The Karakurt extortion group is back after a hiatus, claiming two victims.
The data extortion group has claimed to have hacked US-based IT services business Officeworks and stolen the social security numbers of 150 million Americans from One Corporation.
While the authenticity of this claim is yet to be verified, companies need to strap themselves as the threat actor has been regarded as one of the most notorious extortion gangs of the last year.
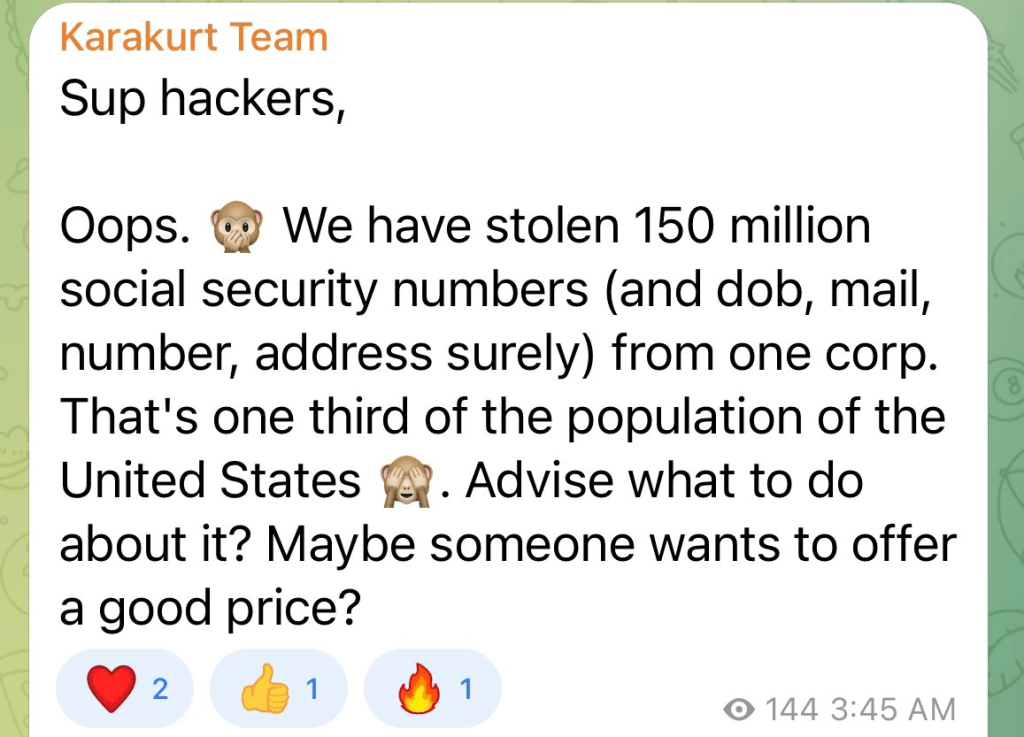
The news comes after the threat actor shared a post on its underground channels, stating, “Sup hackers, Oops. We have stolen 150 million social security numbers (and dob, mail, number, address) from one corp.
“That’s one-third of the population of the United States. Advise what to do about it. Maybe someone wants to offer a good price?”
Officeworks is an IT consulting firm that provides services to small and medium-sized businesses. Karakurt extortion group claim to have obtained access to 288GB of the company’s data.
The data reportedly includes sensitive information such as employee details, birth certificates, drivers’ licenses, financial information, tax records, as well as project and property information. The company has not yet released a statement regarding the incident.
What is Karakurt extortion group?
The Karakurt Extortion gang is a threat actor notorious for employing data theft to extort money from corporations.
The group is infamous for publicly disclosing stolen data from their victims unless a Bitcoin ransom, ranging from $25,000 to $13,000,000, is paid. Since first emerging in June 2021, the group has been active in North America and Europe.
The Karakurt actors typically provide screenshots or copies of the stolen file directories to demonstrate their possession of the stolen data.
The group has also resorted to harassing emails and phone calls to pressure the victims, their employees, business partners, and clients into complying with their demands.
These emails contain sensitive data, including social security numbers, payment accounts, private company emails, and confidential business data belonging to employees or clients.
Once the ransom is paid, Karakurt actors reportedly delete the files and occasionally provide brief explanations for the initial intrusion.
Until January 5, 2022, the Karakurt group operated a leaks and auction website, http[s] [:] //karakurt[.] group. However, the domain and IP address of the website went offline in the spring of 2022.
Although the website is no longer accessible on the open internet, it has reportedly surfaced on the deep and dark web.
The website contains several terabytes of stolen data from North America and Europe victims. Also, it features press releases naming uncooperative victims and instructions for participating in victim data auctions.
The Karakurt extortion group’s modus operandi
After gaining entry or developing access to a compromised system, the Karakurt actors use various tactics such as deploying Cobalt Strike beacons to scan a network.
Then it installs Mimikatz to extract plain-text credentials, utilizes AnyDesk to secure long-term remote control, and implement other tools based on the situation to elevate privileges and move laterally within the network.
It then compresses the exfiltrated data (typically using 7zip) and send large volumes of them, often exceeding 1 terabyte (TB), through open-source applications, file transfer protocols such as Filezilla, and cloud storage services like rclone and Mega.nz.
As per cybersecurity experts, the Karakurt Extortion group operates as a notorious Conti ransomware gang subgroup.
Karakurt extortion group and the Conti connection
Conti, a pro-Russian ransomware group, was one of the highly prolific threat groups in the recent past.
The ransomware group’s demise is believed to be linked to the Russia-Ukraine war, although it is not clear whether it was the direct cause or simply a contributing factor.
Just four days after the war’s official start, an insider leaked tens of thousands of internal chat logs, revealing the group’s size, structure, and day-to-day operations.
The leak, which included the source code of Conti ransomware, put the final nail in the coffin. Security researchers soon discovered a connection between Conti ransomware and the Karakurt extortion group.
It was found that Karakurt is a side business of the Conti syndicate to make money from unsuccessful encryption attacks.
When Conti’s ransomware payload is blocked and the attack doesn’t enter the encryption stage, the already exfiltrated information is released as Karakurt for data extortion. Arctic Wolf, a cybersecurity company, confirmed this finding in a report.
They discovered during an investigation of a client who had previously paid Conti to unlock their data that the client was later breached by Karakurt through a Cobalt Strike backdoor that Conti had left behind.
The research from Arctic Wolf was a collaboration between its computer security service Tetra Defense, cybersecurity company Northwave, and blockchain analysis firm Chainalysis.
Chainalysis’ investigation revealed several Karakurt wallets that sent cryptocurrency to wallets controlled by Conti. The researchers found that payments from victims ranged from $45,000 to $1 million.
The blockchain analytics company also found Karakurt victim payment addresses hosted by a Conti wallet, indicating that both gangs are managed by the same party.