Premier Italian winery Cantina Tollo has disclosed a malicious cyber attack. The announcement came close on the heels of LockBit ransomware gang claiming Cantina Tollo as a victim.
On January 30, 2023, an unknown threat actor struck the company, leaving it to mitigate the damage.
In the last few days we have been doing everything necessary to fix the situation in order to avoid further consequences on the privacy and security of the personal data of our customers and our company,” said the company announcement.
Following that event, necessary measures were put in place to remedy possible violations of personal data.
The Cyber Express has reached out to Cantina Tollo regarding the said cyber attack and is yet to receive a response from them.
Cantina Tollo data breach explained
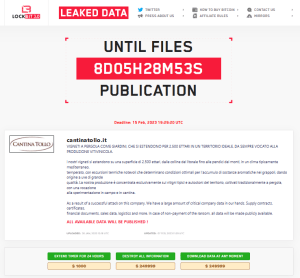
The LockBit ransomware gang posted a threat note on its leak site on Tuesday, February 7, hours before the company disclosed the incident. However, the company disclosure does not mention that it was a ransomware attack.
According to the threat note, the data was accessed on January 30, the day of attack mentioned in the company disclosure. The ransomware gang threatens to publish the data if ransom is not Paid by February 15.
In a bid to negotiate, the ransomware gang has put a $1000 bill to extend the deadline by 24 hours. To destroy the data, the gang has asked for a payment of $249,999.
Ironically, the gang has asked for the same amount for downloading the data.
Cantina Tollo, ransomware, and attack mitigation
Cantina Tollo claims to have taken swift action in response to the attack, including disabling and separation of the impacted systems from its network.
“These measures, while involving the interruption of some services for a limited period of time, are necessary to avoid the increasing of the the consequences of the attack,” said the company disclosure.
Being an Italian company, the company is bound to make the disclosure as per the guideline outlined in Article 34 of the EU Regulation 2016/679 (GDPR).
Cantina Tollo is known for its sprawling vineyards spanning 2,500 hectares, producing wine only from the indigenous and signature grapes of the area, grown in the temperate Mediterranean climate.
LockBit ransomware gang: Mode of operation
The LockBit ransomware gang operates through a mode of encrypting and exfiltrating files on targeted devices, then demanding a ransom payment for their return.
Their latest strain, LockBit 3.0, is also known as LockBit Black and was first discovered in September 2019. It primarily targets organizations with the ability to pay large ransom amounts and has the ability to self-propagate.
LockBit 3.0, discovered in late 2022, has retained most of its previous functionality and added new behaviors, making it harder to analyze.
It may require an affiliate to enter a 32-character password to launch the ransomware binary. The typical attack process involves infecting the device, encrypting files, deleting services, and altering the wallpaper.
Failure to pay the ransom may result in the sale of the stolen data on the dark web. LockBit 3.0 is known to exploit Windows Defender to deploy Cobalt Strike and cause a chain of malware infections.
The LockBit group operates as a Ransomware-as-a-Service model, collaborating with affiliates who may not have the necessary resources for an attack.
According to a December 2022 alert by the U.S. Department of Health & Human Services, a portion of the ransom payment goes back to the affiliated hacker.