The reported Crunchyroll data breach has sparked debate across the anime streaming community, not just because of the alleged scale, but because of how it may have occurred. Early claims suggested a compromise through a third-party access point, a well-known weak link in modern digital ecosystems.
However, new statements from Crunchyroll, shared with The Cyber Express team, indicate that the situation may be more limited than initially reported.
While the full picture remains unclear, what has emerged so far paints a technically plausible and troubling scenario involving outsourced systems, internal tooling, and the kind of data aggregation that makes streaming platforms attractive targets.
What Crunchyroll Has Confirmed
Crunchyroll has now provided a more measured and important clarification with The Cyber Express team, stating, “Our investigation is ongoing, and we continue to work with leading cybersecurity experts. At this time, we believe that the information is primarily limited to customer service ticket data following an incident with a third-party vendor. We have not identified evidence of ongoing access to systems in relation to these claims.”
This statement significantly narrows the likely scope of the incident:
- The exposure appears primarily limited to customer service ticket data
- The incident is linked to a third-party vendor
- There is no evidence of ongoing system access
- The investigation is still ongoing
What Actually Happened in the Crunchyroll Cyberattack
According to early reports first shared by International Cyber Digest on X, the data breach at Crunchyroll may date back to March 12, 2026. A threat actor reportedly gained access to internal systems and exfiltrated nearly 100GB of data.
The attack was initially described as originating through a third-party vendor, where an employee allegedly executed malware on their system, unintentionally granting access to internal tools such as a ticketing system. From there, large volumes of customer analytics and support data were reportedly extracted.
These claims, however, remain unverified.
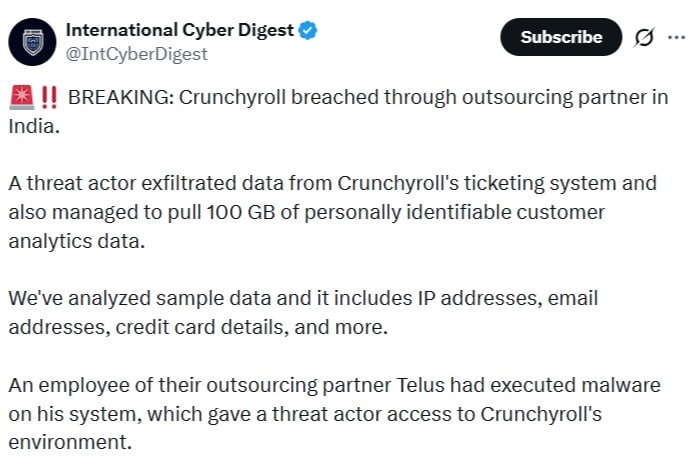
The breach is said to have originated through an outsourcing partner. Specifically, claims indicate that an employee at this third-party vendor executed malware on their system, unintentionally granting the attacker access to Crunchyroll’s internal environment. From there, the attacker reportedly accessed a ticketing system and extracted large volumes of customer analytics and support data.
Another detail emphasizes that this dataset includes IP address data alongside other identifiers, reinforcing concerns about user profiling and tracking.
What Data May Have Been Exposed
Based on both initial reports and the company’s statement, the most plausible exposure involves user-submitted support data, which may include:
- Email addresses
- IP addresses
- Messages sent to customer support
- Potentially sensitive information users voluntarily shared (e.g., account details, partial payment info)
Importantly, support tickets are unstructured, meaning users sometimes include sensitive data in plain text—something that structured systems are designed to avoid.
There is currently no confirmed evidence that full payment systems or encrypted credential databases were breached.
Why the Third-Party Angle Matters
Even with a narrower scope, the incident reinforces a major cybersecurity reality: third-party vendors remain a critical risk surface.
If the breach did originate from a vendor endpoint:
- A single compromised system may have enabled access to internal tools
- Security controls may vary significantly across partner organizations
- Incident response becomes more complex due to shared responsibility
This aligns with a broader industry trend in which attackers target vendors rather than primary systems.
Real-World Risks for Anime Streaming Users
Even if the Crunchyroll data breach is limited in scope, the type of data allegedly exposed carries real risks.
Email addresses and IP data alone can be leveraged for:
- Phishing campaigns targeting anime streaming users
- Credential stuffing attacks using reused passwords
- Behavioral profiling, when combined with older leaked datasets
If passwords were exposed in any form, the risk escalates further, especially for users who reuse credentials across services.
Credit card exposure, even partial, adds another layer of concern. While incomplete data is less immediately exploitable, it can still be used in social engineering or brute-force attempts in combination with other leaks.
Community Reaction Reflects Uncertainty
Online discussions reveal a mix of confusion and cautious concern. Some users question what “credit card details” actually means, whether full numbers were exposed or just fragments. Others point out that payments made through intermediaries like app stores are likely safer due to tokenization, which prevents merchants from directly storing card data.

There is also a broader sentiment that security practices across anime streaming platforms need to evolve. Several users stress the importance of two-factor authentication (2FA), with some arguing that it should be mandatory.
What Users and Security Teams Should Do Next
In situations like this, the Crunchyroll cyberattack, users should act defensively:
- Change your Crunchyroll passwords immediately
- Avoid reusing passwords across services
- Monitor financial statements for unusual activity
- Be cautious of phishing emails posing as Crunchyroll communications
For organizations, the incident reinforces a familiar but often overlooked lesson: third-party risk management is not optional. Vendor access, endpoint security, and data handling policies must be treated as core components of the security architecture, not afterthoughts.
Updated: A Crunchyroll spokesperson shared details of the data breach to The Cyber Express. The story has been updated with the new information.




















































