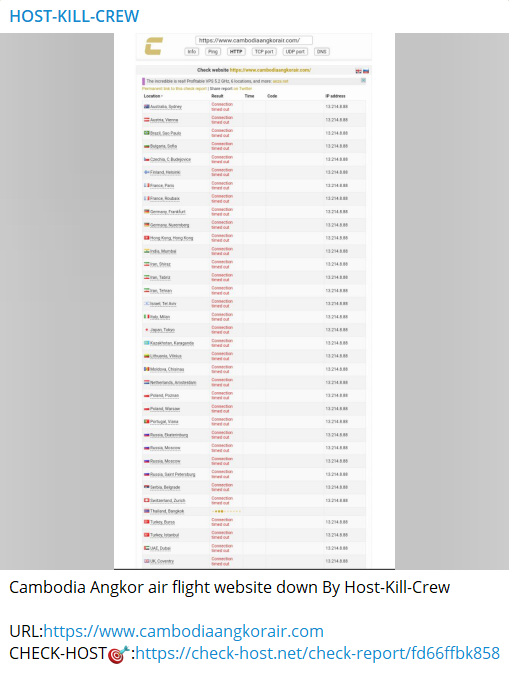
A lesser-known hacker group, which calls itself Host Kill Crew, has taken responsibility for the Cambodia Angkor Air cyber attack.
The group posted details of the attack on their leak site which was likely a Distributed Denial of Service attack to halt the online services for a while.
The website of the carrier, which went inaccessible for some time on 9 May, is operational now.
The Cambodia Angkor Air cyber attack
“Host Kill Crew hackers group claims to have targeted the website of Cambodia Angkor Air, the national flag carrier airline of Cambodia. Note: website is down at the moment,” Threat Intelligence service Falcon Feeds tweeted on 9 May.
The Cyber Express emailed the airlines to inquire about the alleged Cambodia Angkor Air cyberattack. We are yet to receive a confirmation about the same.
Cambodia has been clocking a rise in the number of air transport and passengers carried in recent years. The revenue of Cambodia Angkor Air in the flight segment is expected to touch nearly $132.60 million in 2023.
The airlines flew 1.13 million air travelers in only the initial 8 months of 2022. The hackers likely wanted to make a profit from the growing airline’s income and launched the DDoS attack. The airlines may look forward to a Compound Annual Growth Rate of 3.6% (CAGR) between 2023-2027.
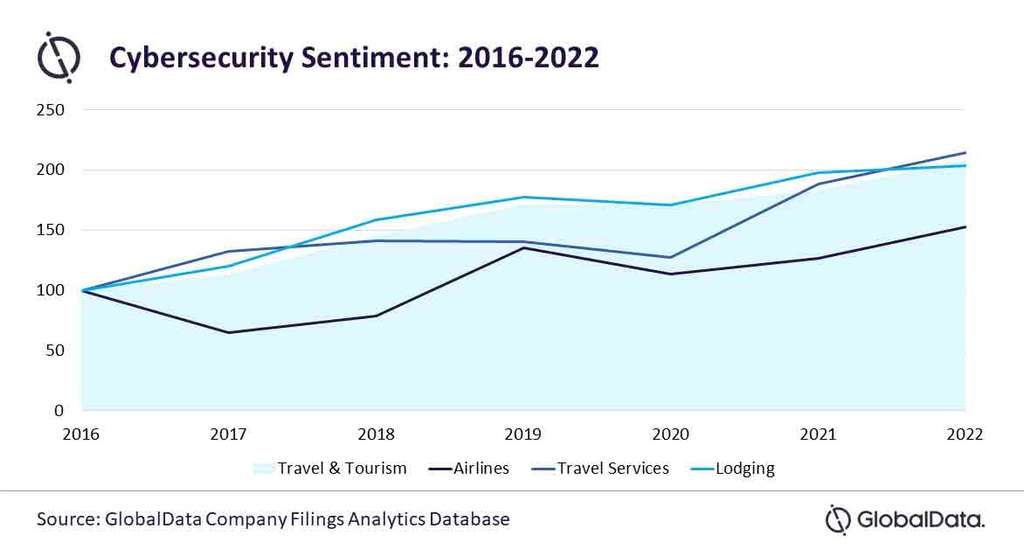
According to a Hospitality Net report, there has been a steady rise in cybersecurity incidents in the travel and tourism sector including airlines between 2016 and 2022. Although airlines are well trained in maintaining due diligence in terms of safety and security, cybersecurity needs to be maintained with just as much caution.
Speaking about the impact of cyber incidents on airlines, Misa Singh, Business Fundamentals Analyst at GlobalData wrote: “A severe data security incident can lead to operational disturbances and cause significant financial damage to the business.”
Cambodia Angkor Air cyber attack: Latest in the list
With several porous access points, from faulty airport WiFi to unsecured third-party booking websites, aviation sector has been an easy target for cyber attackers.
Nok Air, a low-cost Thai airline, was hit by a ransomware attack in March. The attackers used the LockBit ransomware to encrypt Nok Air’s systems and demand a ransom payment.
The leaked data included passport and ID card scans of Nok Air customers, employee data, and financial documents.
Nok Air issued a statement acknowledging the attack and urging customers to be cautious about any unsolicited communications claiming to be from the airline.
In early January, Air Albania, the national flag carrier airline of Albania, suffered a ransomware attack by the LockBit group.
The attackers encrypted Air Albania’s systems and demanded a ransom payment in exchange for the decryption key. Air Albania did not disclose whether they paid the ransom or not.
It turns out that attackers can access the network of a carrier mid-flight! In August 2021, security researchers discovered a critical vulnerability in the in-flight Wi-Fi service of several major airlines, including American Airlines, United Airlines, and Singapore Airlines.
The bug, identified as a remote code execution vulnerability, could allow an attacker to take control of the in-flight Wi-Fi system and potentially access the personal information of passengers or disrupt the aircraft’s avionics systems.
The common perception of increased security at the higher levels of executive access — privileged users — is false, as witnessed by the hacking of Pegasus Airlines. The had about 6.5TB of sensitive data stolen by hackers that it came to know about when researchers notified them in March 2022.
The reported reason behind the İstanbul, Türkiye-based airline Pegasus cyberattack was failure to configure the cloud environment by a system administrator.
Privileged users hold the keys to your organization’s critical infrastructure and sensitive data, which is why they can deal great insider threat damage to your organization,” noted a report by cybersecurity software vendor Ekran System.
While it is imperative to keep systems secure from unauthorized access, a report also reiterated on the need to be cautious when using public Wi-Fi at airports that lack enough security measures.
Merely trusting free internet while traveling may lead to cyberattacks and exposing sensitive information to hackers waiting to hack unsuspecting travellers.