American-based multinational technology conglomerate Cisco confirmed that the recent data posted by Yanluowang ransomware on the dark web was stolen during the cyberattack the company suffered earlier this May.
Cisco Tale Intelligence Group confirmed that the content posted by the threat actor and the one that was stolen was the same.
“On September 11, 2022, the bad actors who previously published a list of file names from this security incident to the dark web, posted the actual contents of the same files to the same location on the dark web. The content of these files match what we already identified and disclosed,” stated the official update. However, the company reaffirmed that the publicizing of data by hackers did not impact its employees, businesses, and partners.
The company earlier confirmed the attacks last Wednesday, where the Lapsus$ Gang took advantage of Cisco’s network by hacking into an employee’s personal Google account that later helped the hackers access all the saved passwords and login details on the network. According to sources, hackers stole 2.8GB of data and released it on the dark web.
Lapsus$ Gang
Lapsus$ Gang initiated the hack by repeatedly attempting to gain access to the Cisco network. The company first became aware of a potential breach on May 24, 2022. According to reports, the hackers seized and released files on the dark web. Sources claim that the hackers exploited a worker’s personal Google account, which was synced to store crucial login information and passwords.
The hackers then used the standard phishing techniques. They pursued other employees to accept a multifactor push authentication notification on their devices, allowing the hacker to access Cisco’s network using the employee’s credentials.
According to Cisco, the hackers didn’t gain access to the internal systems files, such as product development, code signing, etc. However, the group successfully infiltrated the data and compromised the contents of a Box folder associated with the target employee’s account. The company claims the compromised data was not sensitive and did not harm the company, its products, and its employees.
Stolen data published on the dark web
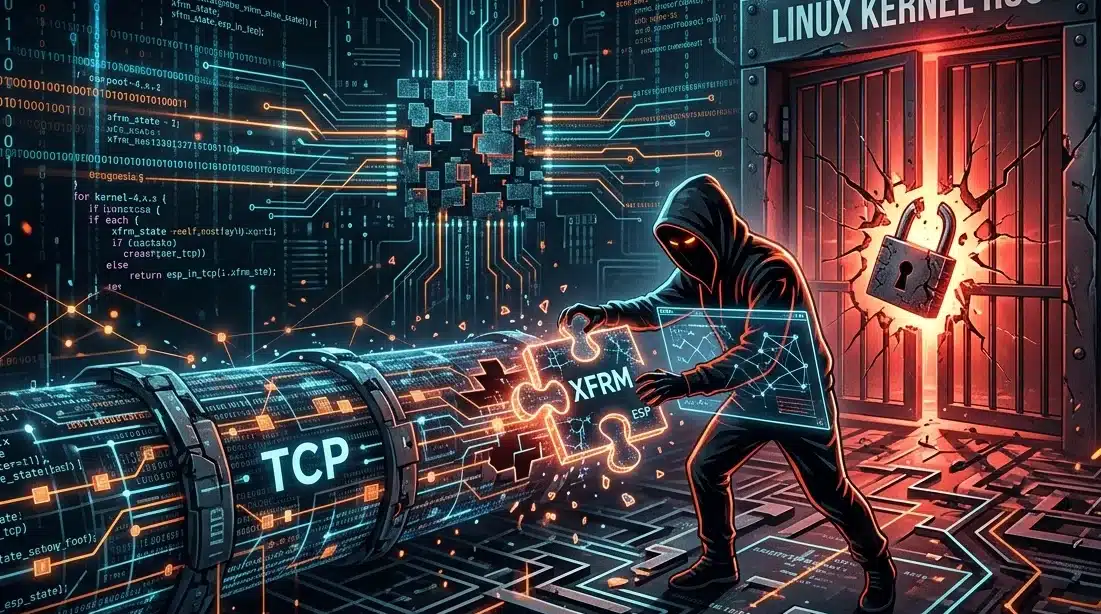
In Cisco’s case, the hackers stole 2.8GB of non-sensitive data using Yanluowang and posted it on the dark web. Though no customers, employees, or product information has been leaked, the company has revoked the attacker’s access to its network and neglected to pay any amount to the hackers to avoid disclosure.
Named after the Chinese deity Yanluo Wang, Yanluowang is a new ransomware and includes code-signed files. It can terminate various processes of the target devices, including database and backup management. This malware has been linked to cyber campaigns since last year, particularly those that target US corporations.
Last night #yaluowang posted #Cisco as a victim. Cisco has confirmed an incident and provided a comprehensive report.
A single staff credential was compromised.
Cisco were able to remove and remidiate the threat. #cybersecurity #ransomware #infosechttps://t.co/lB7DXlMaXa pic.twitter.com/jeEDEi7xPi
— CyberKnow (@Cyberknow20) August 10, 2022
While finding out about the breach, Cisco claimed that “Based upon artifacts obtained, tactics, techniques, and procedures (TTPs) identified, the infrastructure used, and a thorough analysis of the backdoor utilized in this attack, we assess with moderate to high confidence that this attack was conducted by an adversary that has been previously identified as an initial access broker (IAB) with ties to both UNC2447 and Lapsus$ Gang,” adding that the attack was also linked to Yanluowang ransomware gang.