A cancer patient getting treatment at Lehigh Valley Health Network (LVHN), Allentown, Pennsylvania had filed a class action lawsuit against the healthcare after her partially naked pictures taken in the exam room were stolen and leaked on a ransomware leak site.
The images were leaked following the Lehigh Valley Health Network Data Breach incident when the negotiation talks between the organization and hackers failed.
The lawsuit, filed on March 13, alleged that Lehigh Valley Health Network prioritized “money over patient privacy” by refusing to pay the ransom.
According to a news report, the pictures of the plaintiff, identified as “Jane Doe”, and others were taken during the stages of undress for the breast cancer radiation treatment.
The partially naked photos were posted on the leak site following the ransomware attack on Lehigh Valley Health Network by the BlackCat ransomware group.
What the Lehigh Valley Health Network class action lawsuit said
The Lehigh Valley Health Network class action lawsuit was filed in Lackawanna county, Pennsylvania by “Jane Doe”.
The statement released by law firm Saltz Mongeluzzi & Bendesky alleged that the defendant LVHN suffered a data breach on February 6, 2023.
After watching media coverage of the Lehigh Valley data breach on February 28, “Jane Doe” contacted her physician inquiring whether her personal data was leaked. Jane said that she had no inkling that her nude photos were on LVHN’s network.
Often data breaches result in the loss of personally identifiable information such as addresses, emails, and dates of birth among others. However, the LVHN breach exposed photographs taken in the nude that were often taken without the knowledge of the patient, the lawsuit concluded.

The cybercriminals behind the LVHN data breach threatened to release sensitive images publicly if a ransom was not paid.
The Lehigh Valley Health Network class action lawsuit alleged that the defendant made the “knowing, reckless, and willful, decision to let the hackers post nude images of Plaintiff and others on the internet.”
Lehigh Valley Health Network also violated HIPAA by not following reasonable measures to protect the PII and PHI of the victims.
On the counts of wrongful conduct, misrepresentation, concealment, and unlawful practices, the Lehigh Valley Health Network class action lawsuit was filed.
The Lehigh Valley Health Network ransomware attack
The Lehigh Valley Health Network first detected unauthorized access on its IT system on February 6. Three intimate photos of patients were posted online by BlackCat ransomware. The images were of cancer patients receiving radiation oncology treatment.
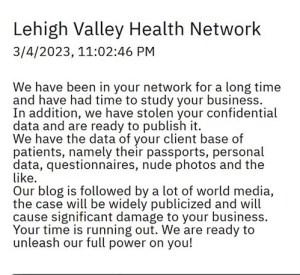
The Lehigh Valley Health Network class action lawsuit statement had images from BlackCat’s website as shown above that read, “Our blog is followed by a lot of world media, the case will be widely publicized…. Your time is running out.”
The threat mentioned that sensitive files of the client base like passport data, photos, and questionnaires were with BlackCat.

The LVHN provides healthcare services to over 2,400 new patients annually. The website of Lehigh Valley Health Network – https://www.lvhn.org/ was inaccessible at the time of writing.
BlackCat ransomware group
The Russian-linked BlackCat ransomware group, a successor to REvil was first detected in 2021.
The group also called ALPHV has had several warnings and reports released against them from legal authorities in relation to its increasing cyberattacks, especially in the healthcare sector.
Ransom payment against stolen data has been deterred by legal authorities because it only encourages cybercriminals and they do not decrypt all of the data after receiving the ransom.




















































