financial transactions.






















































