Days after one of the biggest hospital chains in the US disclosed that hackers obtained protected health information for 1 million patients, researchers have traced the root to a vulnerability in an enterprise software product GoAnywhere.
Community Health Systems of Franklin, Tennessee filed a report with the Securities and Exchange Commission on 13 February, confirming that the access was through GoAnywhere MFT.
The data breach at Fortra’s GoAnywhere did not cause any delay in patient care, the report further clarified.
“Upon receiving notification of the security breach, the company promptly launched an investigation, including to determine whether any company information systems were affected, whether there was any impact to ongoing operations, and whether and to what extent PHI or PI had been unlawfully accessed by the attacker,” said the SEC disclosure.
With regard to the PHI and PI compromised by the Fortra breach, the company currently estimates that approximately one million individuals may have been affected by this attack,” it added.
Community Health, GoAnywhere, and data breach
Fortra’s GoAnywhere was exploited using the vulnerability CVE-2023-0669 which the company alerted on February 1.
The then-known zero-day GoAnywhere vulnerability impacted its managed file transfer (MFT) application. The application received a patch on February 7 with version 7.1.2.
The CVE-2023-0669 was a remote code execution vulnerability that needed access to the administrative console to be exploited. Access to the administrative console is achieved through a private company network, VPN, allow-listed IP addresses in cloud environments, etc.
The client interface accessed via the public internet was not vulnerable to this threat, according to a blog post by the cybersecurity company Qualys.
GoAnywhere vulnerability exploitation
Researchers came across instances of exploitation of CVE-2023-0669 using Truebot-styled persistence arranging scheduled tasks for coded execution using Rundll32. Taking inputs from several threat intelligence sources, Qualys confirmed the following details;
- hash.sha256:[“0e3a14638456f4451fe8d76fdc04e591fba942c2f16da31857ca66293a58a4c3”, “c042ad2947caf4449295a51f9d640d722b5a6ec6957523ebf68cddb87ef3545c”, “c9b874d54c18e895face055eeb6faa2da7965a336d70303d0bd6047bec27a29d”]
- properties.certificate.issuer:”Sectigo Public Code Signing CA R36″ and file.properties.certificate.hash:”82d224323efa65060b641f51fadfef02″
Post-exploitation Indicators of Compromise (IoC):
- 0e3a14638456f4451fe8d76fdc04e591fba942c2f16da31857ca66293a58a4c3
- c042ad2947caf4449295a51f9d640d722b5a6ec6957523ebf68cddb87ef3545c
- C9b874d54c18e895face055eeb6faa2da7965a336d70303d0bd6047bec27a29d
Mitigation efforts for the GoAnywhere vulnerability
A workaround for this GoAnywhere vulnerability was noted on February 3 before the patch was released, BleepingComputer reported.
Users who are finding it difficult to update the software to its latest version may follow these steps outlined by Qualys until the issue is resolved:
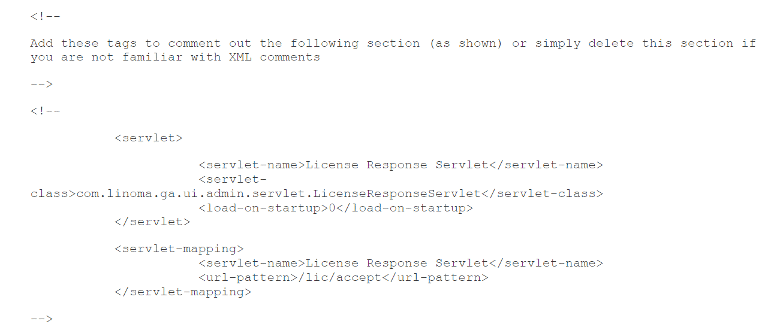
- Disable the LicenseResponseServlet by opening the file system where GoAnywhere MFT is installed.
- Edit the [install_dir]/adminroot/WEB-INF/web.xml- file
- Delete or comment out the servlet and servlet-mapping configuration.
- Restart GoAnywhere MFT app
After deletion of the servlet and servlet-mapping (Photo: Qualys)
A report by cybersecurity researcher Brian Krebbs read that if someone’s administrative interface was publicly exposed and they were not able to apply the required access controls to the interface, they can review and evaluate their administrative user accounts for suspicious access, and unrecognized usernames.
They can then check the details of the new usernames by clicking on the cog icon next to it and selecting ‘view.’ The official company advisory also urged users to investigate if they found any new admin accounts being created under ‘system,’ as they may be the work of cybercriminals.
The suspicious timings (while the vulnerability may still be unpatched in some systems) in creating newer accounts may also giveaway threat actor accounts. The Cyber Express reached out to Fortra’s GoAnywhere for comment. No response has been received so far.