By exploiting anomalies in certificate-based TGT (Ticket Granting Ticket) requests, cyber attackers are able to gain unauthorized access and potentially elevate their privileges within the targeted system.
Forged certificates for unauthorized access
Forged certificates can fool Key Distribution Center (KDC) to gain access to the company’s network.
The Securelist blog stated, “An example of such an attack is the Shadow Credentials technique, which lets an attacker sign in under a user account by modifying the victim’s msDS-KeyCredentialLink attribute and adding an authorization certificate to it,” addressing how hackers modify information to gain unauthorized access.
After conducting experiments in this area, researchers developed a Proof-of-Concept that could find artifacts in the Active Directory (AD) for a counter-attack mechanism.
Authentication of users based on tickets
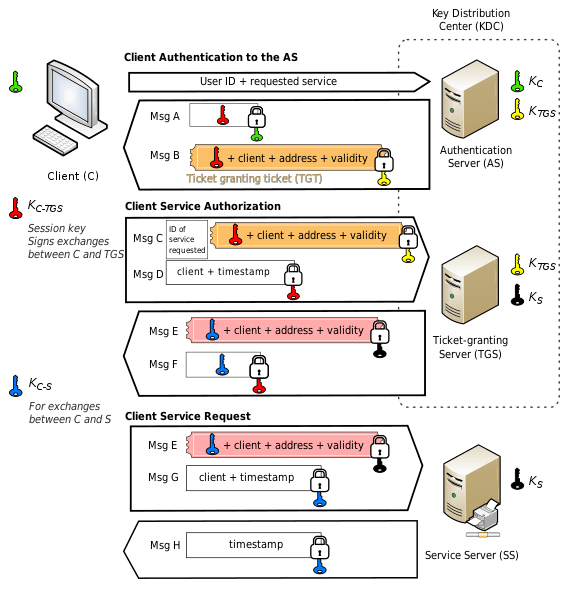
In corporate networks based on Active Directory, resources are managed via Kerberos protocol.
Only the users providing a service ticket issued by the KDC are granted access. This ticket is issued by the KDC component called the Ticket Granting Server (TGS).
Users are issued TGS tickets from the KDC if they have a Ticket Granting Ticket (TGT) as shown in the graphics above.
Some users could gain the TGT without the password by using certificates for authentication. The KDC checks the certificates which must relate to the subject mentioned in the TGT.
“This part of Kerberos, called Public Key Cryptography for Initial Authentication (PKINIT), makes it quite easy to set up authentication if there is a (Certificate Authority) in the corporate network that issues certificates for domain users.”
Cyber attack with user authentication
If a user who has written permissions for any attribute in the AD writes a public key using the Whisker tool, they will get the TGT.
Whisker tool allows manipulating the msDS-KeyCredential attribute to add shadow credentials to the user account.
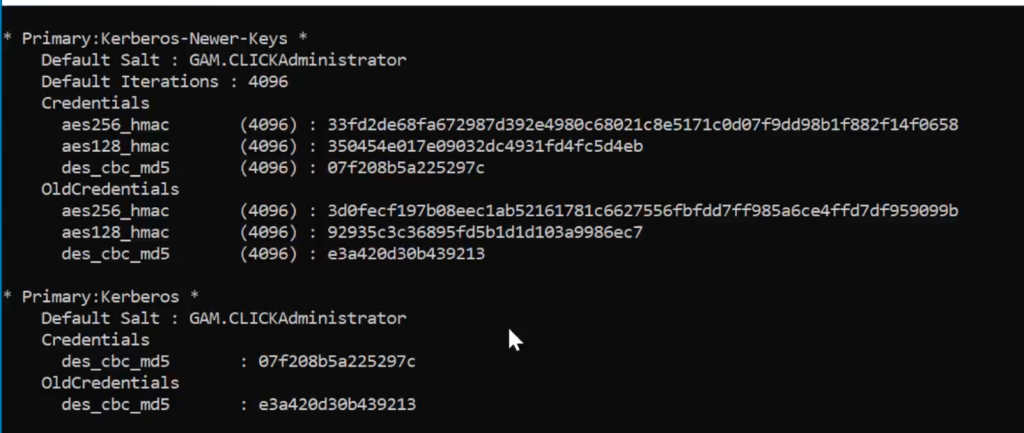
The hacker could use the TGT to get the TGS ticket and edit password data in the domain and synchronize the hash from the domain administrator account. They can then have admin privileges and move laterally across networks causing a DCSync attack using mimikatz.
Upon issuing the TGT, Event 4768 gets triggered on the domain controller stating that a Kerberos authentication ticket (TGT) was requested. In this event, one may find artifacts from forged certificates for authentication.
The artifacts may contain information from the following fields –
- CertIssuerName
- CertSerialNumber
- CertThumbprint
With Logstash having information about how to change the bit fields of Event 4768 to values specific to a ticket, detection becomes faster.
To make the process smoother, the Securelist blog added, “This also makes the search much faster and smoother. I recommend using the handy set of Docker configurations to get your ELK lab up and running quickly. Plus the official WinLogBeat setup guide.”
Test-based results involving forged certificates
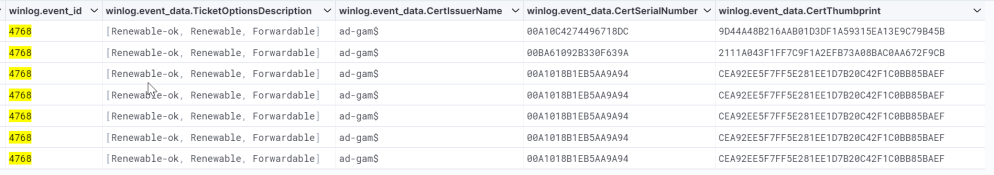
Researchers created several TGT requests through forged certificates using Whisker. It was found that several events were about certificate-based ticket requests for Microsoft Azure Active Directory.
A script could be added to Kibana to find all the 4768 events showing from case-insensitive matches between CertIssuerName and TargetAccountName.
It was found that if a host is known to the system by multiple names, the KDC may offer Service Principal Names with mapping data while retrieving the credentials. Making the process hazardous to security, it was found that if the “Canonicalize” option was set, the KDC can edit the names and SPNs of the client and the server.
It was also concluded that if the msDS-KeyCredentialLink attribute has a DeviceID in GUID format and there was no object with the ID in the domain, that would mean a red flag for security.






















































