In this highly connected business environment, connectivity creates frictionless opportunities and vulnerability to cyber-attacks. Thriving under cyber attack is not a radical proposal but a function of digital resilience.
Unlike conventional security controls, which assume the nature of future cyber attacks is the same as past attacks, the application of behavioral psychology breaks that myth. I.e., Behavioral based threat prevention is a critical part of an effective cyber resilience strategy.
Learning from the success of clinical psychology
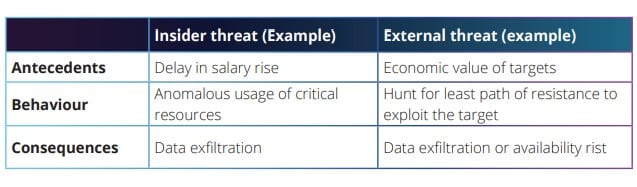
As it is proven in clinical psychology to treat patients, behavior does not change in a vacuum but occurs in response to proceeding events and situations we call antecedents and is encouraged to happen or not concur by the consequences of the behavior that immediately follow.
The most significant difference between adopting behavioral psychology in the clinical field and cyberspace is just the final business outcome; in the clinical meant to change human behavior, but in cyberspace, intended to predict human (and object) behavior.
Example: Mitigating insider threat risk exposures
Unlike external adversaries, It is not easy to profile insider threat adversaries. They may or may not have financial motivation. They may act maliciously out of anger, frustration, or whim. When a user exhibit behavior in the presence of precursor events, his behavior has consequences.
Preceding events (i.e., Antecedents) prompt behavior to occur and results maintain/increase/decrease it in the future based on the desirability of the consequences. (ie, in the case of insider threat, it is either damaging the system/assets or stealing critical information).
Not a silver bullet for all the problems
Like any other technology solution, behavioral-based detection capabilities’ effectiveness depends on these critical factors.
- Availability of multiple observations of the same user behavior under various conditions.
- Observations must include adequate descriptions to identify the who, what, when, where, and how of past behaviors.
- Necessary of SME: A security analyst can leverage subject matter experts (SME) guidance when there is a lack of observations.
- The findings’ quality depends on the antecedents and consequences associated with past behavior. The mere selection of a specific type of statistical method or calculation can’t determine the quality of the findings.
Key behavioral indicators of insider
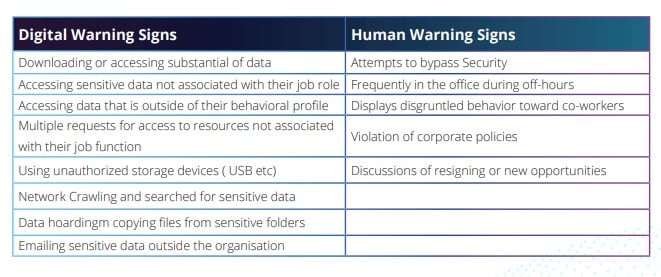
Unlike the advanced persistent threat (APT) adversaries, insiders neither exhibit psychological nor demographic profiles. Instead, they exhibit a unique behavioral pattern as they move along the idea-to-action continuum.
Here are some of the potential behavioral patterns we often hypothesize to detect an insider’s earlier indication.
Summary
Although the business environment evolved from bricks and mortar to bits and bytes, the underlying behaviors associated with insider behavior have remained the same.
So, behavioral-based capabilities are vital in reducing insider threat risk exposures. At the same time, the quality of reliable insider threat prediction over time is based on our ability to identify the precursor antecedents that set the stage for the behavior to occur and the consequences of it.
– By Pons Mudivai Arun, Head of security products, NetScaler
Watch this space and stay updated with Cybersecurity Features.