Cl0p ransomware continues listing victims, with Siemens Energy, a prominent European energy giant, in its latest list of victims.
The ransomware gang claimed the cyber attack on Siemens Energy and four other organizations including Schneider Electric and the University of California Los Angeles.
Upon learning of the alleged Siemens Energy cyber attack, The Cyber Express promptly reached out to the company for confirmation.
In response, Siemens Energy spokesperson, Claudia Nehring, stated, “Regarding the global data security incident, Siemens Energy is among the targets. Based on the current analysis, no critical data has been compromised and our operations have not been affected. We took immediate action when we learned about the incident.”
With over 91,000 employees in more than 90 countries, Siemens Energy AG is considered one of the world’s largest energy technology companies.
The Cyber Express is yet to confirm whether the attack is executed using the MOVEit vulnerability. Coincidentally, Cl0p ransomware executed a cyber attack on Siemens Energy’s competitor Hitachi energy, tapping another MFT vulnerability.

Cyber attack on Siemens Energy: Cl0p’s claim
Siemens Energy has a dedicated in-house ProductCERT team responsible for handling all security-related matters pertaining to their products, solutions, and services. Despite the seriousness of the situation, the ProductCERT team has not released any statements or updates regarding the alleged cyber attack on Siemens Energy.
The Cl0p ransomware gang, believed to be responsible for the attack on Siemens Energy, has been wreaking havoc on various organizations in recent weeks.
Just last Sunday, intelligence analyst Dominic Alvieri disclosed a list of new victims that had fallen prey to this malicious group. The companies and websites mentioned were ENZO.COM, LANDAL.COM, DELAWARELIFE.COM, UHCSR.COM, and NAVAXX.LU, HEIDELBERG.COM, and many others.
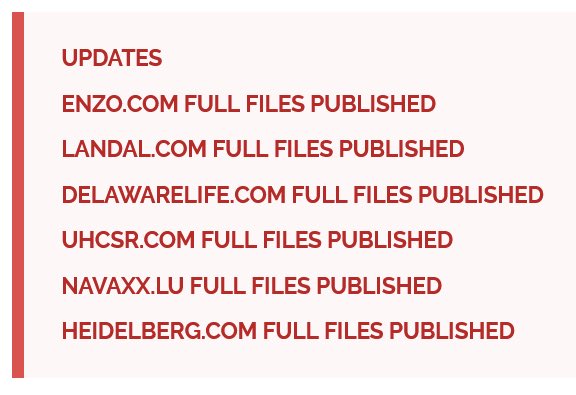
The Cl0p ransomware gang asserted that it had obtained data from these victims and had made it available as a data dump on its data leak site.
Cyber attack on Siemens Energy: Energy infrastructure troubles
Cyber attacks targeting the energy industry have reached an alarming frequency, with the Siemens Energy cyber attack merely scratching the surface of a pervasive problem.
Since 2017, these attacks have been on a rapid rise, culminating in a record-breaking number of incidents in 2022. A newly published study by DNV sheds light on the frequency of hackers targeting the energy sector and how investment in cybersecurity has increased over the years.
According to the study, six out of ten energy professionals have reported that their organizations are boosting cybersecurity spending in 2023. However, experts advise that the current cybersecurity budgets must be increased.
According to a survey conducted by DNV, the majority (59%) of the 600 energy professionals polled confirm increased investment in cybersecurity compared to the previous year. They acknowledge that cyber attacks on the industry are not a matter of “if” but “when.”
Moreover, two-thirds (64%) of respondents believe that their organization’s infrastructure is now more vulnerable than ever to cyber threats, prompting a heightened focus on cybersecurity due to geopolitical tensions.
Six out of ten industry professionals affirm that cybersecurity is now a regular topic on the boardroom agenda, and a significant majority (77%) confirm that it is treated as a business risk within their organizations.
The overwhelming consensus (89%) among energy professionals is that cybersecurity is an essential prerequisite for the industry’s digital transformation initiatives and is crucial for its future sustainability.
Media Disclaimer: This report is based on internal and external research obtained through various means. The information provided is for reference purposes only, and users bear full responsibility for their reliance on it. The Cyber Express assumes no liability for the accuracy or consequences of using this information.





















































