The Indian Cyber Force (ICF) hackers group has claimed a series of precise cyber assaults on critical infrastructure in multiple nations, spanning Bangladesh, China, Pakistan, and Indonesia.
This organization, known for its prowess in the dark web hacking community, has shared its attack schedule until February 14, 2024, through its dark web channel, “INDIAN CYBER FORCE.”
Indian Cyber Force cyber attack timeline
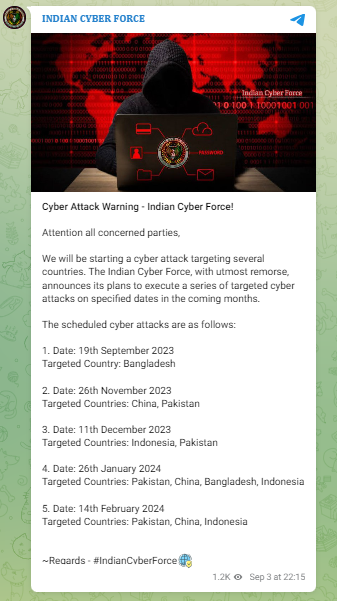
According to the threat actor, they have shared an in-depth plan for targeting these countries and also pointed out dates and times when they will launch their attack campaign against each country.
Attributed to the ICF, the cyber attack schedule includes the following events: On September 19, 2023, Bangladesh is the designated target. Then, on November 26, 2023, the focus will shift to China and Pakistan.
December 11, 2023, marks the date for attacks on Indonesia and Pakistan. Subsequently, on January 26, 2024, the threat actor plans to target Pakistan, China, Bangladesh, and Indonesia.
Finally, on February 14, 2024, the cyberattacks are slated for Pakistan, China, and Indonesia. These revelations underscore the audacity of these hackers and the lengths they are willing to challenge cybersecurity experts.
Indian Cyber Force hackers cyberattack claims
While the Indian Cyber Force hackers have boldly announced their intentions, the authenticity of their claims remains unverified. As mentioned earlier, this mysterious group has asserted its targeting of major corporations and governments across the nations.
In July 2023, the Indian Cyber Force hackers gained notoriety by infiltrating the website of an Indonesian PetroChemical Corporation. The method employed in this hack remains shrouded in mystery, but the group has teased the release of the compromised database.
In response to these threats, the BGD E-Gov CIRT issued an alert in collaboration with other organizations and the Bangladesh Bank. Various institutions, especially financial institutions, have taken proactive measures to minimize potential losses.
The BGD E-Gov CIRT officials remain vigilant, emphasizing that further attack threats persist. Instances of cyber attack proceedings have already been documented, including unauthorized information added to a former official’s biography on the Chittagong Customs House website.
Furthermore, the ICF claimed responsibility for targeting the e-ticketing site of Bangladesh Railway, causing an hour-long disruption. The same group also asserted its involvement in a cyber attack on the ticketing service provider “Shohoz,” leading to transportation service disruptions. However, Shohoz has denied these hacking allegations.
In a related development, hackers temporarily shut down the website flyticket.com.bd, rendering it inaccessible for an hour, along with a message that read, “No flights today, sorry.”
As concerns surrounding cyber attacks from Indian Cyber Force continue to mount, authorities have intensified security measures within the banking and financial sectors in response to government alerts.
While some cybersecurity experts maintain optimism about countering these threats, they unanimously stress the urgency of enhancing security measures and reinforcing digital transactions to repel potential breaches.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.