The Iran Telegram malware campaign has once again put the spotlight on how state-backed cyber actors are adapting their tactics by blending into widely used digital platforms. In a recent alert, the Federal Bureau of Investigation (FBI) revealed that cyber actors linked to Iran’s Ministry of Intelligence and Security (MOIS) are using Telegram as a command-and-control (C2) infrastructure to deploy malware.
The campaign specifically targets Iranian dissidents, journalists, and individuals or groups perceived as opposing the Iranian government. According to the FBI, these operations have led to intelligence collection, data leaks, and reputational damage, indicating that the intent goes beyond simple access and leans toward sustained monitoring and impact.
Iran Telegram Malware Reflects Targeted Surveillance Strategy
The Iran Telegram malware activity dates back to at least Fall 2023, with multiple malware variants identified targeting Windows systems. The victim profile is not random. It is clearly defined, focused on individuals whose views or affiliations are seen as a threat by the Iranian government.
However, the FBI also notes that the malware can be used against any individual of interest, suggesting the capability is broader than the currently observed targets.
What stands out is the level of preparation. The malware is not just deployed, it is tailored. Attackers appear to study their targets in advance, customizing lures to increase the chances of success. This points to a deliberate and intelligence-driven approach rather than opportunistic attacks.
How the Iran Telegram Malware Operates
The FBI outlines a structured, multi-stage malware framework that combines deception with persistence.
Social Engineering Drives Initial Access
Attackers reach out through messaging platforms, impersonating trusted contacts or even technical support. Victims are persuaded to download files disguised as legitimate applications.
These files often appear as commonly used software, including messaging tools or utilities, making them harder to question.
Multi-Stage Malware Deployment
- Stage 1: Masquerades as legitimate applications such as Telegram-related tools, KeePass, or other software
- Stage 2: Installs a persistent implant after user interaction
Once executed, the second stage connects the infected device to a Telegram bot, establishing a C2 channel via Telegram’s infrastructure.
Persistent Access and Control
At this stage, attackers gain remote access to the compromised system. The use of Telegram allows bidirectional communication, enabling continuous control without raising immediate suspicion.
Data Collection and Exfiltration via Telegram
The primary objective of the Iran Telegram malware campaign is data collection. The malware is capable of:
- Recording screen activity and audio
- Capturing cached data and files
- Compressing and staging data for exfiltration
- Deleting files after extraction
Some variants were even designed to record screen and audio during active Zoom sessions, highlighting a focus on capturing sensitive, real-time information.
All collected data is routed through Telegram infrastructure, reinforcing its role as a central component of the attack chain.
Links to Handala Hack and Proxy Operations
The FBI also connects this campaign to the online entity “Handala Hack,” which claimed responsibility for a 2025 hack-and-leak operation targeting individuals critical of Iran.
The agency assesses that some of the leaked data was obtained using malware associated with this campaign. Handala Hack is known for phishing, data theft, extortion, and destructive cyber activities, including the use of wiper malware.
Additionally, the group is linked to “Homeland Justice,” another entity assessed to be operated by MOIS cyber actors.
This reflects a broader pattern where technical intrusions are followed by public data exposure. The goal is not just access, but also reputational and political damage through controlled information release.
Execution Techniques and Persistence Mechanisms
The malware used in the Iran Telegram malware campaign employs several techniques to maintain access and avoid detection:
- Use of PowerShell execution without warnings
- Registry modifications to ensure persistence
- Deployment of multiple malware files for different functions
Observed file names include variants mimicking legitimate tools, such as Telegram_authenticator.exe and WhatssApp.exe, further reinforcing the deception strategy.
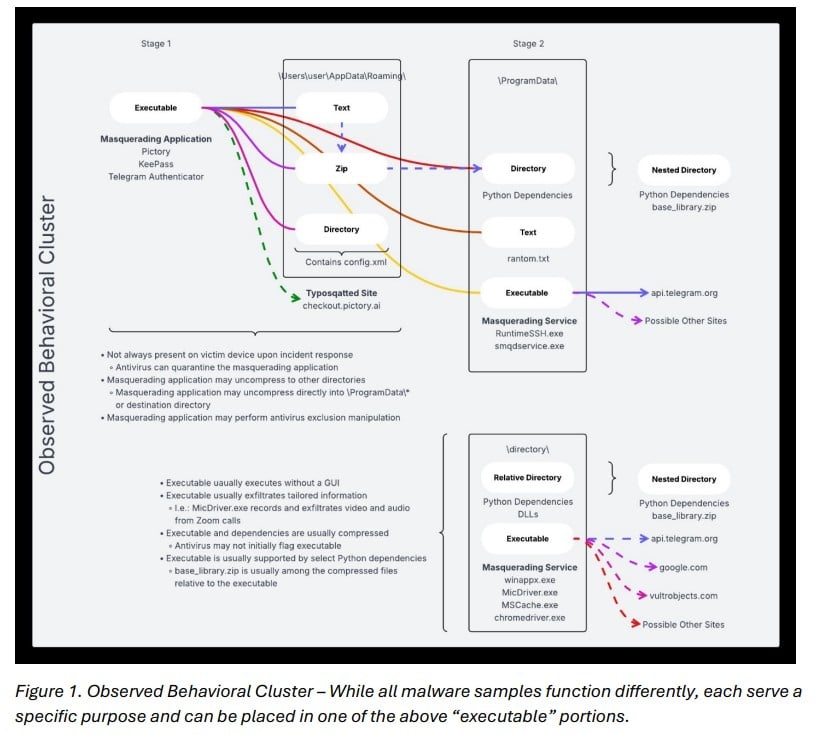
Once inside a system, additional malware components are downloaded to expand capabilities and maintain long-term access.
Why This Campaign Stands Out
What makes the Iran Telegram malware campaign particularly concerning is its simplicity combined with precision.
- It relies heavily on human interaction rather than technical exploits
- It uses trusted platforms instead of suspicious infrastructure
- It focuses on specific individuals rather than mass attacks
This combination makes detection harder and increases the likelihood of success.
Mitigation- Simple Steps, Critical Impact
Despite the sophistication of the campaign, the FBI’s recommendations remain grounded in basic cybersecurity practices:
- Be cautious of unexpected messages, even from known contacts
- Avoid downloading files from unverified sources
- Keep systems updated with the latest software patches
- Use strong passwords and enable multi-factor authentication
- Regularly run antivirus or anti-malware tools
The advisory makes one thing clear: even advanced campaigns often succeed because of small lapses in user awareness.
A Clear Signal for Cyber Defenders
The Iran Telegram malware campaign is a reminder that cyber threats are no longer confined to obscure or easily identifiable channels. By embedding malicious activity within widely used platforms like Telegram, attackers are reducing friction and increasing stealth.
For defenders, this raises an important challenge, security strategies must account not just for malicious code, but for how and where that code is delivered.
In this case, the platform is familiar. The method is simple. And that is exactly what makes it effective.