Security researchers detected a new attack vector in Azure Active Directory (AAD) that allowed them to alter the search results of Microsoft Bing, potentially exposing and compromising the personal data of millions of Bing users.
In a report published by IT security company Wiz, the researchers highlighted how the attack vector, which is based on a common AAD misconfiguration, allowed unauthorized access to misconfigured apps.
Several Microsoft applications and Content Management System (CMS), which powers Bing, were left vulnerable. Through this, they were able to “take over Bing.com functionality, modify search results, and potentially enable the Office 365 credential theft of millions of Bing users,” stated the report.
With the help of these credentials, the researchers could easily access the users’ private emails and documents.
The research also highlighted how the vulnerability could be easily exploited without a “single line of code.”
Following the research, the detected issues were disclosed to Microsoft, which modified the AAD functionality to “reduce customer exposure” and “fixed its vulnerable applications,” the report stated.
How the Microsoft authorization misconfiguration was identified
Wiz researchers unearthed how internal applications were exposed to external threat actors by performing red teaming using search results on the Bing search engine.
They also performed XXS attacks on Bing that led to the discovery that Microsoft Office 365 user data was vulnerable upon exploiting the Microsoft authorization configuration error.
The vulnerable user data included –
- Email addresses
- SharePoint documents
- Chat messages
- Outlook emails
- Calendar entries
- OneDrive files
Single Sign-On (SSO) is an authentication mechanism in Azure App Services. AAD offers account access including single-tenant, multi-tenant, a combination of two, personal accounts, etc.
Cybercriminals had the opportunity to add an authentication function, log in to the application, access the Content Management System (CMS), and so on.
Case study to explain Microsoft Bing authorization misconfiguration
Affected Microsoft applications included the following –
- Mag News which serves MSN newsletters
- CNS API which works as Microsoft’s central notification service
- Contact Center which caters to the call center agents of the company
- PoliCheck which filters forbidden words in Microsoft codes
- Power Automate Blog which is a WordPress admin panel
- Cosmos which is a file management system
The “BingBang” in the Microsoft Authentication Misconfiguration
Naming this attack vector “BingBang”, researchers dug deep into the exploitability of the misconfiguration. They were awarded a bug bounty of $40,000 for their exemplary research that saved data loss and privacy breaches, among other issues.
Upon trying to create an account bingtrivia.azurewebsites.net, it was found that logging in was allowed despite not being a part of Microsoft tenant.
Several core Bing content was reflected on the screen which led researchers to ponder over the exploitability of the tabular ‘Carousels’ section, quizzes and background images, etc., on Bing.
It was found that the carousel was open to being altered on the CMS, changes could have been reverted, saved, or edited further which would reflect on Bing.com. It would reflect on the Bing title, thumbnail, and arbitrary link.
Bing search results, including results on its homepage, could have been controlled by misusing the Microsoft authentication bypass.
To further understand the impact of this authentication bypass, XSS viability was tested with a harmless payload. This confirmed the scope of unauthorized access to Wiz.
Previously reported bugs in Microsoft
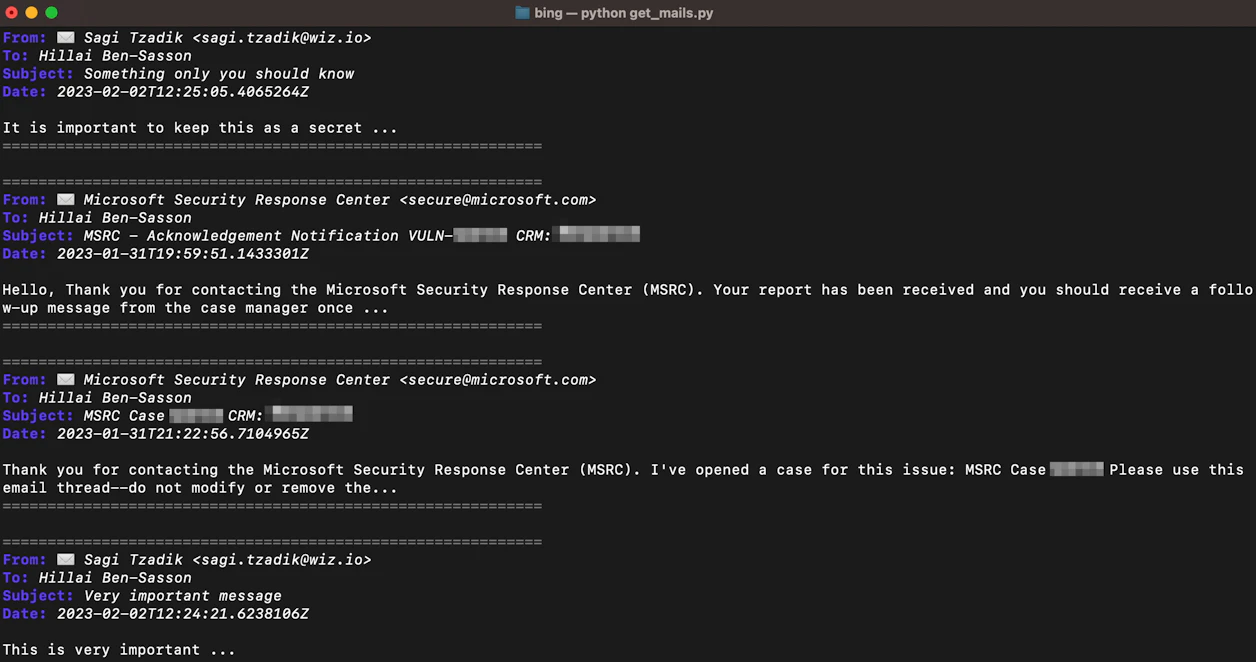
Earlier, Wiz reported bugs in Bing to Microsoft in January, which were promptly fixed the same day. Other vulnerabilities reported on February 25 were addressed starting February 27 which concluded on March 20.




















































