Researchers at Cyble Research & Intelligence Labs (CRIL) found an Android malware — explicitly designed to target the Uyghur community. The malware disguises itself as a book named “The China Freedom Trap.” Upon launching the book, it executes malicious codes in the backend, stealing sensitive information from the users like SMSes, contact data, call logs, and neighboring cell information.
The China Freedom Trap malware explained
"The China Freedom Trap.L1986v8V.apk": fd99acc504649e8e42687481abbceb71c730f0ab032357d4dc1e95a6ef8bb7ca
Seems related to some possible Uyghur targeted samples (https://t.co/44BGePli0E / https://t.co/hp385qm1Xw)…
🤔@bl4ckh0l3z @LukasStefanko pic.twitter.com/cWsYdJ11ZZ— MalwareHunterTeam (@malwrhunterteam) August 25, 2022
During its routine threat hunting exercises, Cyble Research & Intelligence Labs (CRIL) found a Twitter post where security research team MalwareHunterTeam wrote about the malware and how it was purposely designed to target the Uyghur community. For the uninitiated, the Uyghur community is an Ethnic group from Central and East Asia and one of China’s 55 officially recognized ethnic minorities.
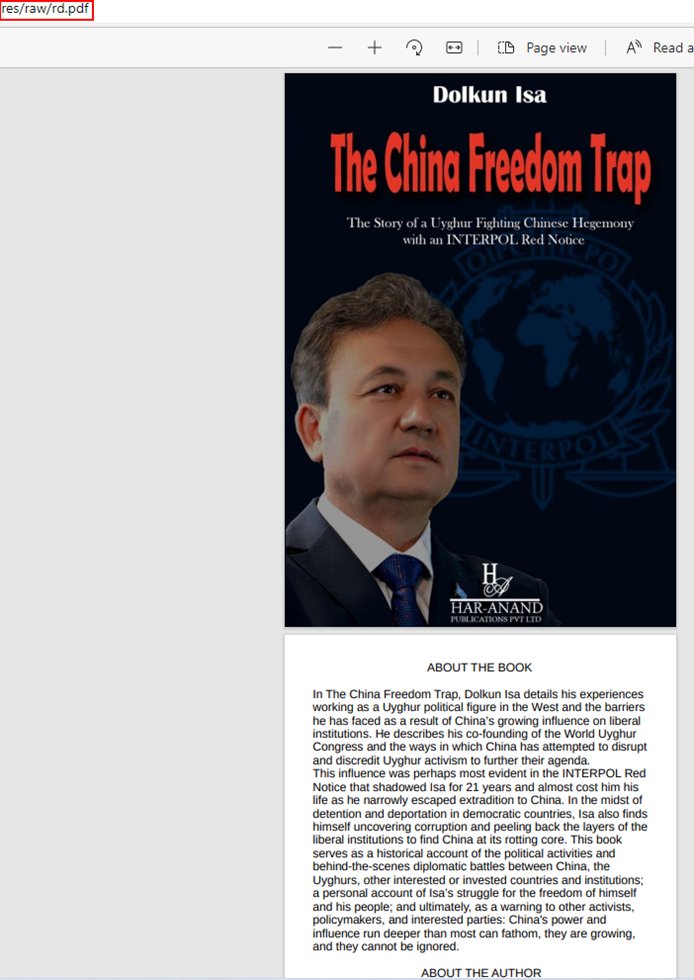
The China Freedom Trap is a book by Uyghur politician and activist Dolkun Isa chronicling his experiences and fighting crimes against Uyghurs. The book seems to be the perfect trap for attracting potential victims involved in the growing conflict between the Government of the People’s Republic of China and the Uyghur community. It acts as a catalyst or the point of research for both the parties involved, and the probability of people downloading the book will be high during the intense power battle between the two parties.
CRIL analysis of the infected China Freedom Trap
The security researchers at Cyble did a behavioral analysis and found that the malware used a similar icon as the cover page of Isa’s book. Upon opening it on the device, it runs, and shows the user a few pages, including the book cover, an introduction of Isa, and a condolence letter at the end.
Once downloaded, the malware-injected book tries to steal sensitive information from the users’ devices. The information includes SMSes, call logs, neighboring cell information, and contact data. The researchers also stressed the malware’s ability to capture the screen and take unauthorized pictures from the device’s camera.
China Freedom Trap and permission abuse
Most Android malware requires access to the device, which is protected by the operating system’s permission protocols. Android permissions are special privileges verified apps can use to access sensitive information from the smartphone. Since smartphones are a hub of data about its user, this permission helps limit which apps can use what data and determines the degree to which specified data can be shared with an application.
Cyble Research & Intelligence Labs (CRIL) did a technical analysis of the malware and found that it was used in an app called ‘The China Freedom Trap’ and had a package name com.emc.pdf. It used the standard 64-character alphanumeric ‘SHA256’ Hash code. Once the user installs the app, the malware requests 27 permissions and abuses 13 of them.
Here is a list of permissions used by the malware
- ACCESS_NETWORK_STATE
- READ_PHONE_STATE
- READ_SMS
- WRITE_SMS
- READ_CONTACTS
- PROCESS_OUTGOING_CALLS
- WRITE_EXTERNAL_STORAGE
- READ_CALL_LOG
- RECORD_AUDIO
- ACCESS_COARSE_LOCATION
- ACCESS_FINE_LOCATION
- GET_ACCOUNTS
- READ_HISTORY_BOOKMARKS
Source code investigation
Upon investigating the malware’s source code, Cyble Research & Intelligence Labs (CRIL) came across many sophisticated techniques used by the malware to exploit the users’ devices. For example, the malware checks the SDK version of the Android device, and if it’s below 29, the malware will conceal its icon from appearing on the screen and run silently in the background.
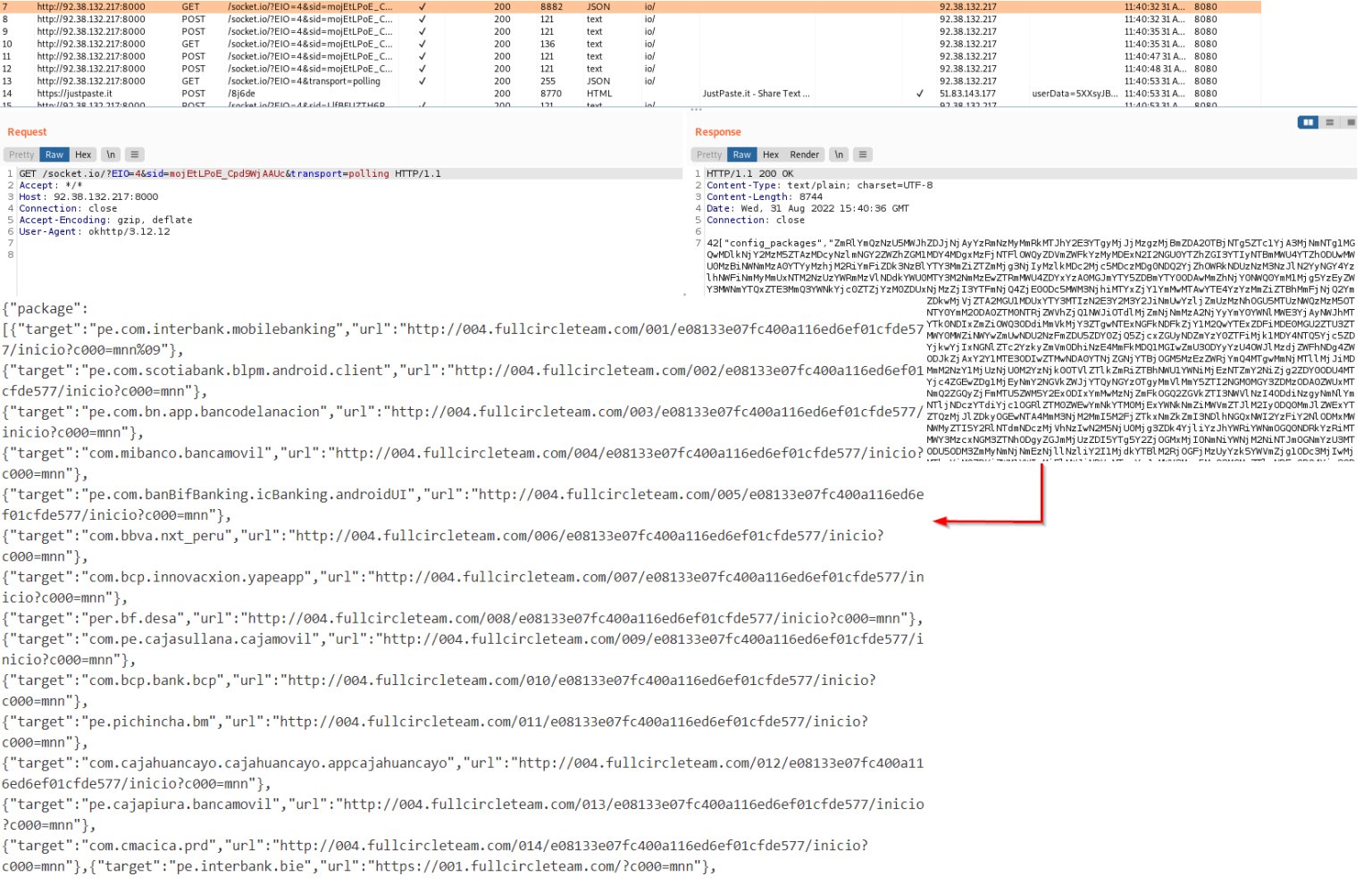
Once the malware is executed, it checks for the Internet connectivity and fetches the device’s Wi-Fi, DHCP, and other important information. It also runs a code that fetches the neighboring cell information, including the Received Signal Strength and Cell ID location.
With this malware, the TAs exploit the Uyghur–Chinese conflict to target unsuspecting individuals. According to the research team, the malware steals information from the infected devices by using the commands from the TA’s Command and Control (C&C) server. Since Google and other American services do not exist in China, the malware-injected app is being distributed via third-party websites and other app platforms in the region.