Following the Hensoldt attack earlier this year, Lorenz ransomware has exploited a critical vulnerability in Mitel MiVoice VOIP appliances. The threat actor used the vulnerability to breach companies using their phone systems.
The new technique enabled malware to access corporate networks and steal sensitive information. Researchers at Arctic Wolf Labs spotted Lorenz ransomware’s occurrence, exploiting the CVE-2022-29499 bug for initial access. After observing a significant overlap with Tactics, Techniques, and Procedures (TTP), Crowdstrike reported the initial attack in June 2022 and shared its findings on its blog. After linking the recent ransomware attacks, Arctic Wolf Labs confirmed a high probability that the Lorenz gang could be behind these attacks.
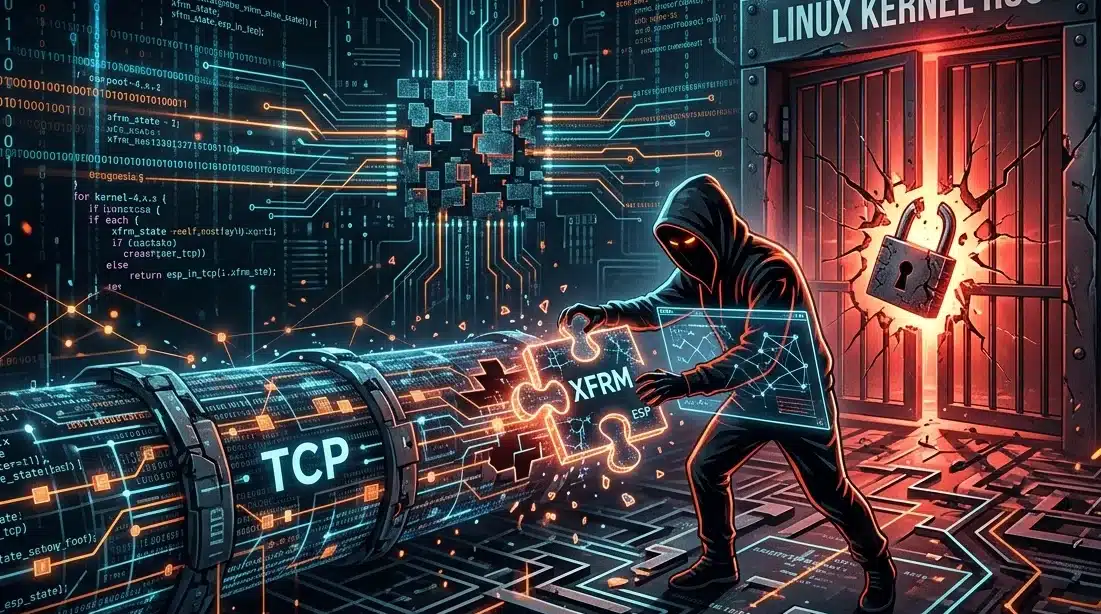
Lorenz ransomware gang exploits CVE-2022-29499
Lorenz ransomware gang exploited CVE-2022-29499, a widespread remote vulnerability, basically found in the Mitel Service Appliance component of MiVoice Connect. By controlling the bug, hackers can obtain a reverse shell that can be used with a Chisel tunneling tool to pivot into the environment, per the Arctic Wolf Labs report.
Mitel Voice-over-IP (VoIP) products are popular among organizations, further enhancing the ransomware capability to attack different sectors and organizations using a vulnerability within all the VoIP systems. According to sources, there are currently over 19,000 devices exposed to potential attacks, and these attacks can be detrimental if not stopped earlier.
Post the incident report, Mitel addressed the issues about the vulnerability and has already released security patches for all the devices and systems. It also released a remediation script for affected MiVoice Connect versions, advising the users on how and what to do in these attacks.
About Lorenz ransomware gang
The Lorenz ransomware gang was observed since December 2020 and has been involved in many extortion cases where it demanded hundreds of thousands of dollars from its victims. According to sources, the Lorenz ransomware gang is actively selling stolen data from enterprises. It pressures the victims to pay the ransom with the threat of selling their data to cyber criminals, which fetches them vast sums of money.
The gang uses reverse tactics to harass the victims by leaking the stolen files using password-protected RAR archives. When the victims refuse to pay the ransom, Lorenz also releases the passwords to the leaked files on hacking forums.