The infrastructure behind HIVE ransomware group has been taken down in a coordinated action of law enforcement agencies in the United States and Europe. The action was led by the U.S. Department of Justice, the FBI, and the Secret Service, with assistance from European government agencies.
“Last night, the Justice Department dismantled an international ransomware news network responsible for extorting and attempting to extort hundreds of millions of dollars from victims in the United States and around the world,” said US Attorney General Merrick B. Garland in a Department of Justice press release on 26 January.
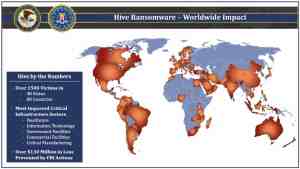
Image courtesy: europol.europa.eu
“This hidden site has been seized. The Federal Bureau of Investigation seized this site as part of a coordinated law enforcement action taken against Hive Ransomware,” said a seizure notice on Hive’s dark web leak site.
“This action has been taken in coordination with the United States Attorney’s Office for the Middle District of Florida and the Computer Crime and Intellectual Property Section of the Department of Justice with substantial assistance from Europol.”
According to Europol, the United States Secret Service and the FBI worked with them along with the following law enforcement agencies in this operation:
Royal Canadian Mounted Police (RCMP) & Peel Regional Police (Canada), Police Nationale (France), Federal Criminal Police Office and CID Esslingen (Germany), National Police (Ireland), Criminal Police Bureau (Lithuania), National Police (Netherlands), National Police (Norway), Judicial Police (Portugal), Romanian Police (Romania), Spanish Police (Spain), Swedish Police (Sweden), and the National Crime Agency (United Kingdom).
Image courtesy: twitter.com/FBI
FBI dismantles Hive ransomware servers
According to the DoJ announcement, the FBI managed to break into Hive’s computer networks in July 2022, obtained its decryption keys, and used them to help victims worldwide, preventing a total ransom payment of $130 million globally.
“Since infiltrating Hive’s network in July 2022, the FBI has provided over 300 decryption keys to Hive victims who were under attack. In addition, the FBI distributed over 1,000 additional decryption keys to previous Hive victims,” said the DoJ press release.
Hive, which operates a ransomware-as-a-service model, previously targeted a wide range of industries and critical infrastructure, with a focus on healthcare and public health entities.
The FBI has also begun dismantling Hive’s front and back-end infrastructure in the U.S. and abroad, which included the seizure of two of Hive’s backend servers located in Los Angeles.
The FBI did not disclose how it identified the Hive servers, and no arrests or indictments were announced during the press conference.
“Cybercriminals utilize sophisticated technologies to prey upon innocent victims worldwide,” said U.S. Attorney Roger Handberg in the press release.
“Thanks to the exceptional investigative work and coordination by our domestic and international law enforcement partners, further extortion by HIVE has been thwarted, critical business operations can resume without interruption, and millions of dollars in ransom payments were averted.”
HIVE ransomware: Mode of operation
HIVE ransomware group was among the six gangs flagged in 2022 by the Cybersecurity & Infrastructure Security Agency (CISA) as the upstarts of 2022.
HIVE ransomware has been used by criminals to target various industries and critical infrastructure since June 2021, including government facilities, telecommunication companies and media, manufacturing, energy, information technology, and healthcare and public health, said an FBI flash alert issued in November 2022.
“The method of initial intrusion will depend on which affiliate targets the network. Hive actors have gained initial access to victim networks by using single factor logins via Remote Desktop Protocol (RDP), virtual private networks (VPNs), and other remote network connection protocols,” said the FBI flash alert.
“In some cases, Hive actors have bypassed multifactor authentication (MFA) and gained access to FortiOS servers by exploiting the vulnerability CVE-2020-12812. This vulnerability enables a malicious cyber actor to log in without a prompt for the user’s second authentication factor (FortiToken) when the actor changes the case of the username.”
According to Europol, over 1,500 companies from over 80 countries worldwide have fallen victim to HIVE associates since June 2021, and lost almost EUR 100 million in ransom payments.
“Affiliates executed the cyberattacks, but the HIVE ransomware was created, maintained and updated by developers,” said the Europol announcement.
“Affiliates used the double extortion model of ‘ransomware-as-a-service’; first, they copied data and then encrypted the files. Then, they asked for a ransom to both decrypt the files and to not publish the stolen data on the Hive Leak Site. When the victims paid, the ransom was then split between affiliates (who received 80%) and developers (who received 20%).”