Enrolling for a certificate course in cybersecurity may require consideration of many factors. A certificate course may be driven by career goals, education and work experience, job profile, pay package, growth prospects, and desired job satisfaction. One may opt for several cybersecurity certifications, keeping their requirements in mind as choosing the most apt cybersecurity certification can help carve the path to a fruitful career. The following are some of the best and in-demand cybersecurity certification courses companies, organizations, and law enforcement agencies look for while hiring qualified cybersecurity candidates.
The basic hierarchy of roles in the field of cybersecurity
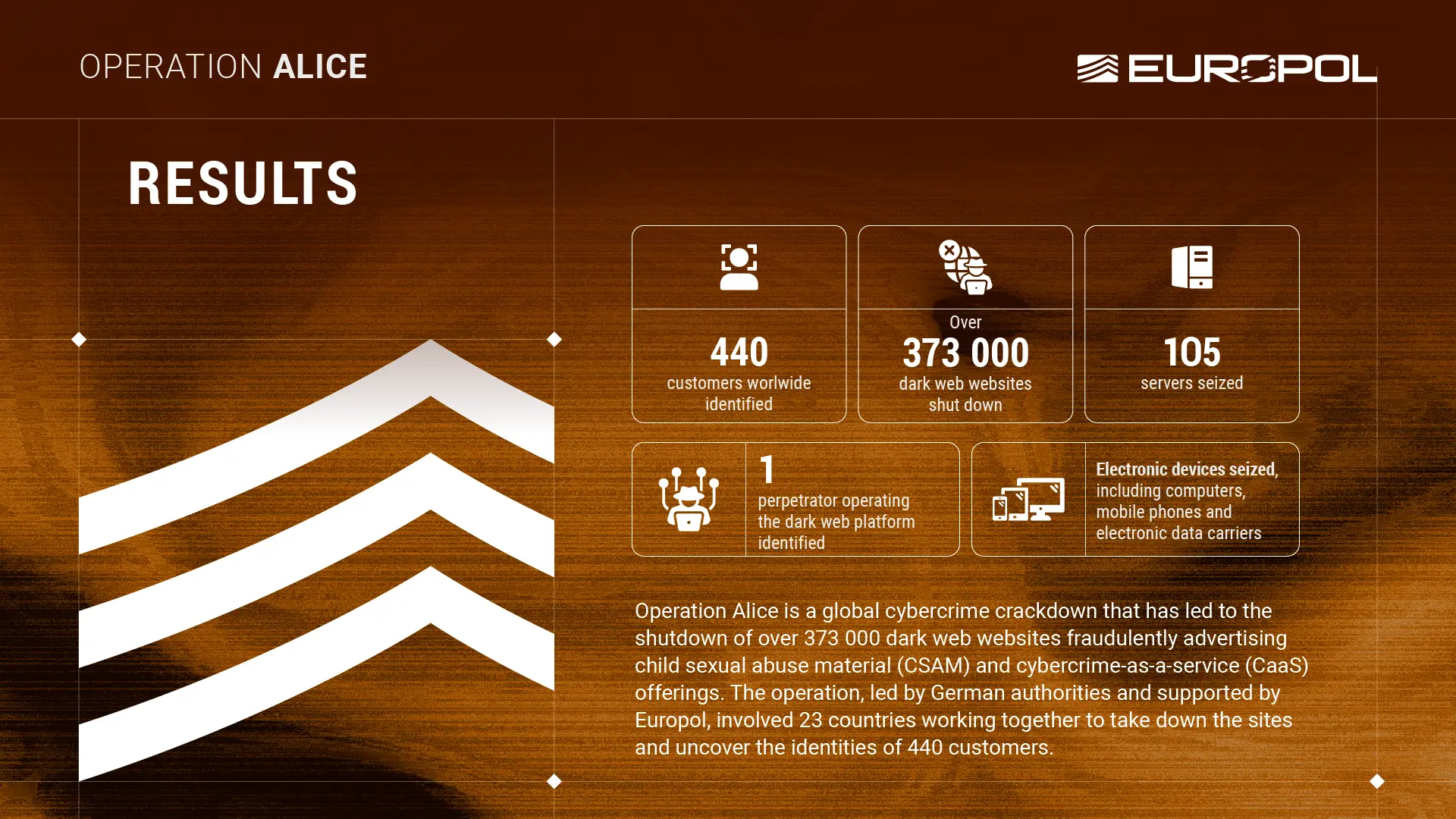
Hundreds of certifications are offered by universities and institutions. As per the desired certification, a candidate may choose to specialize in network security, security architecture and engineering, asset security, security risk management, security assessment and testing, software security, and security operations program.
A roadmap to various certifications in cybersecurity can help individuals find the right role and corresponding skills required for it. A detailed report by Paul Jerimy elaborates on the varied levels of certifications and the hierarchy in this field. In the report, Jerimy formulated a visual map where an interested candidate can read more about a particular program by hovering the cursor or mouse over the topic or certification.
For instance, (refer to the image below) the top boxes in green, orange, black, etc., contain programs that cater to security and risk management, security assessment and testing, software security and so on.
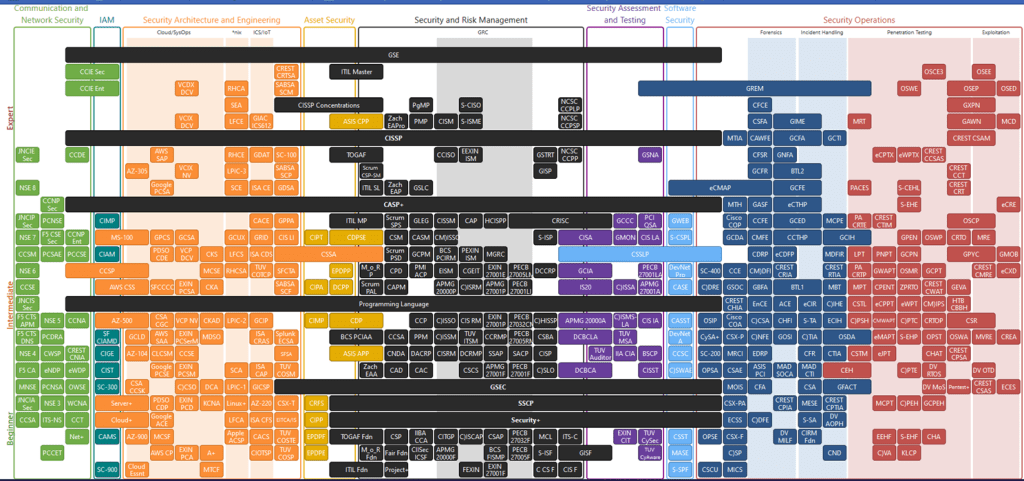
Cybersecurity certifications
Having a single certificate in the cybersecurity field adds to the candidate’s application. The certifications can be broadly divided into two parts, namely professional and academic.
- Professional cybersecurity certifications mainly cater to the staff who are working in the field of cybersecurity. It offers insights into some of the latest developments in the software and IT sector with reference to cybersecurity. CompTIA security plus is one such certificate. The department of defense also hires candidates with similar certifications.
- Academic cybersecurity certifications help young professionals or students gain deeper insights into recent cybersecurity happenings and issues. Harvard offers an online cybersecurity certification that also aligns with this category.
Some of the professional cybersecurity certifications are as follows:
- Certified ethical hacker (CEH) can be opted for by various officials, including network security officers, site administrators, IT specialists, etc. Candidates need to have an undergraduate degree or a high school diploma to pursue this course. Two years of experience in information security or being a graduate of EC-council training is required to join this course. Candidates can expect to learn cryptography, encryption techniques, code of ethics, computer security protocols, etc. Some educational institutions require candidates to have two or more years of experience in the information security area. Or, to attend training such as computer-based training offered by the institute.
- GIAC security essentials certification is opted by candidates who are relatively new to the field of information security but possess knowledge in networking. They may be auditors, penetration testers, security managers, or forensic analysts. This certification covers some topics, including learning about Linux, cloud, cryptography, access control, etc. There are no set requirements for who can take up this course. Any professional keen on learning or desires a career in cybersecurity may follow it.
- Certified information security manager (CISM) would offer in-depth specialization in governance, information security, risk management, etc. Those with prior experience in information security looking forward to managerial positions opt for this certification. The eligibility exam for opting for this course can be taken online or in person at a testing center, depending upon the institution. Candidates need five years of experience in a managerial role in the field of information security.
- Comp TIA security+ is one of the global certifications that offers training in core security functions. A candidate may be offered intermediate-level roles in cybersecurity. Candidates learn to identify, analyze and respond to online threats apart from monitoring and securing systems. One may learn about the Internet of things (IoT), cloud, enterprise environment, etc., through this certification. The benefit of Security+ is that it is approved by the United States department of defense (DoD) directive and is also compliant with ISO 17024 standards. No formal specifications are made for eligibility to take up this certification. However, IT professionals with two to ten years of IT administration experience are preferred.
- Certified information systems security professional (CISSP) opens the path to becoming an ISC2 member. ISC2 is an international association of cybersecurity workforce. ISC2 is a non-profit organization that offers certification for various cybersecurity roles. Applying candidates are expected to have a minimum of five years of paid work experience in either of the eight domains of the CISSP CBK. They are security and risk management, asset security, security architecture and engineering, communication and network security, identity and access management (IAM), security assessment and testing, security operations, and software development security.
Academic cybersecurity certifications may not be as full-fledged as professional cybersecurity certificates. It can last for a few months to a year or so. Such certifications may help add to the present credentials, be helpful for graduates for a career in this field or to make a career change from another field. Candidates can choose from various programs like a certificate in advanced digital forensics, certificate in network security, certificate in digital forensics, advanced cyber defender certificate, healthcare information security certificate, post-baccalaureate digital forensics, incident handling, and so on.
Here are details of some of the academic cybersecurity certifications:
- Managing risk in the information age certificate is a short-term course to start a career in cybersecurity. After completing the course from Harvard, the candidate is presented with a certificate from Harvard University’s office of the provost for advances in learning. It has modules that cover various topics, including cybersecurity as a business risk, identifying threats, leadership in managing cyber risk, and incidence response, among others.
- Information systems cybersecurity certificates for professionals can help students understand foundational cybersecurity technology, build data systems, conduct penetration testing, and so on.
- The Cybersecurity certificate offered by the University of Maryland is open for the undergraduate and graduate students. Both levels require 15 and 18-credit hours, and the course lasts for a year. This certification may help prepare candidates with computer networking for other cybersecurity professional exams that they may need for future growth.
Universities that offer these certifications are Worcester polytechnic institute, Wayne country technical college, Washington University in St Louis, Valencia College, University of Pittsburg campus, SUNY at Albany, San Jose state university, Sacramento city college, and City College of San Francisco.
Overview of some of the most popular cybersecurity positions
Online safety is never expected to be in lesser demand because of the increasing use of the internet and the devices that work using the internet. The spending on cybersecurity to secure systems and data has gone over billions of dollars in the recent past. Governments across the globe are increasing the sum allocated for their cybersecurity budgets. Several vacant positions need to be filled in order to create a robust team. The education and certification needed in some of the positions in the cybersecurity field are:
1. Information security specialist
Also called cybersecurity or computer security specialists, they need to be knowledgeable in up-to-date programming and computer science with a BA. They need either certified information systems security professional (CISSP), a certified ethical hacker (CEH), or a systems administration and network security (SANS) certification.
Their salary ranges between $59k to $157k
2. Security consultant
This is a contract job that has a specialization in the area of cybersecurity. They typically work at a consulting firm. A general certification for a security analyst from the international association of professional security consultants will help.
Their salary ranges between $60k to $158k
3. Information security engineer
Having a bachelor’s degree in engineering, computer engineering, or computer science is required for this position. Companies may prefer candidates with a master’s degree over a bachelors. Certification in certified ethical hackers, certified information systems, security professionals (CISSP), and security related CIAC certification will help. Some companies may even hire candidates despite not having a certificate based on their prior experience, which may help in this field.
Their average salary ranges between $74k to $152k.
4. Information security manager
Candidates can join as an information security manager with a bachelor’s degree in the relevant information technology and experience of minimum of five years in the relevant fields. A certified information security manager (CISM) and certified information systems security professional (CISSP) will help in being considered for this position.
Their salaries range between $88k to $196k.
5. CISA: Certified information systems auditor
One of the most prestigious certifications, the CISA certified information systems auditor, is open for candidates with five years of IT auditing or assurance experience. Professionals who are certified by the cybersecurity and infrastructure security agency (CISA) in the field of information systems auditing, IT management and governance, or protection of information assets opt for a career using this certificate.
6. IT security architect
Having a bachelor’s degree in computer security or computer science and a minimum of five years of relevant work experience is required. They are exposed to business and IT infrastructure, which helps them make tremendous improvements in planning and implementing an organization’s computer and network security infrastructure.
Their salary ranges between $70k to $160k.
7. Information security director
A bachelor’s degree in a relevant discipline with IT experience is needed to apply for this position. Good security skills and a managerial attitude is expected from candidates applying for this role in their career.
Their salary ranges between $123k to $237k.
8. CISO
CISO or CSO requires a bachelor’s degree in computer science or any other relevant field. They also need a minimum of 5 years of experience in a management role and knowledge of security technology, practices, and industry regulations.
Their salary ranges between $105k to $264k.