A New York-based organization that serves groups advocating the rights of individuals with cerebral palsy and other disabilities has been targeted by the LockBit ransomware group. The hackers gave a deadline of 6 days for ransom payment. The CP State cyberattack threat was updated by LockBit on 16 October, 2023 however, the organization has made no formal statements on any security incident.
CP State is a non-profit organization that provides education and advocacy services to disability service agencies in New York.
CP State Cyberattack by LockBit
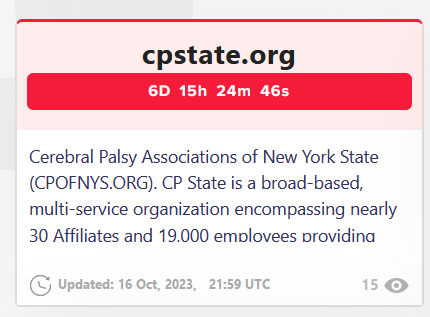
The CP State ransomware attack post had received 15 views on the dark web when it was captured by Falcon Feeds, the Threat Intelligence platform.
If LockBit’s claim about the Cerebral Palsy State cyberattack is to be believed, the security breach is likely to impact the 30 affiliates, 19,000 employees, and over 100,000 individuals it serves and keeps a record of.
The amount of data or the ransom demanded by LockBit after the CP State cyberattack could not be ascertained at the time of writing.
The Cyber Express emailed the organization for comments regarding the alleged CP State cyberattack. We will update this report upon receiving a response from them.
Falcon Feeds tweeted that hackers will publish the organization’s data on October 23, 2023.
LockBit, Civilian Hackers and IHL Rules
In one incident, LockBit offered a free decryptor and an apology stating that they have a policy against targeting healthcare. They launched a cyberattack on SickKids a children’s hospital in Canada earlier in January 2023. Thereafter, they apologized on behalf of a partner in their group who launched the SickKids cyberattack.
The partner was removed from the group.
While civilian hackers are urged to abide by the eight rules under the International Humanitarian Law, financially motivated cybercriminals go on a rampage extorting money from any entity they find. One of the eight rules in the guidelines says that they should not target medical and humanitarian facilities.
They are also to avoid targeting civilian infrastructure, public services, and civilian data.
Civilian hackers and hacktivists are expected to follow the eight rules that carry out operations in the context of an armed conflict. “The most egregious violations of these rules constitute war crimes, which may be prosecuted nationally or internationally,” read a blog by the International Committee of the Red Cross (ICRC).
It is for this reason the ICRC called on States to let civilians know of the consequences of participating in military cyber operations for their nation.
“The more civilian hackers engage in cyber operations, the greater the risk of operations that violate applicable law and blur the line between combatants and civilians,” the ICRC blog further added.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.




















































