The NoName DDoS attack on Lithuania continues, with the threat group claiming its latest set of victim organizations in the country.
In this latest wave of NoName DDoS attack on Lithuania, this aggressive campaign targeted various industries, causing disruptions and raising concerns about cybersecurity in the Baltic nation. The threat group shared multiple screenshots along with the details on its Telegram channel.
Last month, the Pro-Russian hacker group took responsibility for a series of cyber attacks on key governmental institutions and major corporate entities within Lithuania. This series of attacks seems to be continuing in June as well.
NoName DDoS attack on Lithuania: The latest victims
Baltic Marine Spedition
The latest wave of NoName DDoS attack on Lithuania began with their sights on the website of JSC, “Baltic Marine Spedition,” a prominent Lithuanian company operating in the maritime industry.
Their website became the initial target of the cyber attack, leading to widespread service interruptions and a loss of online functionality.
Simatra Group and Aurida Logistics Solutions
As the chaos ensued, two more Lithuanian companies found themselves in the crosshairs of the NoName DDoS attack.

The websites of Simatra Group, a well-established organization, and Aurida Logistics Solutions, a key player in the logistics sector, were allegedly breached by the hacker group.
MTL Group and UAB MULTITRANSAS
The NoName hacker group showed no signs of slowing down as they proceeded to target the websites of MTL Group and UAB MULTITRANSAS, prominent logistics companies based in Lithuania.
The relentless barrage of traffic overwhelmed their servers, causing severe disruptions to their operations.
DOT LT Portal
Not content with their prior exploits, the NoName hackers turned their attention to the Lithuanian airline DOT LT. The airline’s portal became the latest victim of the attack, suffering from prolonged downtime and rendering crucial services inaccessible to passengers and employees.
Freught and Baltic Shipping

Continuing their rampage, the NoName hackers directed their assault toward the website of Freught, a leading logistics company in Lithuania. The attack further highlighted the vulnerability of the country’s logistics sector and raised concerns about the potential economic impact of such malicious activities.
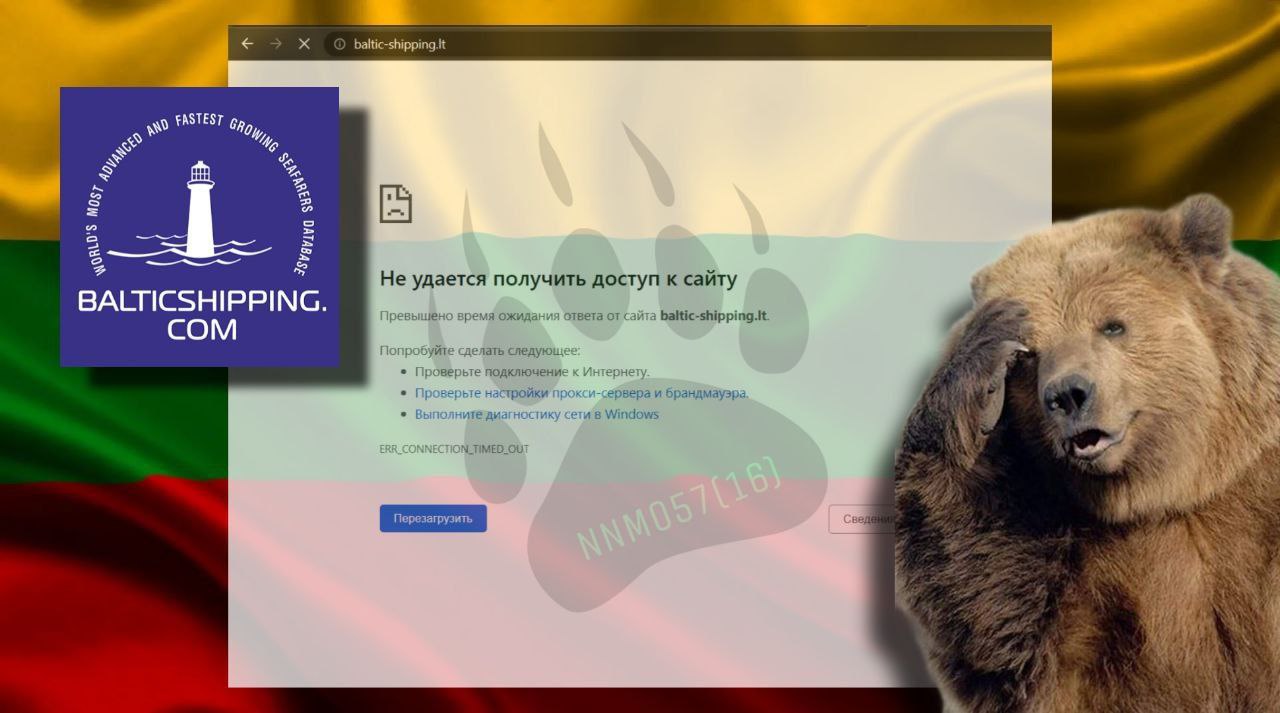
Additionally, Baltic Shipping, a company integral to the maritime industry, suffered a similar fate, exacerbating the unease among Lithuanian businesses.
The growing threat of cyber attacks on Lithuania
According to the National Cyber Security Report released by Lithuania’s Defence Ministry, over 4,000 cyber attacks were documented in 2022. NoName DDoS attack on Lithuania tops the attacks attributed to a single threat actor.
Interestingly, the total number of recorded attacks remained comparable to the previous year, but there was a significant decline of over 50% in medium-impact incidents, reported LRT.
Remarkably, there were no high-impact attacks reported in either 2022 or 2023. The report highlights a notable change in the landscape, noting that the number of Distributed Denial of Service (DDoS) incidents actually increased compared to the previous year.
Out of the total incidents recorded in 2022, 33 were categorized as medium-impact incidents and were primarily associated with DDoS attacks and malware dissemination to gain unauthorized access to communication systems for malicious purposes.
The report reveals that most incidents were linked to malware (1,795 cases) and information gathering (1,005 cases). Additionally, incidents involving the distribution of spam, misleading information, and DDoS attacks witnessed an upward trend over the year.
Public sources provided valuable information regarding attempts to target more than 130 publicly accessible websites. Notably, a hacker group with pro-Russian affiliations claimed responsibility for these attacks, as indicated in the document.
Across various sectors, the highest number of incidents occurred in state and local government entities (564 cases), followed by the security and defense sector (312 cases) and the business sector (159 cases).
Media Disclaimer:
This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.




















































