A GitHub vulnerability has recently caught the attention of researchers. The vulnerability threatens multiple GitHub repositories, even affecting the users who are part of it.
The vulnerability exploits the “race condition” within GitHub’s repository creation and username renaming operations, potentially allowing attackers to hijack repositories for distributing malicious code.
A race condition, in this particular situation, refers to an event within GitHub where a device or system tries to perform two or more functions together — making it difficult for operations to be executed in a proper sequence.
This sequence is important for many applications because, otherwise, the connection would break — leaving vulnerabilities to be exploited in this path. In this particular case, attackers use RepoJacking attacks to target GitHub repositories.
New GitHub Vulnerability and RepoJacking Attacks

The vulnerability, though not given a CVE ID or score, allows threat actors to use RepoJacking attacks by exploiting the renamed users in a particular repository.
RepoJacking attacks are a popular hacking technique where a threat actor can take over the user accounts on the repository.
“By gaining access to the account, the attacker can inject malicious code into projects that use the repository as a dependency”, reads the report by Kratikal.
In this case, the attacker can use RepoJacking attacks to gain control of namespaces on GitHub, which is, according to Checkmarx, “a combination of the username and repo name (e.g., example-user/example-repo).”
Checkmarx report denotes that the vulnerability potentially impacts over 4,000 code packages in languages such as Go, PHP, and Swift, as well as GitHub actions.
However, since this GitHub vulnerability has started taking a toll on users, GitHub has issued a fix.
Technical analysis of GitHub vulnerability and RepoJacking attacks
To better understand this GitHub vulnerability, GitHub has mentioned the chain hackers use to perform RepoJacking attacks.
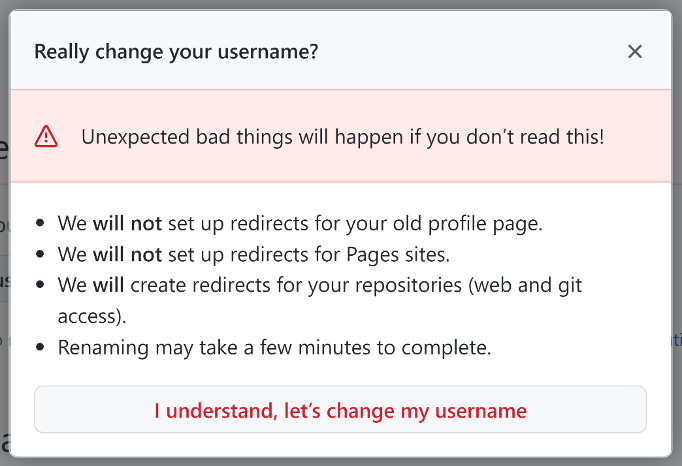
In the initial phase of the attack, the attacker looks for users who have recently changed their username on GitHub. Once the new username has been registered, the old username becomes available for anyone to use.
Now, hackers use these old usernames and claim them. The hackers can now open a repository under the “matching repo name and hijack the namespace.”
Here is a quick look at the exploitation method used by threat actors to “bypass GitHub checks.” The demonstrated was shared by Checkmarx SCS Group Architect Elad Rapoport.
- The victim owns the namespace “victim_user/repo.”
- Victim renames “victim_user” to “renamed_user.”
- The “victim_user/repo” repository is now retired.
- An attacker who owns the username “attacker_user” prepares a command that practically simultaneously creates a repo called “repo” and renames the username “attacker_user” to the victim’s username, “victim_user.”
- This is done using an API request for repository creation and a renamed request interception for the username change.
Now, upon successful exploitation, the vulnerability could allow threat actors to take over widely used code packages across various package managers, including prominent ones like “Packagist,” “Go,” and “Swift.”
Furthermore, exploiting this vulnerability extends to the commandeering of popular GitHub actions, with potentially severe implications for supply chain security.
Recent investigations have highlighted the gravity of this vulnerability, revealing that major entities like Google and Lyft were initially susceptible.
To counter RepoJacking attacks, Checkmarx has advised to avoid using retired namespaces and thoroughly inspect code for any dependencies leading to vulnerable GitHub repositories.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.




















































