Two vulnerabilities in Apple iOS have been actively exploited in the wild. The company has issued patches for these vulnerabilities in Apple iOS its latest software update.
The comprehensive set of updates cover vulnerabilities in Apple iOS, iPadOS, macOS, watchOS, and Safari browser.
While the identity of the threat actor remains unknown, Apple is taking the necessary steps to mitigate the risks posed by these vulnerabilities.
Three zero-day vulnerabilities Apple patched in May were added to CISA’s Known Exploited Vulnerabilities (KEV) catalog, The Cyber Express reported earlier.
Vulnerabilities in Apple iOS and Operation Triangulation
The updates are designed to tackle a range of security flaws, including two zero-day Apple iOS vulnerabilities that have been actively exploited in a mobile surveillance campaign called Operation Triangulation.
One of the zero-day vulnerabilities in Apple iOS, CVE-2023-32434, is an integer overflow flaw within the Kernel. This vulnerability has the potential to allow a malicious app to execute arbitrary code with kernel privileges.
The second zero-day vulnerability, identified as CVE-2023-32435, is a memory corruption issue within WebKit that can lead to arbitrary code execution when processing specially crafted web content.
“Apple is aware of a report that this issue may have been actively exploited against versions of iOS released before iOS 15.7,” said the patch alert.
Kaspersky researchers Georgy Kucherin, Leonid Bezvershenko, and Boris Larin were credited for the discovery of this vulnerability.
Further analysis of the zero-click attack campaign targeting iOS devices has revealed significant details about the spyware implant employed.
Known as TriangleDB, this sophisticated implant operates exclusively in device memory, leaving no traces behind after a reboot.
Its capabilities encompass a wide range of activities, such as interacting with the device’s file system, managing processes, extracting keychain items for gathering victim credentials, and monitoring geolocation.
The complex nature of TriangleDB underscores the determination and sophistication of the threat actors involved.
A third zero-day vulnerability, identified as CVE-2023-32439, allows for arbitrary code execution when processing malicious web content. Apple has implemented improved checks to address this type confusion flaw.
Operation Traingulation: An overview
A sophisticated mobile campaign called Operation Triangulation has been targeting iOS devices since 2019, cybersecurity firm Kaspersky reported this month.
The campaign utilizes zero-click exploits through iMessage to infect devices, gaining complete control and access to user data. By creating offline backups of targeted devices, Kaspersky found evidence of compromise.
The attack begins with a message containing an attachment that triggers the exploit, requiring no user interaction for code execution.
“Without any user interaction, the message triggers a vulnerability that leads to code execution,” said the Kaspersky report.
“The code within the exploit downloads several subsequent stages from the C&C server, that include additional exploits for privilege escalation.”
The exploit retrieves additional payloads to escalate privileges and installs a fully-featured advanced persistent threat (APT) platform from a remote server.
The implanted malware operates with root privileges, allowing it to extract sensitive information and execute downloaded code as plugin modules. It silently transmits private data, including microphone recordings, messenger photos, and geolocation, to remote servers.
To cover its tracks, the malware deletes the initial message and exploit attachment, erasing traces of the infection. However, re-infection may occur after device rebooting due to the lack of persistence in the malicious toolset.
“The oldest traces of infection that we discovered happened in 2019. As of the time of writing in June 2023, the attack is ongoing, and the most recent version of the devices successfully targeted is iOS 15.7,” the report said.
According to Kaspersky, the extent of Operation Triangulation is not fully known, but ongoing attacks have targeted devices running iOS 15.7.
The involvement of zero-day vulnerabilities in iOS remains uncertain, as Apple has released iOS 16.5 and an update to iOS 15.7.6.
Patches for vulnerabilities in Apple iOS and more
To ensure the security of its users, Apple has made the following updates available:
iOS 16.5.1 and iPadOS 16.5.1: These updates are compatible with iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later.
iOS 15.7.7 and iPadOS 15.7.7: These updates are compatible with iPhone 6s (all models), iPhone 7 (all models), iPhone SE (1st generation), iPad Air 2, iPad mini (4th generation), and iPod touch (7th generation).
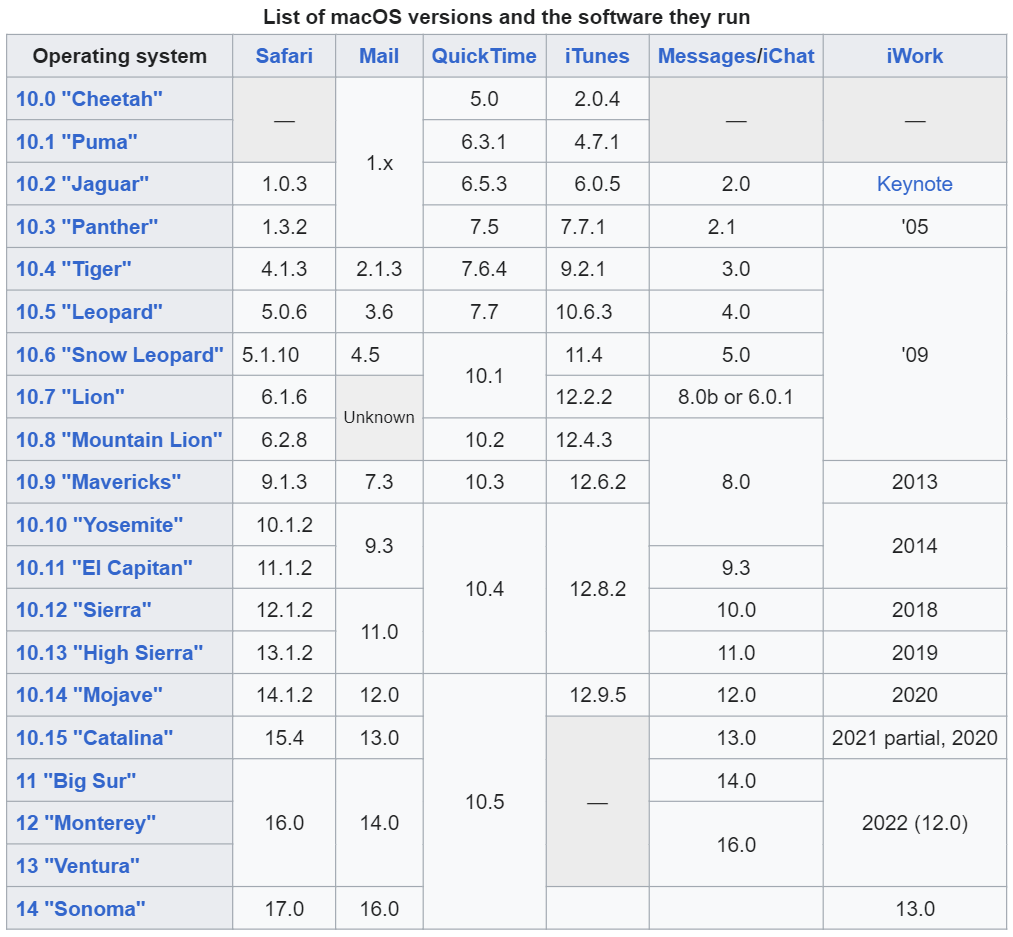
macOS Ventura 13.4.1, macOS Monterey 12.6.7, and macOS Big Sur 11.7.8.
watchOS 9.5.2: This update is available for Apple Watch Series 4 and later.
watchOS 8.8.1: This update is available for Apple Watch Series 3, Series 4, Series 5, Series 6, Series 7, and SE.
Safari 16.5.1: This update is applicable to Macs running macOS Monterey.