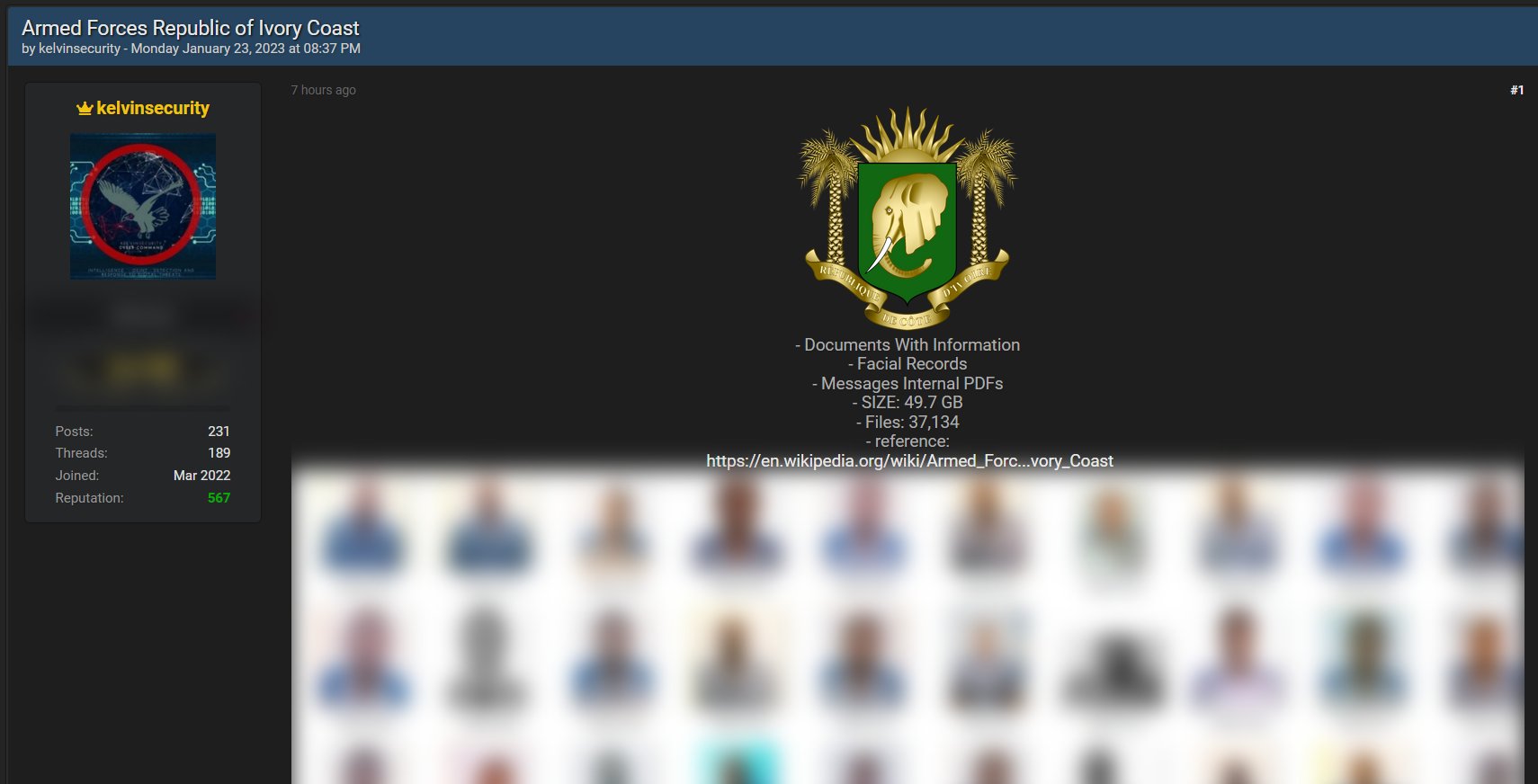
A database allegedly from the systems of the Ivory Coast armed forces — Armed Forces of the Republic of Ivory Coast — has been put on sale by KelvinSecurity. The cybercriminals claimed to have nearly 37,134 files amounting to 49.7 GB of data which can be bought on the hacker’s forum.
The post claiming to have Ivory Coast armed forces data (Source: FalconFeedsio)
The group claimed to have facial records and internal PDFs supposedly of messages from the systems of the Ivory Coast armed forces, according to a tweet by FalconFeedsio.
The changing shape of ransomware data leaks
Cyble Research and Intelligence Labs (CRIL) published its Q4 – 2022 ransomware analysis that pointed out that even though ransomware activities showed a decrease in Q3, they increased in Q4.
The Cyber Express has been closely following hacker and breach forums, based on which it could be inferred that several ransomware groups are trying to make the most of the data of previously hacked organizations available on the forum.
Ransomware groups are resharing links to downloads either for free or for a price likely based on the interest of the members seeking it.
While data from the Adidas breach is considered a hot commodity for sale despite the cyberattack being over 2 months old, Luxottica’s breached data has been made available for free on hacker forums and leak sites.
The rise and fall of threat actors
CRIL researchers pointed out that the LockBit ransomware group was the second most active group in Q4 despite a drop in the number of victims and its reputation due to the arrest of one of its affiliates in Canada.
Other gangs, such as the Play ransomware group grew their malicious activities by posting exfiltrated data and also targeting Swedish organizations chiefly from the transportation and logistics sector.
Emerging new groups were also noticed in Q4 of 2022, including Royal, Putin Team, Play, Qilin, Mallox, and Nokoyawa.

Amid data leaks, ransomware groups also encountered leaks due to differing affinities. Cyble noted in its Q1-2022 ransomware report that the Conti ransomware group’s source code, structure, and internal Jabber chats were leaked by an insider because certain members of Conti were not in favour of their support to Russia in the Russia-Ukraine conflict. This broke numerous personally identifiable information about the gang.
Details like the gang having around 100 members on its payroll and speculations of some being associated with the Federal Security Service (FSB) were also made.
The stagnant databases
Ransomware groups have been regrouping and rebranding themselves ultimately to revive their identity. They were at times found to be posting on their leak site and breach forums, not one but three victims or company names at once.
On one side, BlackByte ransomware group posted about a ‘New year sale’ of data from CPTM, Hayward, and KansasCityHomes. And on the other, LockBit claimed to have data from Politriz, Melody Shipping Agency Co. Ltd., and Fulfillment Matters UK.