Researchers at the Cyble Research and Intelligence Labs (CRIL) reported a new scam where threat actors are spreading malware via a FiveM spoofer. With this threat campaign, the threat actors seem to be targeting the GTA V modding community with a fraud FiveM server that promises to let users unban themselves. The gaming community seems to be the central target for threat actors in these past few months, as we saw multiple instances of gaming platforms, titles, and users getting victimized by malware campaigns.
According to the CRIL report, the malicious site, hxxps://cloud-spoofer[.]xyz, offers bait to GTA V users and claims to help unban themselves from the FiveM servers. Once the user visits the website, it redirects them to a discord channel where there is a malware-injected version of a FiveM spoofer. This is a standard phishing practice used by threat actors. However, this time they have targeted the modding community and seem to be going after the Grand Theft Auto V series fans.
What is FiveM?
FiveM can be described as a private server (not affiliated with Rockstar games) that allows gamers to host mod servers in the game or join modded servers created by other users. In other words, it is an additional service to GTA V that runs on top of the game. However, to use the FiveM server, the user needs to have a verified copy of GTA V; otherwise, the server will not work.
Steam or Social Club can verify the copy’s authenticity and keep unidentified gamers out of the servers. Despite being an illegal part of the game, the modders are highly cautious of users who try to cheat on the servers. Often, gamers get banned due to illicit behavior or through external programs that attempt to inject themselves into the FiveM client. Nevertheless, users have found shortcuts to join modded servers on FiveM without purchasing the actual game copy — putting them at the bay of being banned by the modders.
FiveM scammers on a rise

Once a user is banned, they can try Spoofer tools to get unbanned, and various clients offer this service. However, FiveM mods quickly track these clients and forbid them from entering the server again. According to Cyble, the fraudulent Discord server was created in September 2022, indicating that the malware campaign is pretty new. For the last two months, the threat actor seems to be selling the FiveM Spoofer for 20-60 Euros.
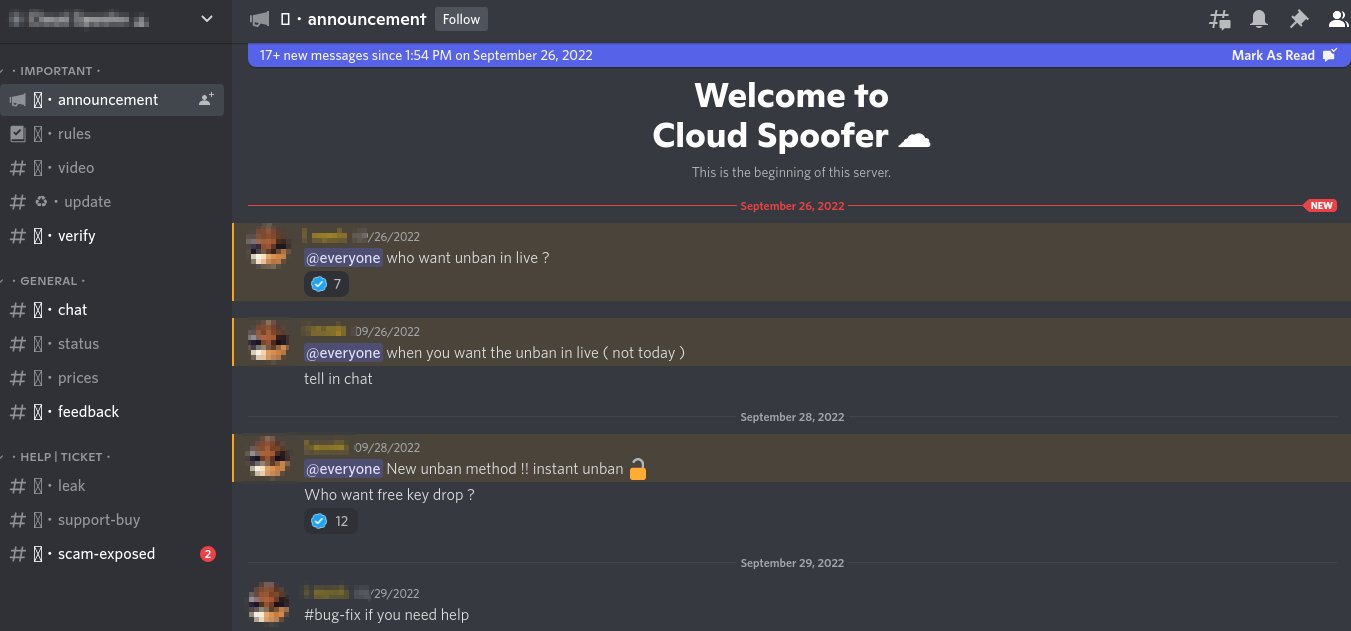
The CRIL team observed that the threat actor was also promoting their Discord server via a pyramid scheme, where it offers a giveaway for Discord channel members who create YouTube and TikTok videos to promote the threat actor’s Discord server link. The link is inserted in the description of those videos, which is a clever way to spread the service while hindering confrontation from authorities. Since users blindly promote the Discord server, the sheer number of victims falling for the trap increases — giving a clear path for the hackers to steal more data from multiple users.
Technical analyses of the FiveM scam
The threat actor lures the victims by offering an instant unban service on FiveM and redirects them to subscribe to its YouTube channel. The spoofer link is added to the YouTube video description, where the users (potential victims) can download it after completing the initial processes asked by the threat actor.
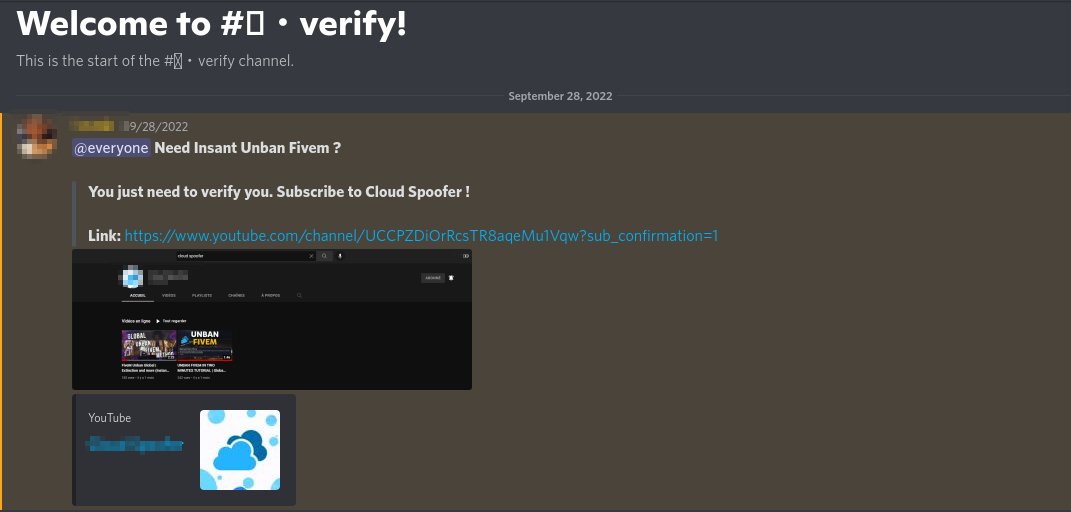
Once downloaded, the alleged spoofer gets saved into the download folder with the name Fivem_Spoofer.rar. Upon opening the RAR file, the users are greeted by a .exe file named Cloud Free.exe.
These .exe files are executable and don’t require any additional program to run. Once the user double clicks on the file, the modified version of the spoofer downloads malicious files to the system with these two links — hxxps://cloud-spoofer.xyz/AnyDesk[.]exe and hxxps://cloud-spoofer[.]xyz/GameOverlayUI.exe.
The researchers claim that the spoofer is real, but it has been altered, and the hackers have added additional code and files that trace back to a remote server, where the hacker operates the malware and spoofs over the information from the compromised system.
The hacked spoofer uses a similar UI as the original one and shows the standard buttons with operations attached to each of them, including spoofer, cleaner, global ban, etc. While the user becomes occupied with the controls and the overall use of the spoofer, the threat actors install malicious code to the system in the backend.

According to CRIL, the modified spoofer installs AsyncRAT malware and allows the threat actor to control the victim’s system while staying discreet about the malware’s existence. Moreover, suppose the user tries to select any of the functions available in the tool, in that case, it further downloads additional malicious files on the system, giving complete control of the computer while still staying hidden inside the spoofer.
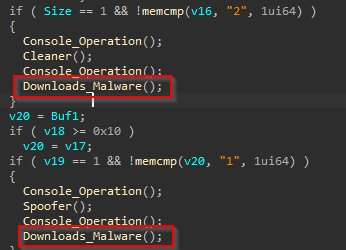
The malware, AsyncRAT, is capable of remote viewing and recording the user screen, tapping into keystrokes using keyloggers, as well as taking control over the sensitive functions of the system, including power on/off, downloading, and executing files.
The threat researcher company has advised users not to fall for these traps and use the original links for downloading software and online programs because, often, these too-good-to-be-true applications are injected with malware with the sole intent of stealing and harassing the victims.



















































