In a startling turn of events, a thriving fashion brand based in Hanoi, Vietnam, known as “The Bad God,” has become the unfortunate victim of a data breach. The Bad God data breach has been claimed by a user of the hacker forum and not a prominent threat actor group.
What sets this breach apart is the boldness with which the data has been advertised on a hackers’ forum.
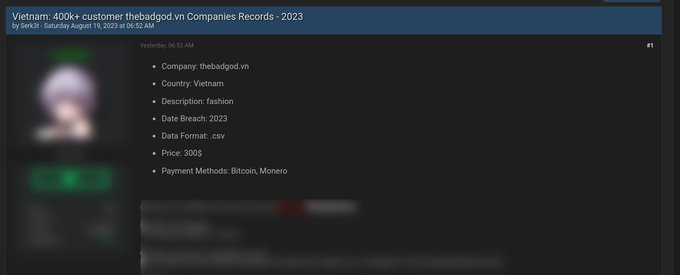
A user by the name “Serk3t” has stepped forward, presenting a treasure trove of over 400 thousand customer records, all reportedly sourced from The Bad God data breach.
The Bad God data breach explained
The Bad God, recognized for its edgy and street-inspired fashion creations, has its roots deeply embedded in the vibrant fashion scene of Vietnam.
Operating from its online platform at http://thebadgod.vn, the brand has successfully curated a niche market of individuals drawn to its aesthetically pleasing designs.
The breached data spans 2023 and is up for grabs in a .CSV format, and the price tag attached to this data trove is a mere $300.
Notably, the cybercriminal behind this The Bad God data breach has specified two cryptocurrency payment methods – Bitcoin and Monero – to facilitate the exchange of funds for sensitive data.
To learn more about the authenticity of The Bad God data breach, The Cyber Express has reached out to the fashion brand.
However, at the time of writing, no official response or statement had been received, leaving the claims made by “Serk3t” for The Bad God data breach unverified.
Regrettably, The Bad God data breach is not an isolated incident in the fashion industry
.Fashion has become an attractive target for cybercriminals recently, with other prominent brands falling prey to similar attacks.
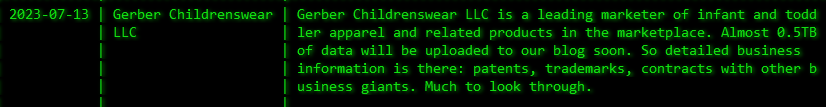
The Cyber Express previously reported a comparable incident involving the Akira ransomware group. This time, their target was Gerber Childrenswear, another esteemed fashion brand.
The Bad God data breach and the rise of cyber attacks on the fashion industry
In a striking resemblance to The Bad God data breach, the Akira ransomware group claimed responsibility for infiltrating Gerber Childrenswear’s servers. The hacker group declared access to data of over 500GB of the company’s confidential information.
However, The Bad God data breach and the Gerber Childrenswear breach aren’t the only dark clouds looming over the fashion industry’s security incidents.
Earlier this year, in January 2023, a fashion industry data breach saw threat actors pilfer the personal information of a staggering 10 million customers of the renowned fashion retailer JD Sports.
These cybercriminals penetrated JD Sports’ data infrastructure, gaining access to a database encompassing purchase records from 2018 to 2020.
The compromised data included personal details such as full names, delivery and billing addresses, email addresses, phone numbers, and the last four digits of payment cards.
In a separate yet equally concerning incident in March 2023, an Australian fashion house, Not A Man’s Dream, faced backlash for featuring Arabic text representing “Allah” on its garments during the Melbourne Fashion Festival.
The controversy erupted into distributed denial-of-service (DDoS) attacks, orchestrated by Islamic hacktivist groups, against numerous Australian institutions and businesses. These retaliatory actions responded to what the hacktivists perceived as a “disgraceful display” of religious texts.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.