The United States Department of Defense released a Zero Trust strategy to work toward a robust security infrastructure required to secure systems. The Zero Trust (ZT) capabilities will have a better reach than the traditional perimeter network approach. And it will be adapted in the fiscal year 2027.
Preparing a Zero Trust roadmap for security
The Department of Defense Zero Trust Strategy model would think in terms of a ‘never trust, always verify’ approach, which would build a sense of responsibility to verify every entity reaching the network. It would require all DoD components to work with and integrate Zero Trust features, technologies, solutions, and processes. The ZT strategy would enable the following outcomes:
- Technological acceleration: Since Zero Trust-based technology works at a higher pace, it would help the department address issues and promote innovation.
- Seamless Zero Trust Enablement: Since the strategy will be employed on the department and component level, it would help seamless and well-coordinated ZT execution. It would also bring more transparency and analytics features regarding the network and environment, among other things.
- Securing DoD systems: The Zero Trust strategy would enable securing and defending the systems of the Department of Defense and gaining enterprise resilience from attacks.
- Zero Trust cultural adoption: Beyond better safety, the ZT adaptation would also create a mindset of a security framework with commitment, outreach, awareness, and training.
Why is Zero Trust required for the Department of Defense?
The Zero Trust Strategy and roadmap are needed due to the current threat map and sophisticated cyberattacks the nation and department face. A strategic plan was required to prevent, detect, and report existing and potential threats. If the defense systems are secure, the people can be secured. It would progress data sharing in a partnership environment and help remediate threats. However, the ZT model is not limited to this; it will constantly be worked upon to adapt to the changing needs to keep systems secure. It would also enable better support for an interoperable information system for warfighters’ missions.
The ZT aligns with the DoD national defense strategy and thus will be applied across all military multi-domain operations, including cyber, air, sea, ground, and space. It would also help target the exact threat actor and enable data sharing at the required speed. It will enhance data format, vetting of data, and secure point of origin, with targeted, tagged and trusted data.
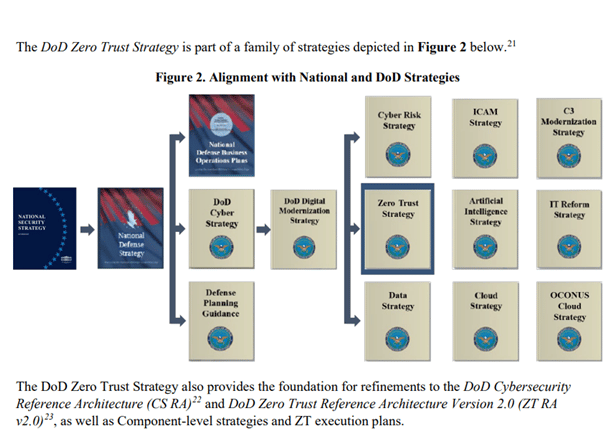
The ZT model aims to help streamline every connected channel where data is managed and shared. Such as artificial intelligence, cloud, and OCONUS cloud strategy. The strategy is a refined version of the previous one from the Pentagon. It was recommended by the White House’s office of management to be met by the fiscal year 2024. The DoD chief information officer John Sherman had said in August that the “….adversary capability we’re facing leaves us no choice but to move at that level of pace,” according to Breaking Defense. He had said the one goal he had was to implement the zero-trust architecture.
Zero Trust strategy outcomes
While the pre-ZT architecture attempted to lockdown networks after detecting a threat, it would now offer checks and balances. This would also offer proper authorization to sensitive data to users working remotely and reduce the attack surface and threats to clouds. Most of the damage would be containable, and mitigation would be easier. ZT model offers a real-time risk-based response and a more aligned architecture across networks.
Microsoft applauds plan to implement Zero Trust Strategy
In its blog, Microsoft applauded the DoD’s move to adopt the Zero Trust strategy, which has been considered for years by several departments. Microsoft pointed out that this move is significant when the demography of attacks on United States government networks says it has suffered about 50% of the global nation-state attacks. The transition of the DoD’s approach from compliance and control-based to outcome-based would strengthen the flow of work as cybercriminals would be stopped instead of only ensuring a security plan is in place.
The Zero Trust strategy

The Zero Trust strategy will not just secure the DoD information enterprise (IE) within the joint information environment (JIE) but also secure the Department of Defense information network (DODIN). It will offer better visibility of specific events and automate responses. No user will have access to systems without authentication, and it will secure virtual machines, among others.




















































