In the latest cybersecurity news, a new information stealer that goes by the name “Laze Stealer” is being advertised. This information stealer, still in its developmental phase, is engineered with a sinister purpose – to pilfer sensitive information from a target’s device.
The information stealer was first advertised on Github by a user named xKiian Kian. The German Github user uploaded the information stealer on October 11, 2023, bringing the attention of hackers and cybersecurity experts.
What is Laze Stealer?
According to the post, this information stealer is hailed as the “most powerful stealer” capable of executing an array of functions. However, being in its developmental stage, it falls short in certain aspects when compared to its more established counterparts.
Laze Stealer casts a wide net, aiming to pilifer various types of critical data from the victim’s system. This encompasses Discord account particulars such as emails, phone numbers, and payment information.
Additionally, it ventures into browser territory, seeking passwords, cookies, and even credit card data. Furthermore, it doesn’t stop there, extending its reach to cryptocurrency wallets across an array of browsers and desktop applications.
A Closer Look at Functionality

For Discord users, the information stealer infiltrates various aspects of the platform including email, phone, billing information, badges, Nitro, Mfa, Token, HQ Servers, and HQ Friends.
When it comes to browsers, it sets its sights on popular browsers, such as Chrome, Chrome SxS, Chrome Beta, Chrome Dev, Chrome Unstable, Chrome Canary, Brave, Vivaldi, Yandex, Edge, and the ever-popular Firefox.
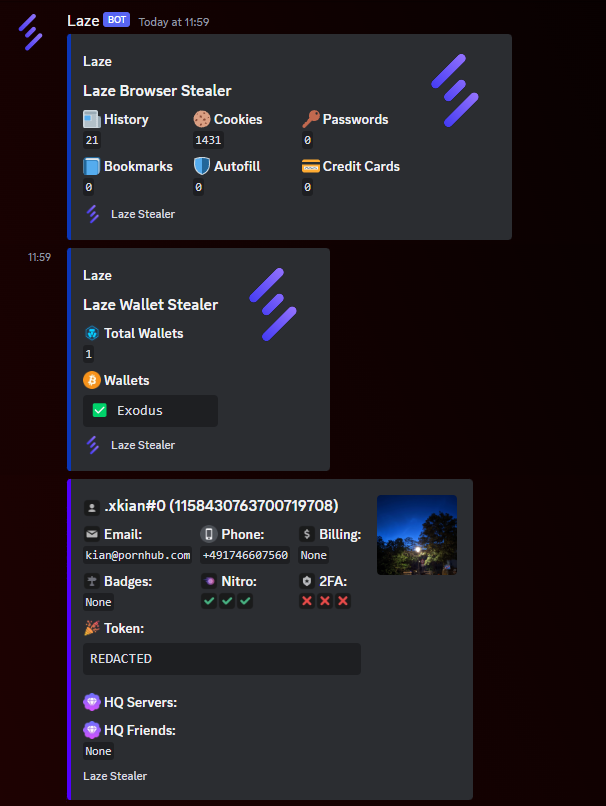
The list of pilfered data is comprehensive, ranging from passwords and cookies to history, bookmarks, autofill information, and credit card details.
For wallets, Laze Stealer exhibits a long range of tactics, targeting well-known names like Metamask, Binance, and Coinbase, along with a plethora of others.
The theft isn’t confined to browsers alone; it extends to desktop applications such as Atomic, Armory, Coinomi, and Jaxx Liberty.
Limitations and Claims
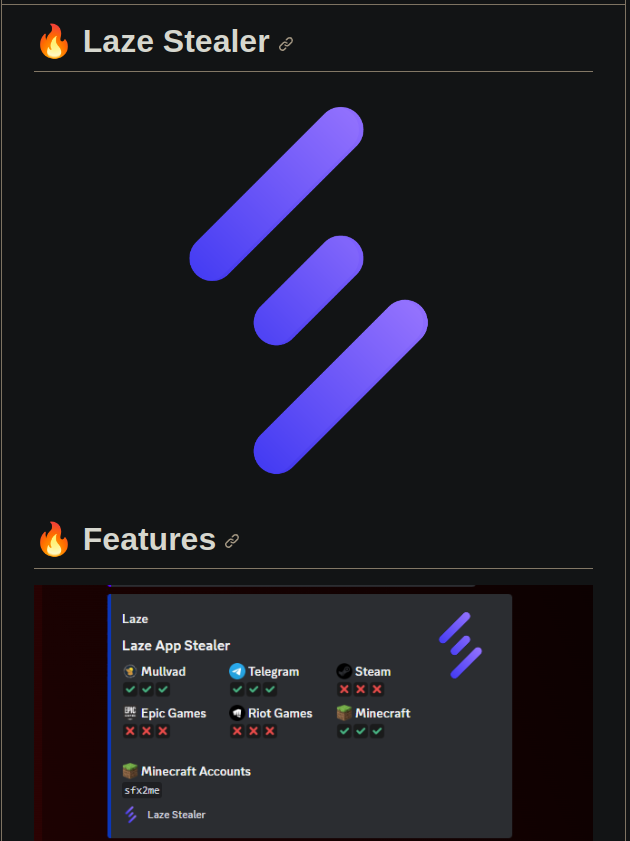
Although the advertisement touts Laze Stealer’s ability to plunder data from platforms like Mullvad, Telegram, Steam, Epic Games, Riot Games, and Minecraft, the user behind this information stealer has clarified that it is currently functional only for Mullvad, Telegram, and Minecraft.
Moreover, the user has divulged additional insights, revealing that Laze Stealer is equipped with a webhook protector/backend and a data encryptor.
The stolen data is compiled into a single compressed file and sent with the password “@Laze. It’s important to note that the code may contain bugs, and the user has explicitly stated they will not offer assistance.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.






















































