When Rackspace Hosted Exchange service faced a ransomware attack in December, the root cause was traced to a zero-day exploit related to a Microsoft Exchange vulnerability (designated as CVE-2022-41080). This allowed hackers to gain access to multiple accounts and caused tens of thousands of users to lose access to their previous emails.
It was discovered that the vulnerability in Microsoft Exchange can lead to an elevation of privileges. This weakness can be combined with the CVE-2022-41082 ProxyNotShell bug to achieve remote code execution. Cybercriminals have been exploiting this critical vulnerability to gain remote privilege escalation on Microsoft Exchange Server.
Researchers since then have been spotting several such instances. The Cybersecurity and Infrastructure Security Agency (CISA) added security weaknesses in its database of exploited bugs, within days after the Rackspace incident came to light.
Despite repeated instances, the CISA notice, and even a call of action from Microsoft for patch management, many organizations are yet to initiate a patch, The Cyber Express found.
Microsoft Vulnerability: Big bug and no patch?
A spot survey conducted by The Cyber Express among our registered readers found that many of them were unaware of the impact of the vulnerability.
Out of about 40 cybersecurity leaders and executives who were surveyed from various industries and locations, just about 20% took action to patch the bug after being alerted in January. Surprisingly, close to 40% of them still have not updated their systems completely.
In a report, CrowdStrike noted that the exploit ‘OWASSRF’ consists of two vulnerabilities that allow remote code execution through Outlook web access.
Attackers leveraged their attack vector for ProxyNotShell to Remote PowerShell and gained initial access.
Microsoft alerted that Cuba ransomware used the zero-day exploit named OWASSRF flaw to hack Microsoft Exchange servers. They also bypassed the ProxyNotShell URL rewrite mitigations, confirmed Texas-based cloud computing provider Rackspace.
Old flaws in Microsoft Exchange Server
Several flaws in Microsoft Exchange Server, disclosed across the past two years, still continue as keyholes for ransomware gangs.
ProxyShell, which was a set of Exchange Server vulnerabilities, was disclosed in August 2021 following which threat actors were found looking for vulnerable exchange servers in ProxyLogon and ProxyShell.
Tenable noted that ProxyLogon (CVE-2021-26855) and CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065 were exploited as zero-day vulnerabilities by HAFNIUM, a state-sponsored cybercriminal group.
Unpatched on-premises Exchange systems hold valuable information waiting to be exploited, warned Microsoft.
For example, user mailboxes often contain sensitive data and every Exchange server contains a company address book, which provides useful information for social engineering attacks such as organizational structure, job titles, and contact information.
Additionally, Exchange has extensive access to Active Directory and in hybrid environments, it has access to the connected cloud environment as well.
“We’ve said it before, we’re saying it now, and we’ll keeping saying it: it is critical to keep your Exchange servers updated,” said the Microsoft blog post calling for urgent patching.
ProxyNotShell patch
Microsoft offered mitigation guidance for two months of the ProxyNotShell being disclosed in September 2022.
No patches were issued until November 8, which came about a month after the flaw was disclosed. Moreover, a mitigation bypass was found in OWASSRF that let cybercriminals bypass the mitigation offered for ProxyNotShell by exploiting CVE-2022-41080.
Organizations that did not apply the patch for the vulnerabilities offered in Microsoft’s November Patch Tuesday remain vulnerable to attacks found in 2022. Those following the mitigation guidelines are not fully protected against cyberattacks and were urged to patch the flaws.
Researchers at Viettel Security pointed out that the OWASSRF with CVE-2022-41080 can enable remote code execution in PowerShell despite being patched in December 2022.
After conducting tests, they were able to exploit both vulnerabilities to enter the PowerShell sandbox to execute arbitrary PowerShell cmdlets.
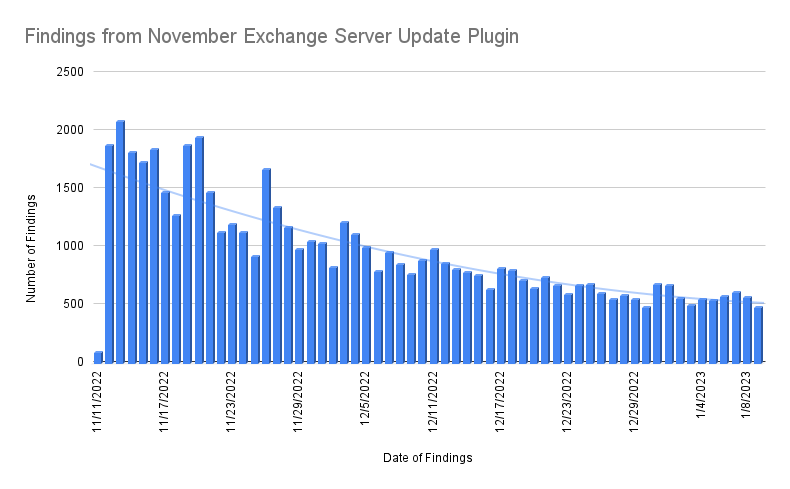
(Image: Tenable)
Tenable used a plugin to gauge the number of vulnerable Exchange servers and found that even though the number of servers has decreased from November 2022 to January 2023, there are still users that need to patch their systems. Even if ProxyNotShell mitigation measures were followed, servers are vulnerable to Exchange server flaws that hackers have been exploiting.
The latest Exchange security updates must be applied with the November 2022 patch. Or organizations need to disable Outlook Web Access until the vulnerabilities are patched to avoid being vulnerable to cyberattacks.